Cybersecurity Time: Detection and Response Guide
Cybersecurity Time describes how quickly an organization can detect, respond to, and contain cyber threats.
In modern cybersecurity, speed matters more than ever. Attacks are more frequent, more complex, and faster to spread. Organizations must reduce detection and response time to minimize damage and financial loss.
This pillar guide explains what Cybersecurity Time means, why it matters, the key metrics used to measure it, and how organizations can reduce security response delays.
Table of Contents
What Is Cybersecurity Time?
Cybersecurity Time refers to time-based measurements used to evaluate how fast a security team can handle cyber incidents.
It focuses on:
- Time to detect an attack
- Time to respond after detection
- Time to contain the threat
- Time to recover systems
In simple terms, Cybersecurity Time answers this question:
How long does a cyber attacker have before being stopped?
Shorter Cybersecurity Time means less damage, lower costs, and better protection.
Why Cybersecurity Time Matters
Cyber attacks do not cause damage instantly. They follow a timeline.
- Initial access
- Persistence
- Lateral movement
- Data access
- Detection
- Response
- Containment
If detection happens late, attackers can stay inside systems for days, weeks, or even months.
Reducing Cybersecurity Time helps organizations:
- Limit data breaches
- Reduce downtime
- Avoid regulatory penalties
- Protect brand reputation
Speed is now one of the most important cybersecurity defenses.
Incident Response Time Metrics
Mean Time to Detect (MTTD)
Mean Time to Detect measures how long it takes to discover a security incident after it begins.
Lower MTTD means faster awareness and less attacker dwell time.
Mean Time to Respond (MTTR)
Mean Time to Respond measures how quickly a security team reacts once a threat is detected.
Fast response prevents escalation and limits damage.
Mean Time to Contain (MTTC)
Mean Time to Contain measures how long it takes to isolate affected systems and stop the attack from spreading.
Containment is critical during ransomware and network-wide attacks.
Dwell Time
Dwell Time is the total time an attacker remains undetected inside an environment.
High dwell time increases the risk of data theft and system compromise.
Recovery Time
Recovery Time measures how quickly systems return to normal after containment and remediation.
Typical Incident Response Timeline
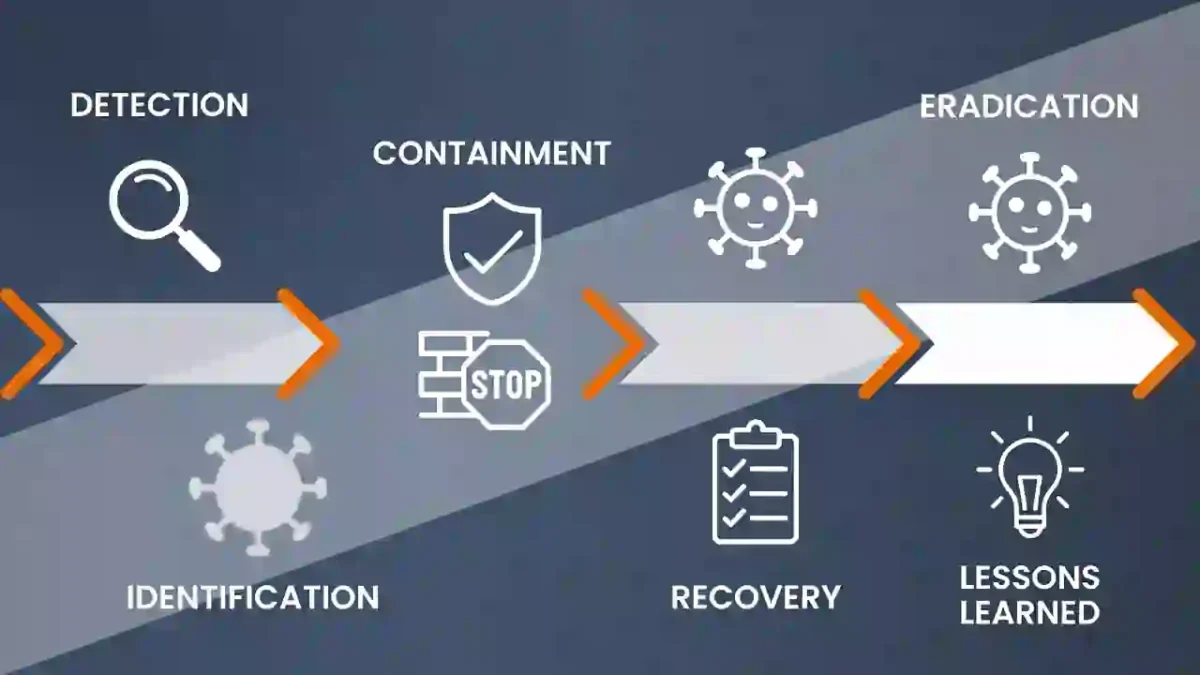
A typical cybersecurity incident follows these stages:
Compromise – Phishing, malware, or stolen credentials
Persistence – Attacker maintains access
Movement – Lateral exploration
Targeting – Sensitive data identified
Detection – Alerts triggered
Response – Investigation begins
Containment – Threat isolated
Reducing Cybersecurity Time shortens every stage after compromise.
Industry Benchmarks
Security research consistently shows that:
- Many breaches go undetected for long periods
- Organizations with automation detect threats faster
- 24/7 monitoring reduces response delays
For trusted industry research, refer to:
🌐 External Links :
How to Improve Incident Response Speed
Improving Cybersecurity Time requires people, process, and technology.
Continuous Monitoring
Use SIEM, EDR, and network monitoring tools to detect threats earlier.
Automated Response
Automation helps block threats immediately without waiting for manual action.
Clear Incident Response Plan
Defined roles and procedures reduce confusion during incidents.
Cybersecurity Incident Response Timeline
Regular Security Testing
Tabletop exercises and simulations help identify response delays.
Frequently Asked Questions
What does response time mean in cybersecurity?
Cybersecurity Time measures how quickly threats are detected, responded to, and contained.
What does response time mean in cybersecurity?
Faster response reduces damage, cost, and downtime.
What is a good detection time?
Leading organizations aim to detect threats within hours instead of days or weeks.
Final Thoughts
Cybersecurity Time is now a core security performance metric.
Organizations that continuously improve detection, response, and containment speed reduce cyber risk and strengthen resilience.
In cybersecurity, speed is protection.

