SEC Cyber Incident Disclosure Checklist: 7 Critical Costly Rule Errors
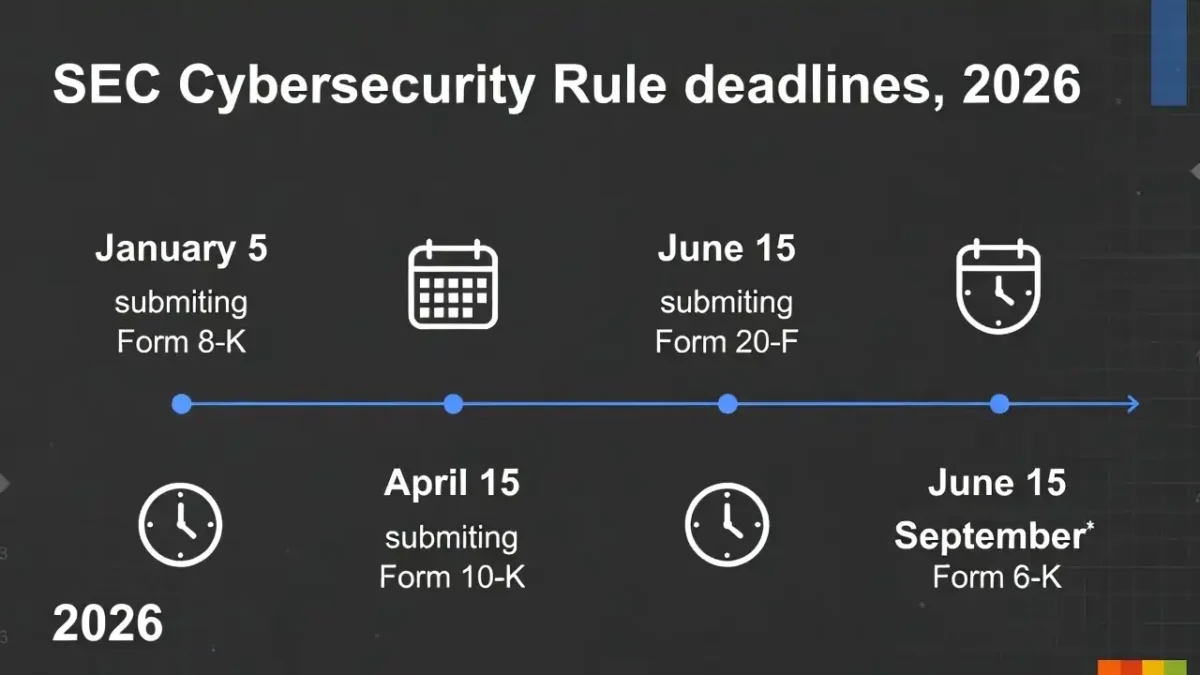
A practical SEC Cyber Incident Disclosure Checklist can make the difference between an organized response and a rushed disclosure process. For US public companies, the SEC’s 4-business-day disclosure rule has made cybersecurity reporting a legal, operational, and board-level concern.
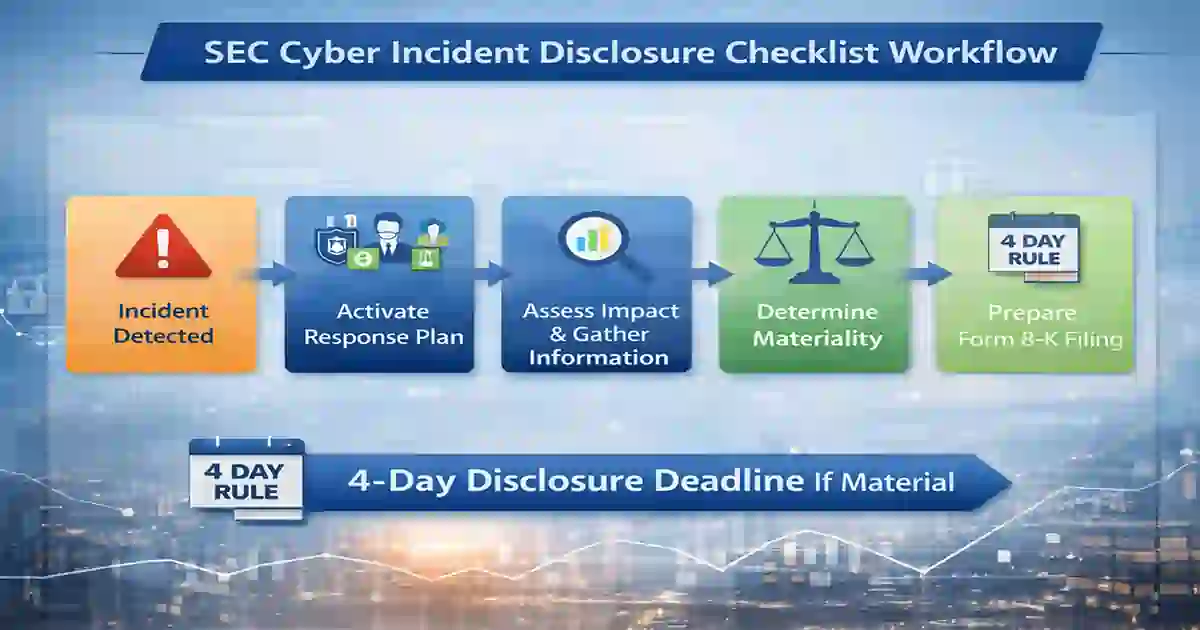
When a cyber incident happens, most teams focus first on containment, recovery, and technical investigation. That is expected. But for public companies, another question becomes just as urgent: has the incident become material, and if so, is the company ready to disclose it on time?
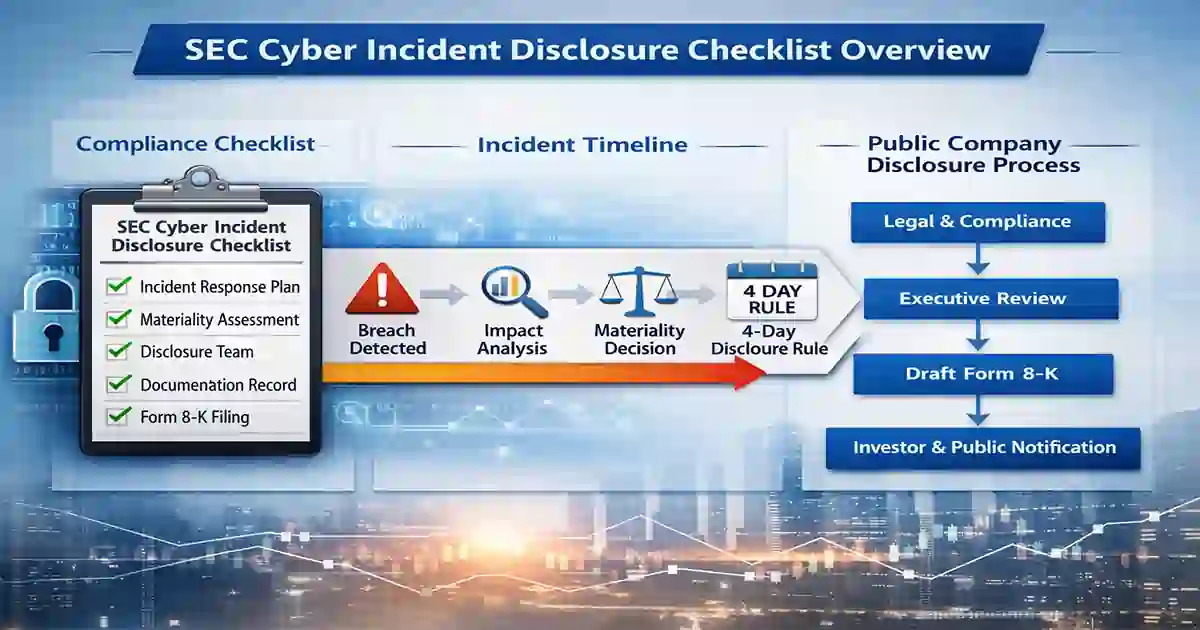
That is where a strong SEC Cyber Incident Disclosure Checklist becomes useful. It gives legal, compliance, security, investor relations, and executive teams a repeatable process for escalation, review, documentation, and disclosure.
This guide breaks the issue into practical steps so your team can move with more confidence, reduce delay, and avoid costly disclosure mistakes.
Table of Contents
What the 4-business-day rule means
The SEC rule does not require a company to disclose every cybersecurity event. It requires disclosure of a material cybersecurity incident, and the filing obligation begins after the company determines that the incident is material.
That timing creates confusion for many organizations. The clock does not necessarily begin when the attack starts or even when it is first discovered. It starts when the company reaches a materiality determination.
In real-world situations, that can be the hardest part of the process. Security teams may have partial technical facts. Legal teams may still be evaluating exposure. Executives may want more certainty before authorizing a public statement. Without a clear internal process, valuable time can disappear.
A well-built SEC Cyber Incident Disclosure Checklist helps solve that problem by setting out who needs to be involved, what facts must be gathered, how materiality should be reviewed, and how the filing timeline should be tracked.
If your team is still improving its broader incident handling process, you can also review Cybersecurity Incident Response Timeline for a more operational view of how response phases fit together.
Why this checklist matters
Cyber incidents rarely unfold in a neat, predictable sequence. Facts change. Scope expands. Business impact may be unclear in the first several hours. Security teams often work from logs, alerts, and forensic indicators while executives need concise explanations and decisions.
Without a checklist, companies often run into the same issues:
- legal is involved too late
- materiality discussions are informal
- key facts are scattered across teams
- disclosure drafting starts too close to deadline
- internal and external statements do not align
- documentation is too weak to explain timing later
A practical SEC Cyber Incident Disclosure Checklist reduces confusion by turning a legal requirement into a working internal process. It also improves governance. Cybersecurity is no longer viewed as only an IT problem. Boards, regulators, and investors increasingly expect visible oversight and disciplined response planning.
For that broader governance angle, you can internally link to Board-Level Cybersecurity Metrics Guide.
You can also link to Incident Response Deadlines US UK for readers who want to compare cyber reporting timelines across jurisdictions.
SEC Cyber Incident Disclosure Checklist
Use this SEC Cyber Incident Disclosure Checklist as a practical framework before, during, and after a potentially material cybersecurity incident.
1. Confirm your incident response plan includes SEC disclosure triggers
Many incident response plans are written mainly for technical responders. They cover containment, eradication, recovery, and evidence preservation. Those points matter, but they are not enough for a public company.
Your incident response plan should clearly explain:
- when legal must be notified
- when executive leadership must be brought in
- who owns the materiality assessment
- who drafts and reviews Form 8-K language
- how the four-business-day timeline will be tracked once materiality is determined
If those steps are missing, your company may lose time exactly when timing matters most.
This is also a natural place to add an internal link to How to Reduce Cybersecurity Detection Time, because faster detection and escalation make timely disclosure more realistic.
2. Identify the internal disclosure team in advance
A cyber incident with possible disclosure consequences should never remain isolated within the security or IT team. Public company disclosure requires a coordinated, cross-functional response.
That team often includes:
- General Counsel
- CISO or security lead
- CFO
- CEO or delegated executive sponsor
- investor relations lead
- communications or PR lead
- privacy or compliance lead
- outside counsel, when needed
This part of the SEC Cyber Incident Disclosure Checklist should be settled before any incident occurs. In a live event, no one should be wasting time deciding who owns the next decision.
3. Gather the right facts early
You do not need every fact to begin a serious materiality review. What you need is a consistent way to collect the facts most likely to matter.
Document early facts such as:
- when the incident was detected
- which systems, business units, or assets are affected
- whether sensitive data may be exposed
- whether operations have been disrupted
- whether customers, vendors, or partners may be affected
- what remains uncertain
- what containment actions are already underway
This helps legal and executive teams begin evaluating significance without waiting for a perfect forensic picture.
One common problem during incident response is delay caused by uncertainty. A company keeps waiting for full clarity, even though early decisions still need to be made.
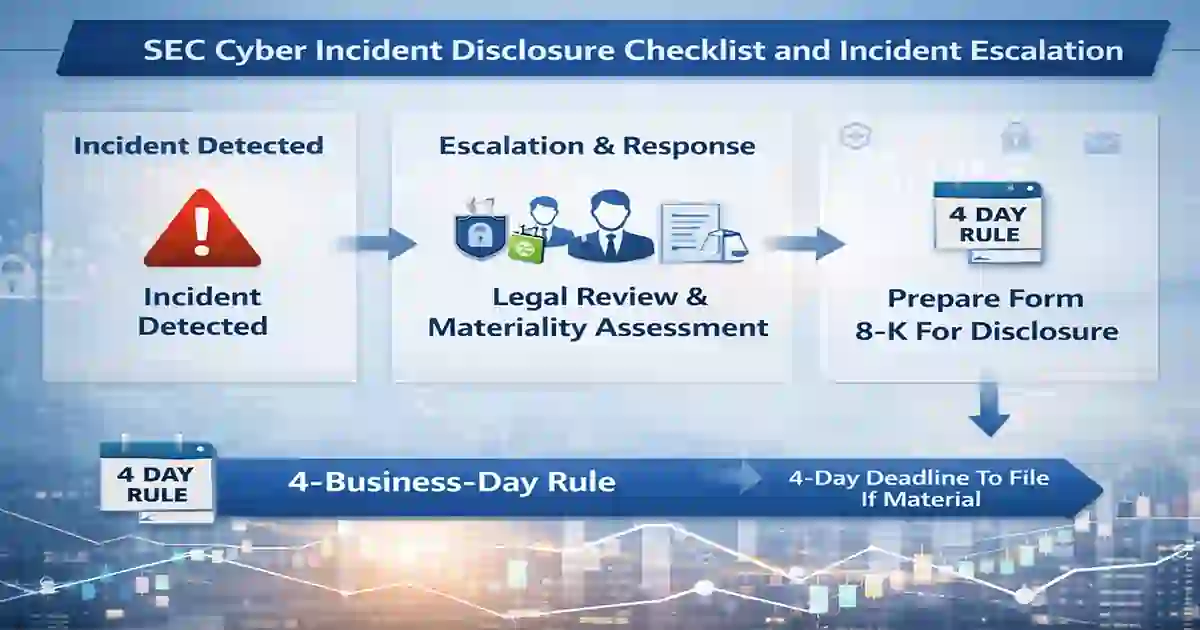
4. Use a documented materiality review process
This is the core of the SEC Cyber Incident Disclosure Checklist.
Materiality is not just about immediate financial loss. A cybersecurity incident may be material because of business interruption, reputational damage, customer impact, litigation exposure, regulatory risk, or harm to critical operations.
A good materiality review should ask questions like:
- Could this incident affect financial condition or operating results?
- Has it disrupted a core business function?
- Could it lead to customer loss or reputational harm?
- Is there a realistic chance of regulatory scrutiny or litigation?
- Would a reasonable investor likely consider the event important?
The answer usually does not depend on one factor alone. What matters is that the review is timely, cross-functional, and documented.
5. Record when the materiality determination is made
Once the company determines that an incident is material, the disclosure clock starts.
That means your internal process should clearly record:
- who participated in the decision
- what facts were considered
- what conclusion was reached
- when the decision was made
- what uncertainties still remained at that time
This part of the SEC Cyber Incident Disclosure Checklist is essential. If your timeline is questioned later, that documentation may become one of the most important records in the entire response file.
6. Draft the Form 8-K carefully
After materiality is determined, the company needs to move quickly but carefully. The disclosure should be accurate, understandable, and limited to what is known.
In most cases, the company should be ready to describe:
- the nature of the incident
- the scope of the incident
- the timing of the incident, if known
- the material impact or reasonably likely material impact
This is not the place for dramatic language or technical overload. Investors need useful information, not a highly technical incident report written for forensic teams.
For related site content, you can internally link to the Compliance & Reporting category page, since it naturally supports readers interested in cyber reporting obligations.
7. Align SEC disclosure with broader communications
Once a material cyber incident becomes public, multiple groups will be paying attention at the same time. That usually includes investors, employees, regulators, customers, partners, media, and the board.
That is why the final step in an SEC Cyber Incident Disclosure Checklist is alignment.
Your company should review and coordinate:
- Form 8-K language
- customer notices
- executive talking points
- board updates
- internal employee communications
- public statements
- regulatory messaging
Mixed messages create confusion and unnecessary risk. A coordinated approach helps the company stay credible while the situation is still developing.
For broader technical and governance context, you can add external links to trusted sources such as the SEC cybersecurity disclosure final rule, NIST Incident Response, and NIST SP 800-61 Rev. 3.
7 critical costly rule errors
Even well-prepared organizations can make avoidable mistakes under pressure. Here are the seven biggest ones.
1. Treating the incident as only a security issue
Security teams are essential, but disclosure risk cannot be managed by technical teams alone. Public company cyber incidents require legal, executive, financial, and communications input.
2. Waiting too long to assess materiality
Some organizations wait for complete certainty before starting a materiality review. That often compresses the timeline and increases the risk of a rushed filing.
3. Failing to document internal decisions
A company may make the right call but still create risk if it cannot later show how and when the decision was made.
4. Using vague disclosure language
Generic language may seem safer, but it often raises more questions than it answers. Disclosures should be careful, factual, and useful.
5. Ignoring the role of response speed
Detection time and response speed matter more than many teams realize. Faster identification of business impact makes it easier to escalate, assess, and disclose on time. This is a natural place to add another internal link to Mean Time to Respond.
6. Failing to align communications
If customer notices, board briefings, media comments, and SEC disclosures do not line up, the company creates confusion and unnecessary legal risk.
7. Treating disclosure readiness as a one-time task
A checklist is only useful if it is reviewed, tested, and updated. Companies should revisit the process after incidents, tabletop exercises, and governance reviews.
Final thoughts
A strong SEC Cyber Incident Disclosure Checklist gives companies something they urgently need during a live cyber event: structure.
The 4-business-day rule is manageable when an organization already knows how to escalate incidents, assess materiality, document key decisions, and coordinate accurate disclosure across legal, security, finance, and leadership teams.
It becomes much harder when those steps are being invented in real time.
For US public companies, cyber disclosure readiness is no longer optional. It is part of good governance, good compliance, and good crisis management. If your current process still depends on scattered notes, informal calls, or individual memory, now is the right time to tighten it up.
A practical SEC Cyber Incident Disclosure Checklist will not prevent a cyber incident. But it can help your company respond with much more clarity, confidence, and discipline when the disclosure timeline begins.