Average Time to Detect Cyber Attack in 2026: Latest Statistics
The average time to detect cyber attack remains one of the most critical cybersecurity metrics in 2026.
Detection speed determines:
- How much data is exposed
- How far attackers move laterally
- The final cost of the breach
- The overall recovery time
In this guide, we break down the latest breach detection time statistics, industry benchmarks, and what organizations can realistically expect.
Table of Contents
1. What Is the Average Time to Detect a Cyber Attack?
The average time to detect cyber attack refers to how long attackers remain inside a network before security teams identify the intrusion.
This metric is closely tied to:
- Mean Time to Detect (MTTD)
- Dwell time
- Incident response maturity
Organizations with advanced monitoring detect threats faster, while those without centralized visibility often experience prolonged breaches.
For a full breakdown of detection metrics, see:
🔗 Mean Time to Detect (MTTD) in Cybersecurity
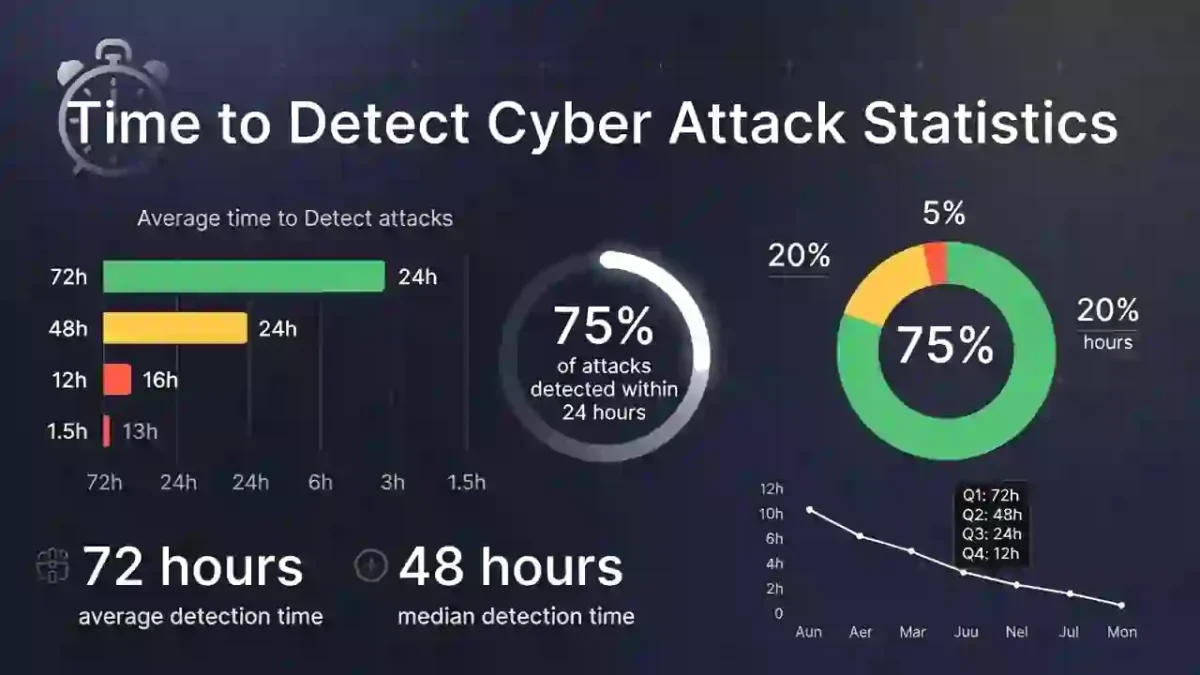
2. 2026 Breach Detection Time Statistics
Recent industry reports show:
- The global average detection time remains over 200 days in many sectors.
- Organizations with mature SOC teams reduce detection time to under 30 days.
- Automated detection tools can cut response timelines by more than 50%.
According to the IBM Cost of a Data Breach Report:
Faster detection significantly reduces total breach cost.
The Verizon Data Breach Investigations Report also confirms that early detection limits lateral movement and ransomware impact:
3. Industry-Specific Detection Benchmarks
Detection speed varies by sector.
Finance
- Typically faster detection due to strict compliance requirements.
Healthcare
- Often slower due to legacy systems.
Manufacturing
- Frequently targeted by ransomware with delayed detection.
The average time to detect cyber attack differs based on monitoring maturity and investment.
4. Why Detection Time Is Still Too High
Despite improved tools, detection delays remain common due to:
- Alert fatigue
- Lack of 24/7 monitoring
- Poor log visibility
- Understaffed security teams
- Manual investigation processes
Organizations without centralized monitoring often fail to identify threats quickly.
5. Detection Time vs Dwell Time
Dwell time refers to how long attackers remain undetected.
The longer the dwell time, the higher the breach cost.
A shortened detection window directly reduces overall damage.
For a step-by-step breakdown of how incidents unfold, see:
🔗 Cybersecurity Incident Response Timeline
6. How to Reduce Detection Time
Organizations can reduce the average time to detect cyber attack by:
- Implementing SIEM platforms
- Deploying endpoint detection tools
- Using automated threat intelligence feeds
- Running continuous monitoring
- Conducting regular security simulations
For a practical guide, read:
🔗 How to Reduce Cybersecurity Detection Time
7. Final Insights
The average time to detect cyber attack remains one of the most important cybersecurity performance indicators in 2026.
Organizations that:
- Monitor continuously
- Automate detection
- Reduce manual investigation
- Improve response workflows
… significantly limit breach damage and recovery time.
Detection speed is not just a technical metric — it is a financial and operational safeguard.


