CIRCIA 72-Hour Reporting Rule: 6 Critical Requirements
The CIRCIA 72-Hour Reporting Rule is one of the most significant federal cybersecurity requirements impacting U.S. critical infrastructure organizations in 2026.
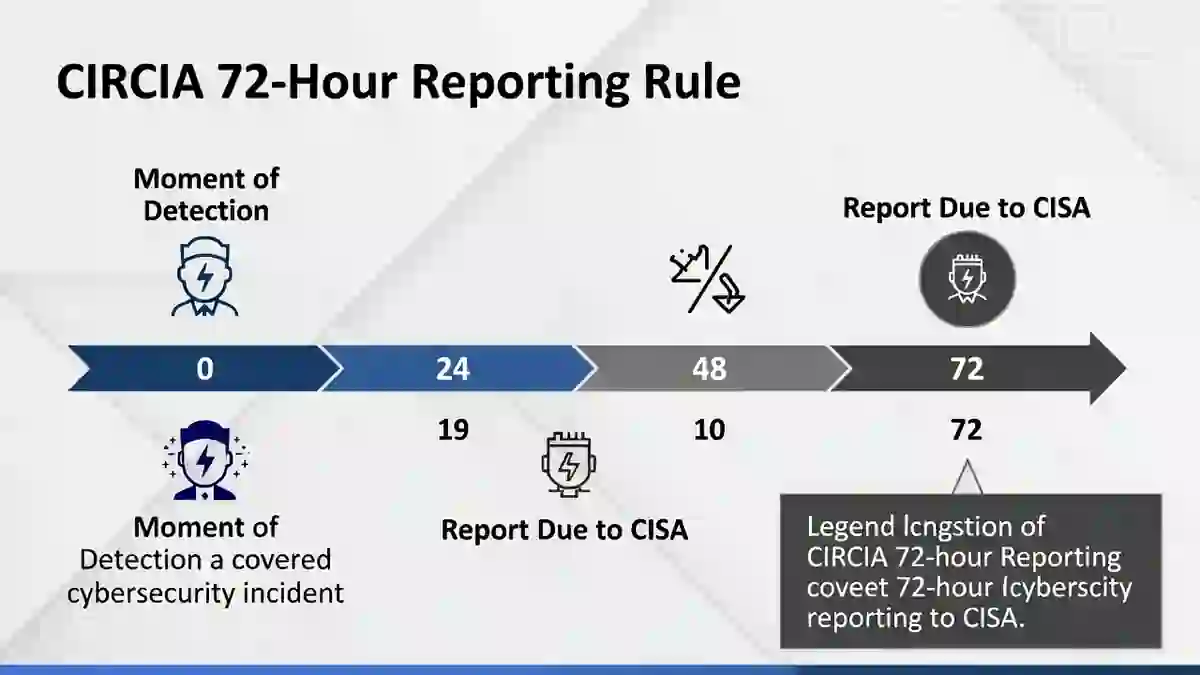
Under the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), covered entities must report substantial cyber incidents to the Cybersecurity and Infrastructure Security Agency (CISA) within 72 hours of reasonably believing the incident occurred.
In addition, ransomware payments must be reported within 24 hours.
The CIRCIA 72-Hour Reporting Rule shifts cybersecurity from operational response to regulatory obligation. Detection speed, classification accuracy, and internal coordination now directly influence compliance exposure.
Table of Contents
1️⃣ What is CIRCIA?
CIRCIA stands for the Cyber Incident Reporting for Critical Infrastructure Act.
The law was enacted to improve federal visibility into cyber threats affecting essential U.S. infrastructure.
The goal is to:
- Strengthen national cyber awareness
- Improve ransomware intelligence sharing
- Accelerate coordinated government response
The CIRCIA 72-Hour Reporting Rule ensures that federal authorities receive timely insight into major cyber disruptions.
2️⃣ Who Must Comply?
The CIRCIA 72-Hour Reporting Rule applies to covered entities operating in critical infrastructure sectors, including:
- Energy
- Healthcare
- Financial services
- Transportation
- Communications
- Water systems
Not every organization is covered. CISA defines which entities qualify.
Companies operating in multiple sectors should conduct legal review to confirm whether they fall under CIRCIA requirements.
3️⃣ What Starts the 72-Hour Clock?
Under the CIRCIA 72-Hour Reporting Rule, the clock begins when a covered entity reasonably believes a substantial cyber incident has occurred.
This is a key compliance concept.
The organization does not need full forensic confirmation. The threshold is reasonable belief.
Substantial incidents may include:
- Operational system disruption
- Significant data compromise
- Ransomware affecting critical systems
- Large-scale service outages
Delayed detection reduces flexibility in meeting the 72-hour requirement.
4️⃣ 24-Hour Ransomware Payment Requirement
CIRCIA includes an additional provision that often receives less attention.
If a ransomware payment is made, the organization must report the payment within 24 hours.
This requirement exists even if the organization has already submitted a 72-hour incident report.
The federal government uses this information to track ransomware operators and financial networks.
Failure to report payments can create additional regulatory risk.
5️⃣ Required Reporting Information
The CIRCIA 72-Hour Reporting Rule requires detailed submission including:
- Description of the incident
- Affected systems and infrastructure
- Estimated impact on operations
- Mitigation steps taken
- Ransom payment details (if applicable)
CISA may require supplemental reporting as investigations progress.
Preparation is critical. Organizations should create internal templates before incidents occur.
6️⃣ How Detection Speed Affects CIRCIA Compliance
Time-based cybersecurity metrics play a central role in CIRCIA compliance.
Key metrics include:
- Mean Time to Detect (MTTD)
- Dwell Time
- Mean Time to Respond (MTTR)
👉 MTTD Guide:
Mean Time to Detect (MTTD)
👉 Dwell Time Explained:
Dwell Time
Long dwell time reduces the effective reporting window.
For example:
If attackers remain undetected for 10 days, the organization may have only limited time to investigate before reaching the 72-hour federal deadline after reasonable belief.
Faster detection provides more time for:
- Legal review
- Incident classification
- Regulatory coordination
- Executive approval
Under the CIRCIA 72-Hour Reporting Rule, detection speed is no longer just a performance metric — it is a compliance safeguard.
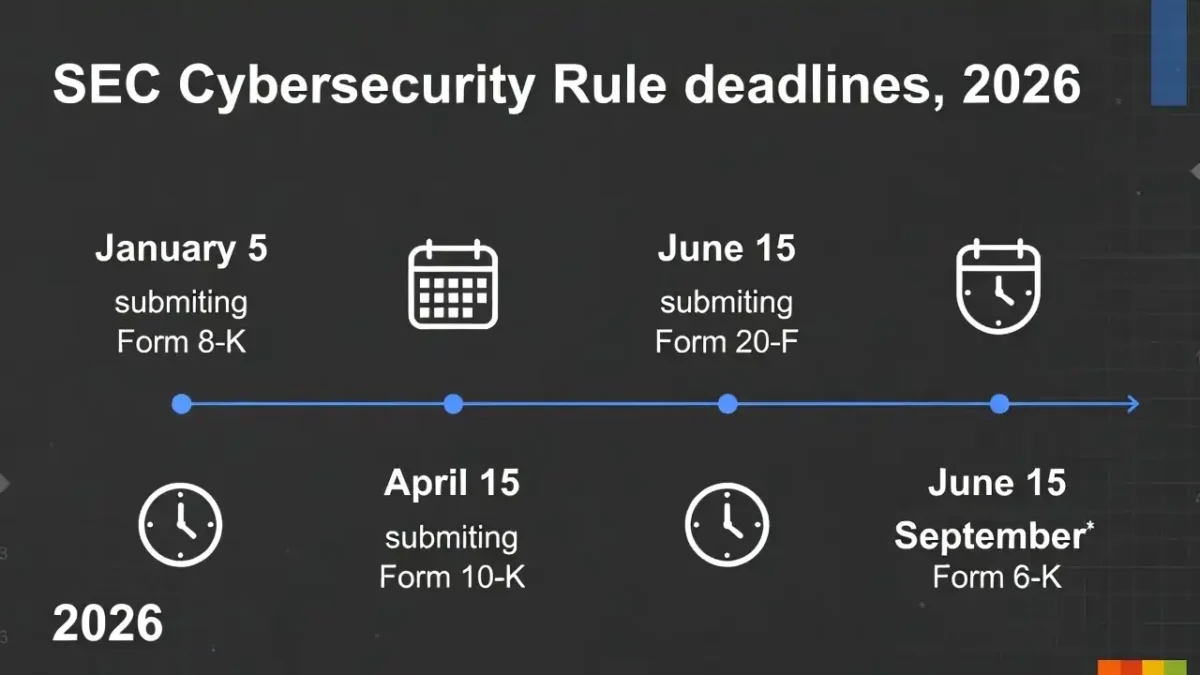
CIRCIA vs SEC and UK Reporting Rules
It is important to distinguish CIRCIA from other reporting frameworks:
- CIRCIA applies to critical infrastructure entities.
- SEC rules apply to publicly traded companies.
- UK ICO rules apply to personal data breaches.
Some organizations may be subject to multiple frameworks simultaneously.
Multinational or publicly traded infrastructure companies must coordinate across:
- CISA (CIRCIA)
- SEC (4-day disclosure rule)
- UK ICO (72-hour GDPR rule)
This increases the importance of integrated incident response governance.
Practical Compliance Checklist
To prepare for the CIRCIA 72-Hour Reporting Rule, organizations should:
- Confirm whether they qualify as a covered entity
- Establish internal incident classification criteria
- Create federal reporting templates in advance
- Conduct tabletop exercises simulating 72-hour reporting
- Track detection metrics at executive level
Prepared organizations reduce regulatory stress during real incidents.
Final Thoughts
The CIRCIA 72-Hour Reporting Rule represents a major shift in U.S. cybersecurity governance.
Covered entities must report substantial cyber incidents within 72 hours and ransomware payments within 24 hours.
Detection speed directly affects compliance readiness.
In 2026, cybersecurity timing is federal policy.
Organizations that reduce dwell time and improve MTTD are better positioned to meet reporting obligations without operational disruption.