How to Reduce Cyber Breach Detection Time: 9 Critical Strategies
How to Reduce Cyber Breach Detection Time has become a central priority for modern security teams.
In today’s threat landscape, attackers move quickly. The longer an intrusion goes undetected, the greater the financial loss, operational disruption, and reputational damage. Extended dwell time allows adversaries to escalate privileges, move laterally, and exfiltrate sensitive data before containment begins.
This advanced playbook outlines practical, measurable strategies to reduce cyber breach detection time and strengthen overall detection maturity.
Table of Contents
Why Detection Speed Matters for Cyber Breach Detection Time
Understanding how to reduce cyber breach detection time begins with understanding attack progression.
Most breaches unfold in stages:
- Initial access
- Privilege escalation
- Lateral movement
- Data exfiltration
- Impact
For lifecycle context:
🔗 Link: Cyber Attack Lifecycle Timeline
The longer detection is delayed, the higher the business impact.
1️⃣ Strengthen Continuous Monitoring to Reduce Cyber Breach Detection Time
Continuous monitoring is foundational.
Organizations should:
- Implement 24/7 SOC coverage
- Use managed detection services
- Monitor endpoints and cloud workloads
Without real-time oversight, detection gaps increase.
2️⃣ Improve Log Visibility Across All Systems
Log gaps are a primary cause of delayed detection.
To reduce cyber breach detection time:
- Centralize logs into a SIEM
- Monitor cloud, network, and endpoint telemetry
- Enable detailed audit logging
Detection cannot occur without visibility.
3️⃣ Use Behavioral Analytics
Signature-based detection alone is insufficient.
Behavioral analytics identifies anomalies such as:
- Abnormal login patterns
- Suspicious privilege changes
- Lateral movement behaviors
This significantly improves early breach detection.
4️⃣ Automate Alert Prioritization
Security teams face alert overload.
Automation helps:
- Correlate events
- Escalate high-risk alerts
- Reduce investigation delays
Improving:
🔗 Link: Mean Time to Detect (MTTD)
Directly supports efforts to reduce cyber breach detection time.
5️⃣ Reduce Alert Fatigue
Alert fatigue slows investigations.
Improve detection performance by:
- Tuning detection rules
- Eliminating noisy alerts
- Focusing on high-confidence signals
Cleaner alert pipelines accelerate response.
6️⃣ Conduct Proactive Threat Hunting
Threat hunting identifies attackers before automated tools generate alerts.
Hunting focuses on:
- Indicators of compromise
- Suspicious outbound traffic
- Credential misuse
🔗 Link: How Long Do Hackers Stay Undetected
Proactive investigation shortens dwell time.
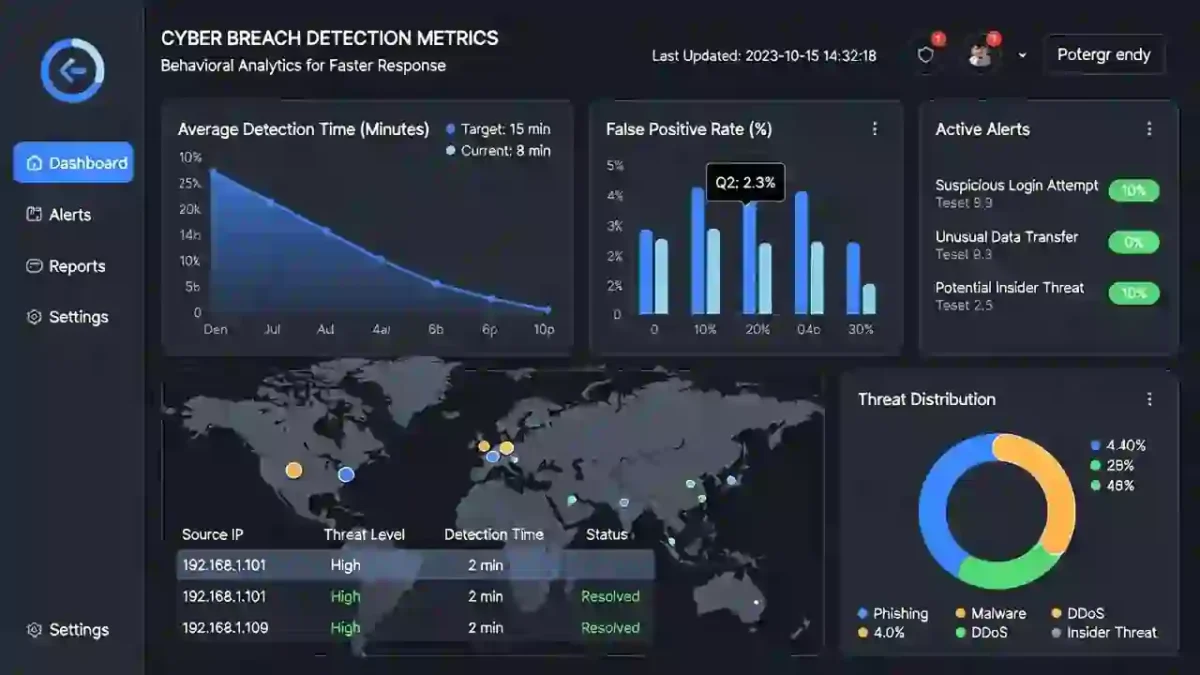
7️⃣ Benchmark Detection Metrics
If you want to reduce cyber breach detection time, you must measure it.
Track:
- Mean Time to Detect
- Mean Time to Contain
- Dwell Time
🔗 Link: Industry Benchmarks 2026
Benchmarking reveals performance gaps.
8️⃣ Simulate Real-World Attack Scenarios
Red team exercises expose blind spots.
Simulations evaluate:
- Detection accuracy
- Escalation speed
- Cross-team coordination
Testing improves operational maturity.
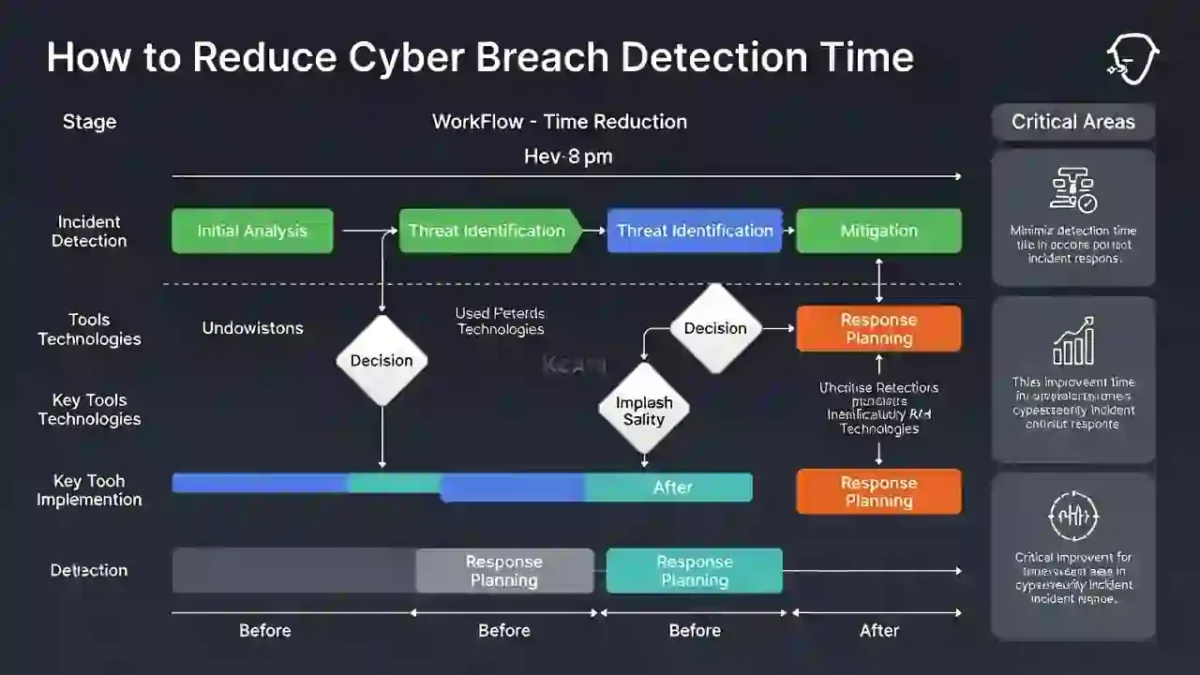
9️⃣ Integrate Detection with Response Workflows
Detection without immediate response limits value.
Ensure:
- Automated containment triggers
- Clear escalation playbooks
- Cross-team communication
Reducing friction between detection and response dramatically improves containment speed.
Industry Research Supporting Faster Detection
Research consistently shows that faster detection reduces breach cost.
🌍 Link: IBM Cost of a Data Breach Report
Organizations that detect and contain incidents quickly experience lower financial impact.
Reducing detection time protects both technical systems and business outcomes.
Final Thoughts
How to Reduce Cyber Breach Detection Time requires operational discipline, automation, visibility, and benchmarking.
Organizations that prioritize continuous monitoring and measurable detection metrics significantly reduce dwell time and limit breach impact.
In cybersecurity, speed is protection.


