Cyber Attack Lifecycle Timeline: 8 Powerful Stages Explained
The Cyber Attack Lifecycle Timeline helps organizations understand how modern cyber attacks unfold from start to finish. Rather than happening instantly, most attacks progress through structured stages.
Understanding the Cyber Attack Lifecycle Timeline allows security teams to:
- Detect threats earlier
- Reduce dwell time
- Contain incidents faster
- Improve response metrics
This guide explains each stage step-by-step and shows how it connects to measurable security benchmarks.
Table of Contents
What Is a Cyber Attack Lifecycle Timeline?
A Cyber Attack Lifecycle Timeline is a structured breakdown of how attackers move through a system after identifying a target.
It maps the attacker journey from:
Reconnaissance → Access → Expansion → Impact.
This model closely aligns with the MITRE ATTACK framework.
It also connects directly to detection and response metrics such as:
- Mean Time to Detect (MTTD)
- Mean Time to Contain (MTTC)
- Mean Time to Respond (MTTR)
- Dwell Time in Cybersecurity
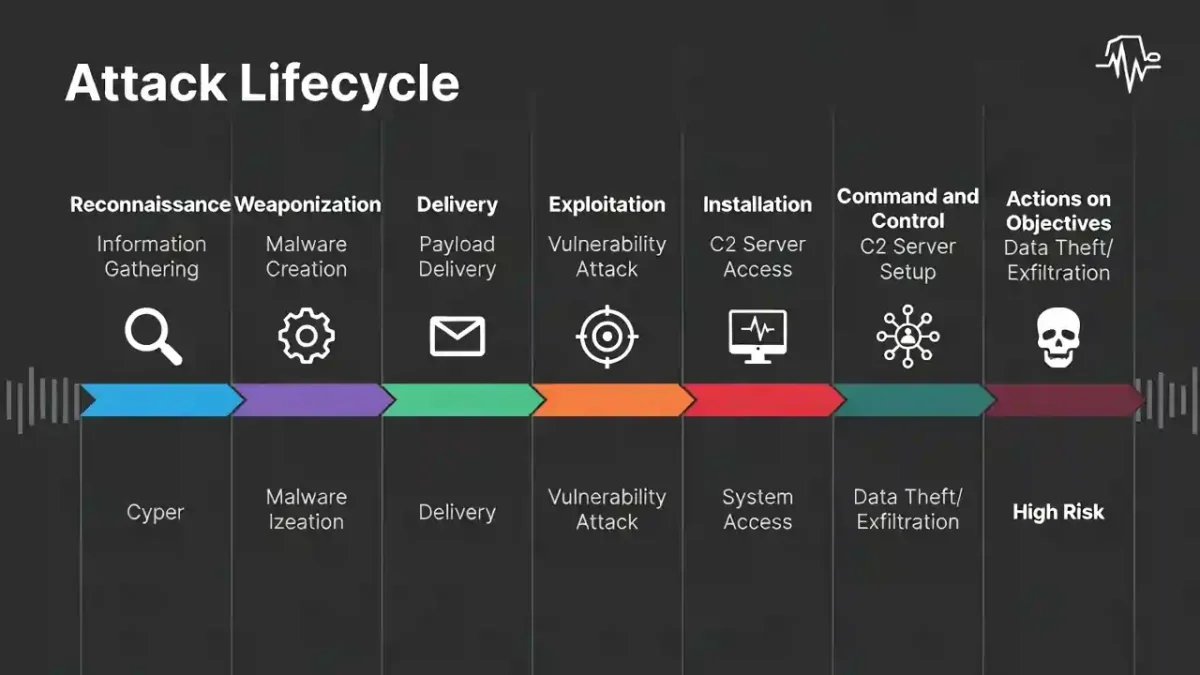
Stage 1: Reconnaissance in the Attack Lifecycle
Attackers begin by gathering information about the target.
Activities include:
- Scanning networks
- Identifying exposed services
- Harvesting email addresses
Early detection at this stage significantly reduces risk.
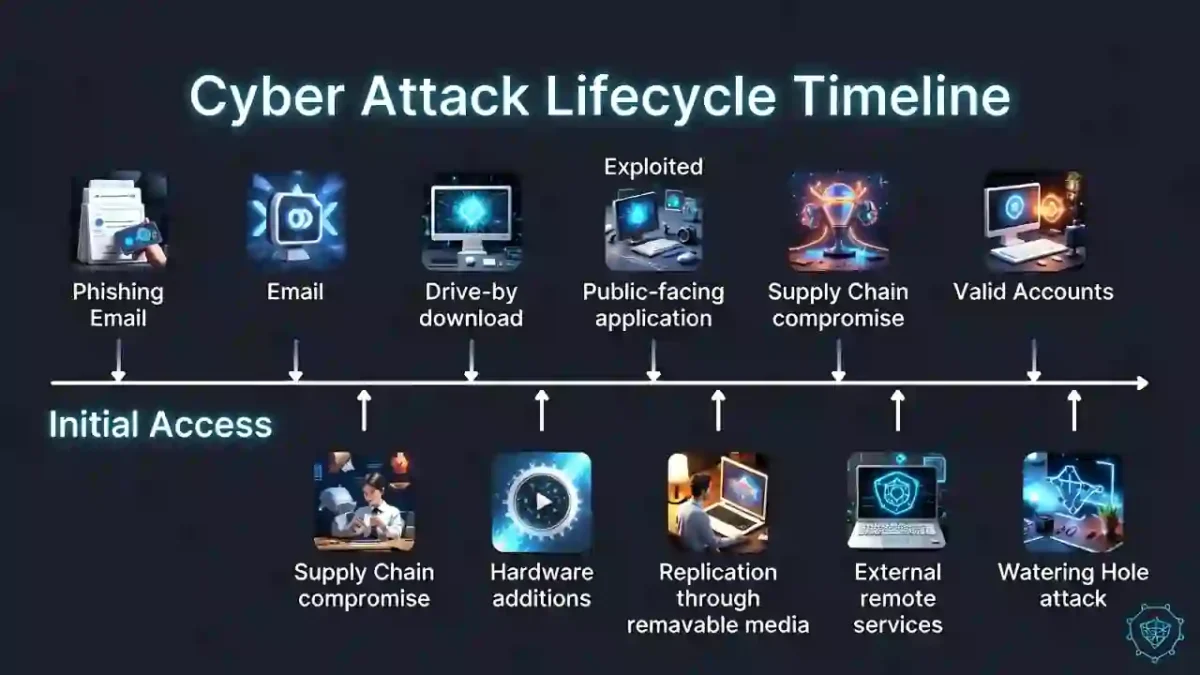
Stage 2: Initial Access
This is where the attacker gains entry.
Common methods:
- Phishing
- Credential stuffing
- Exploiting vulnerabilities
Avoid Social Engineering and Phishing Attacks
Strong identity controls reduce successful entry attempts.
Stage 3: Execution
Malicious code runs inside the environment.
Examples:
- Malware deployment
- Script execution
- Remote command control
Improving: MTTD
Reduces attacker progress.
Stage 4: Persistence
Attackers ensure continued access.
Methods include:
- Scheduled tasks
- Registry changes
- Backdoor accounts
Continuous monitoring limits long-term compromise.
Stage 5: Privilege Escalation
Attackers attempt to gain administrative control.
Techniques:
- Credential dumping
- Exploiting privilege flaws
Stopping escalation prevents lateral expansion.
Stage 6: Lateral Movement
Attackers move across systems to reach critical assets.
🌍 External NIST Incident Handling Guide
Network segmentation and anomaly detection reduce this risk.
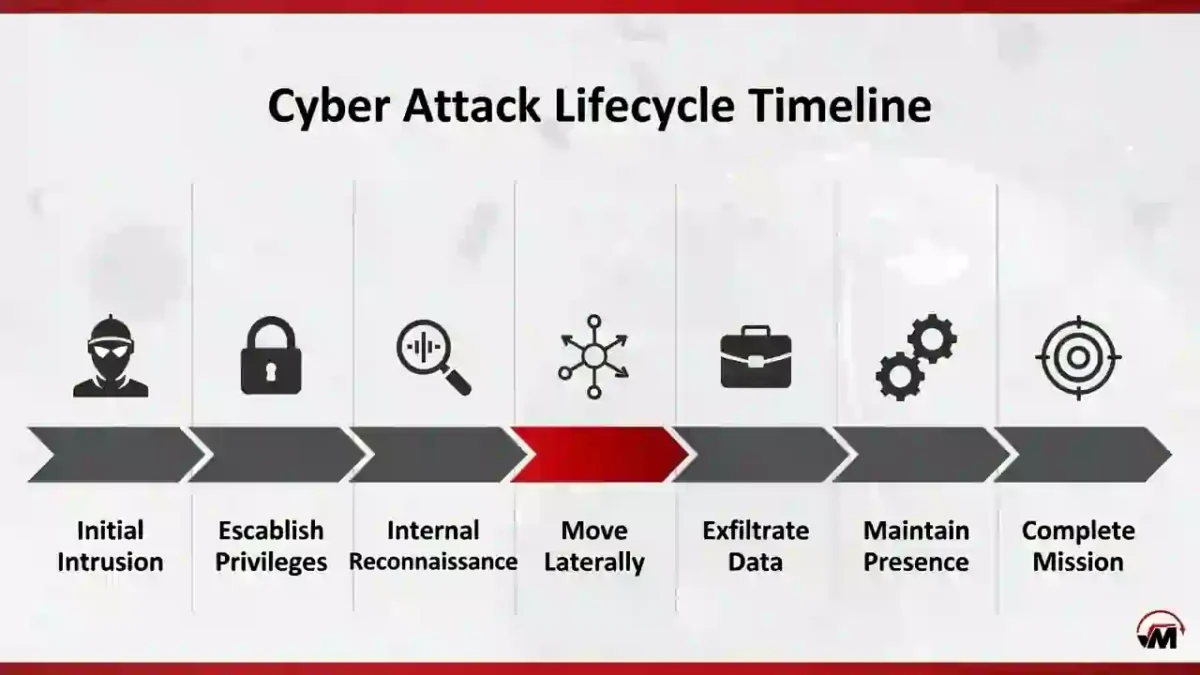
Stage 7: Data Exfiltration
Sensitive data is collected and removed.
Indicators:
- Unusual outbound traffic
- Large encrypted uploads
Reducing: Dwell Time: 5 Proven Ways to Reduce Risk
Minimizes exposure.
Stage 8: Impact
The final stage of the Cyber Attack Lifecycle Timeline is visible damage.
Examples:
- Ransomware
- Downtime
- Data leaks
Faster containment improves: Mean Time to Contain MTTC
Efficient recovery strengthens: Mean Time to Respond (MTTR)
How Security Metrics Align With the Attack Lifecycle
| Stage | Key Metric |
|---|---|
| Compromise | Dwell Time |
| Detection | MTTD |
| Containment | MTTC |
| Recovery | MTTR |
For a full benchmark comparison:
🔗 Link MTTD vs MTTR vs MTTC vs Dwell Time
Why the Attack Lifecycle Model Matters
The Cyber Attack Lifecycle Timeline transforms security from reactive defense into measurable performance.
Organizations using this framework can:
- Reduce detection delays
- Improve containment speed
- Limit operational disruption
- Strengthen long-term resilience
Final Thoughts
The Cyber Attack Lifecycle Timeline provides clarity in a complex threat landscape. By understanding each stage, organizations can build layered defense systems that detect earlier, contain faster, and recover efficiently.
Security maturity begins with visibility into the full attack progression.


