Mean Time to Detect: 5 Proven Ways to Reduce Cyber Risk
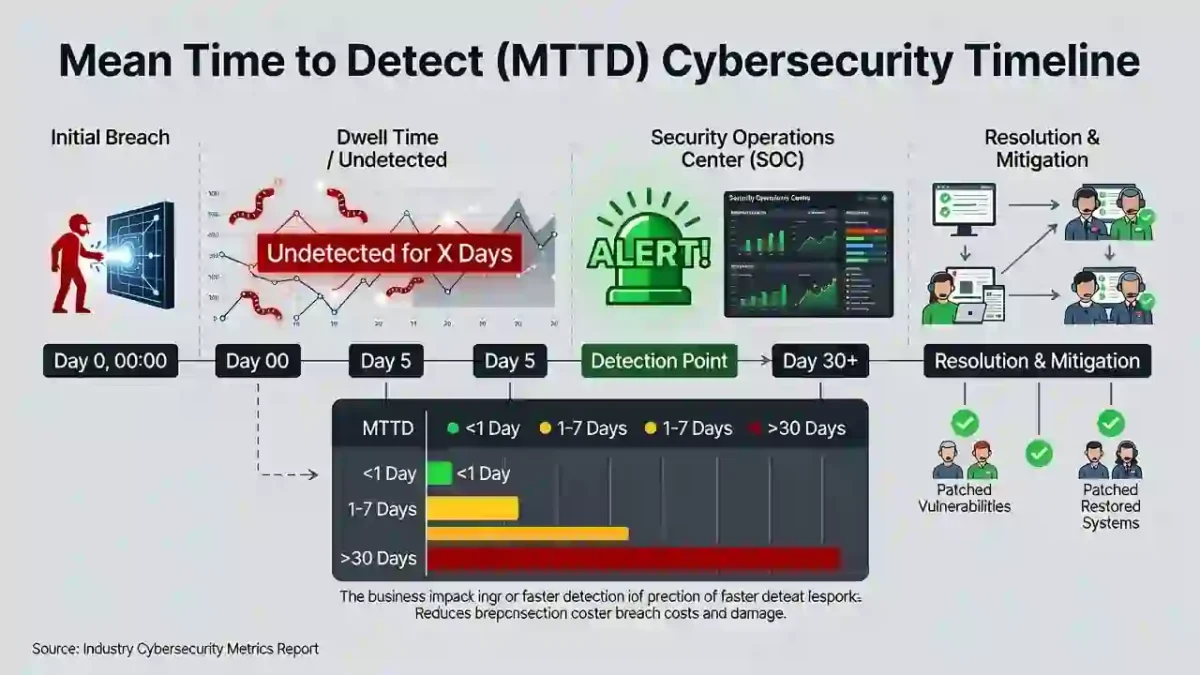
Mean Time to Detect (MTTD) is a critical cybersecurity metric that measures how long it takes to identify a cyber attack after it begins.
A high Mean Time to Detect allows attackers to remain hidden, increasing the risk of data loss, system damage, and financial impact. Organizations that reduce Mean Time to Detect are able to limit attacks earlier and respond more effectively.
This guide explains Mean Time to Detect in clear terms, why it matters, how it is measured, and how to reduce detection delays.
Table of Contents
What Is Mean Time to Detect?
Mean Time to Detect is the average amount of time required to discover a security incident after it occurs.
In simple terms:
Mean Time to Detect shows how long an attacker stays inside a system before being noticed.
Lower Mean Time to Detect improves visibility, reduces attacker dwell time, and limits damage.
Why Mean Time to Detect Matters
Cyber attacks rarely cause immediate disruption. Attackers often spend time exploring systems, escalating privileges, and locating sensitive data.
When Mean Time to Detect is high:
- Breaches become larger
- Recovery takes longer
- Costs increase
- Compliance risks grow
Reducing Mean Time to Detect improves overall Cybersecurity Time and strengthens security posture.
How Mean Time to Detect Is Calculated
Mean Time to Detect is calculated using a simple formula:
MTTD = Total Detection Time ÷ Number of Incidents
Example
If 4 incidents took a total of 80 hours to detect:
Mean Time to Detect = 20 hours
Tracking this metric regularly helps organizations measure improvement.
Average Time to Detect a Cyber Attack
The average time to detect a cyber attack varies depending on security maturity.
General observations:
- Many organizations take weeks to detect breaches
- Advanced security teams detect threats within hours
- Automated monitoring significantly reduces Mean Time to Detect
For trusted research, refer to:
5 Proven Ways to Reduce Mean Time to Detect
1. Continuous Security Monitoring
Use SIEM and EDR tools to monitor systems in real time.
Continuous monitoring lowers Mean Time to Detect by identifying threats earlier.
2. Behavioral Threat Detection
Behavior-based analytics identify abnormal activity faster than traditional tools.
3. Automated Alert Correlation
Automation helps connect related alerts into actionable incidents, reducing investigation delays.
4. Centralized Log Management
Centralized logs improve visibility and speed up threat analysis.
5. Clear Escalation Procedures
Defined escalation paths reduce confusion and shorten detection delays.
Mean Time to Detect vs Other Security Metrics
Mean Time to Detect works alongside other cybersecurity metrics:
Frequently Asked Questions
What is a good Mean Time to Detect?
High-performing organizations aim to detect threats within hours rather than days.
Why is Mean Time to Detect important?
Lower Mean Time to Detect limits attacker dwell time and reduces breach impact.
Is Mean Time to Detect the same as response time?
No. Detection measures discovery speed, while response measures action speed.
Final Thoughts
Mean Time to Detect is a foundational cybersecurity metric.
Organizations that improve monitoring, automation, and visibility significantly reduce cyber risk and limit attack impact.
Improving Mean Time to Detect strengthens overall cybersecurity resilience.


