6 Critical Reasons Cyber Attacks Go Undetected
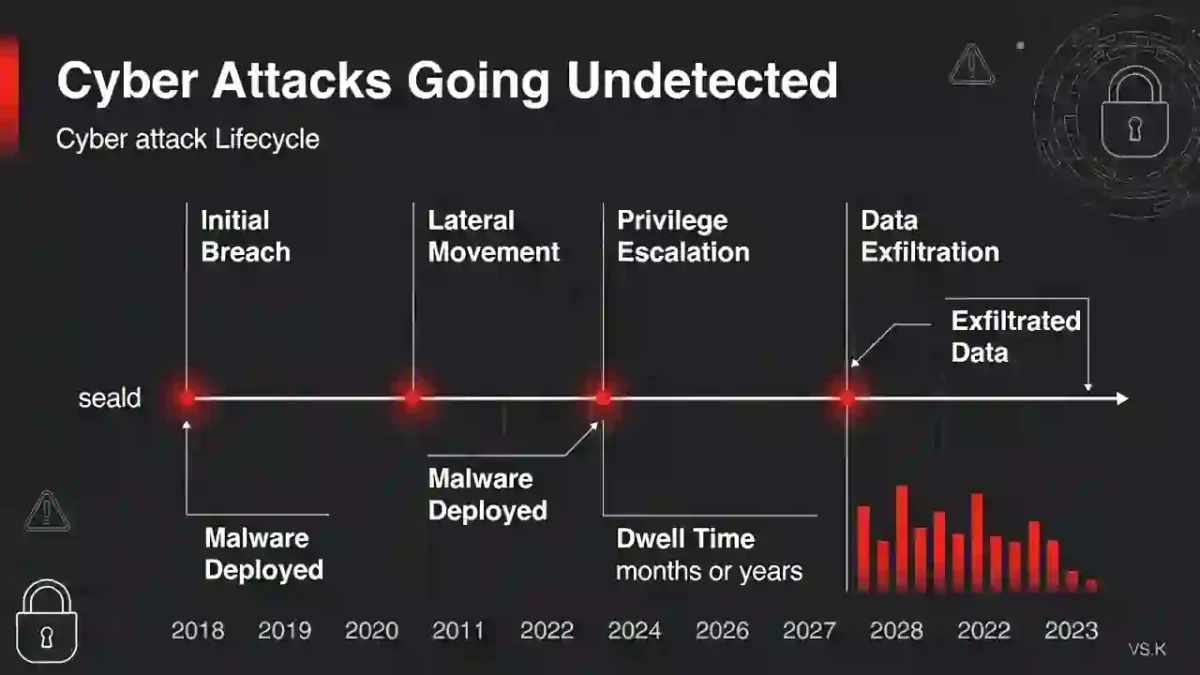
Cyber attacks rarely happen in a single moment. Instead, they unfold quietly over days or even weeks.
In many cases, organizations do not detect breaches immediately. Attackers gain time to escalate privileges, move laterally, and access sensitive systems before security teams respond.
Understanding why cyber attacks go undetected is essential for improving detection speed and reducing long-term impact.
Why Cyber Attacks Go Undetected in Modern Networks
Understanding why cyber attacks go undetected is the first step toward improving detection maturity.
Table of Contents
1️⃣ Lack of Continuous Monitoring
Many organizations lack true 24/7 monitoring.
Without real-time oversight, attackers operate during nights, weekends, or holidays without immediate detection.
Continuous monitoring significantly reduces:
🔗 Link: Mean Time to Detect (MTTD)
When monitoring gaps exist, detection delays grow.
2️⃣ Alert Fatigue in Security Teams
Security analysts often face thousands of alerts daily.
This creates:
- Investigation backlogs
- Delayed response
- Missed high-priority signals
Alert fatigue is a major contributor to delayed breach discovery.
Automation and smarter filtering improve detection accuracy.
3️⃣ Visibility and Logging Gaps
Cyber attacks go undetected when visibility is incomplete.
Common blind spots include:
- Cloud misconfigurations
- Unmonitored endpoints
- Third-party vendor access
- Insufficient log retention
Without full telemetry, attackers remain hidden longer.
For deeper insight into dwell time:
🔗 Link: Dwell Time in Cybersecurity
4️⃣ Delayed Incident Escalation
Sometimes detection happens — but escalation fails.
Alerts may be:
- Misclassified as low severity
- Delayed due to staffing shortages
- Trapped in approval workflows
These internal process delays extend containment timelines.
For performance benchmarks:
🔗 Link: Industry Benchmarks 2026
5️⃣ Misconfigured Security Tools
Security solutions require constant tuning.
Outdated rules and improper configurations create silent failures. Tools may be deployed but not optimized.
Security effectiveness depends on configuration quality, not just tool presence.
6️⃣ Advanced Evasion Techniques
Modern attackers intentionally avoid detection.
They use:
- Living-off-the-land binaries
- Encrypted command-and-control channels
- Low-and-slow lateral movement
- Credential abuse
These techniques are documented in:
🌍 External Link: MITRE ATT&CK Framework
Understanding these tactics explains why detection delays still occur.
How to Reduce Undetected Attack Windows
Organizations can shorten detection time by:
- Implementing 24/7 monitoring
- Deploying endpoint detection and response (EDR)
- Automating alert prioritization
- Conducting red team exercises
- Improving escalation workflows
Aligning detection improvements with the attack lifecycle strengthens resilience.
🔗 Link: Cyber Attack Lifecycle Timeline
Final Thoughts
Cyber attacks go undetected when visibility, monitoring, escalation, and configuration weaknesses combine.
Reducing detection time requires more than tools — it requires operational maturity, automation, and continuous benchmarking.
Organizations that invest in monitoring and response processes dramatically reduce dwell time and limit breach impact.