PayPal Data Breach 2026: 7 Critical Timeline Facts
The PayPal Data Breach 2026 has raised serious concerns across the United States. As one of the largest digital payment platforms in the world, PayPal handles millions of daily transactions.
When a financial platform experiences a cybersecurity incident, the most important question is not just what was accessed — but how quickly the threat was detected and contained.
In cybersecurity, time determines impact.
This article breaks down the PayPal Data Breach 2026 timeline, analyzes detection and response performance, and explains what individuals and organizations can learn.
Table of Contents
Overview of the PayPal Data Breach 2026
Reports indicate unauthorized access to parts of PayPal’s infrastructure. Early investigations suggest potential exposure of:
- Account email addresses
- Limited transaction metadata
- Authentication-related information
There is no confirmed large-scale exposure of full financial credentials at this stage. Investigations are ongoing.
For official cybersecurity response standards, organizations often follow the
National Institute of Standards and Technology (NIST) Cybersecurity Framework:
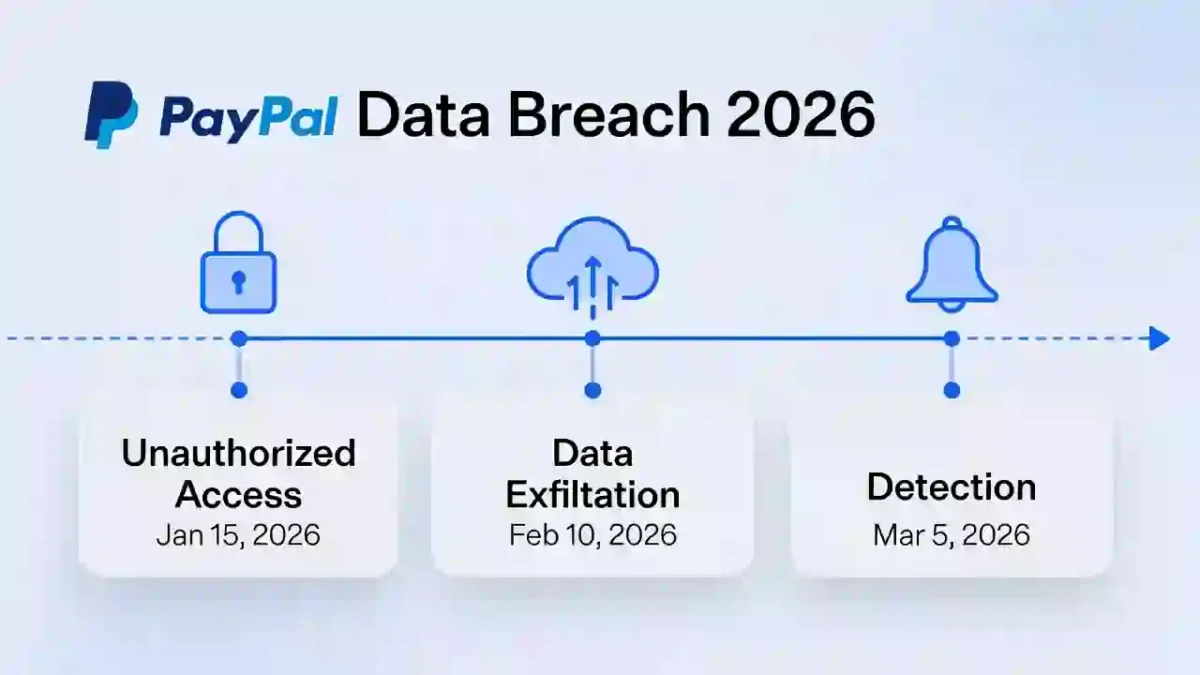
Timeline of the PayPal Data Breach 2026
Understanding the timeline helps evaluate security maturity.
Phase 1: Initial Access
Attackers may have exploited:
- Compromised login credentials
- Third-party integration vulnerabilities
- Application-layer weaknesses
This phase often happens silently.
Phase 2: Internal Exploration
After entry, attackers typically:
- Attempt privilege escalation
- Map internal systems
- Search for valuable data
This stage increases exposure risk.
Phase 3: Detection
The PayPal Data Breach 2026 was reportedly identified through internal monitoring systems and suspicious activity alerts.
Detection speed directly influences overall damage.
Phase 4: Response and Containment
Once identified, actions included:
- Resetting credentials
- Securing affected systems
- Launching forensic investigations
- Initiating regulatory notifications
Containment stops attacker movement.
Dwell Time and Detection Speed
Dwell time refers to how long attackers remain inside systems before detection.
Short dwell time limits exposure.
Long dwell time increases data risk.
You can learn more here: Dwell Time Cybersecurity
Financial institutions usually aim to maintain low Mean Time to Detect (MTTD) to minimize dwell time.
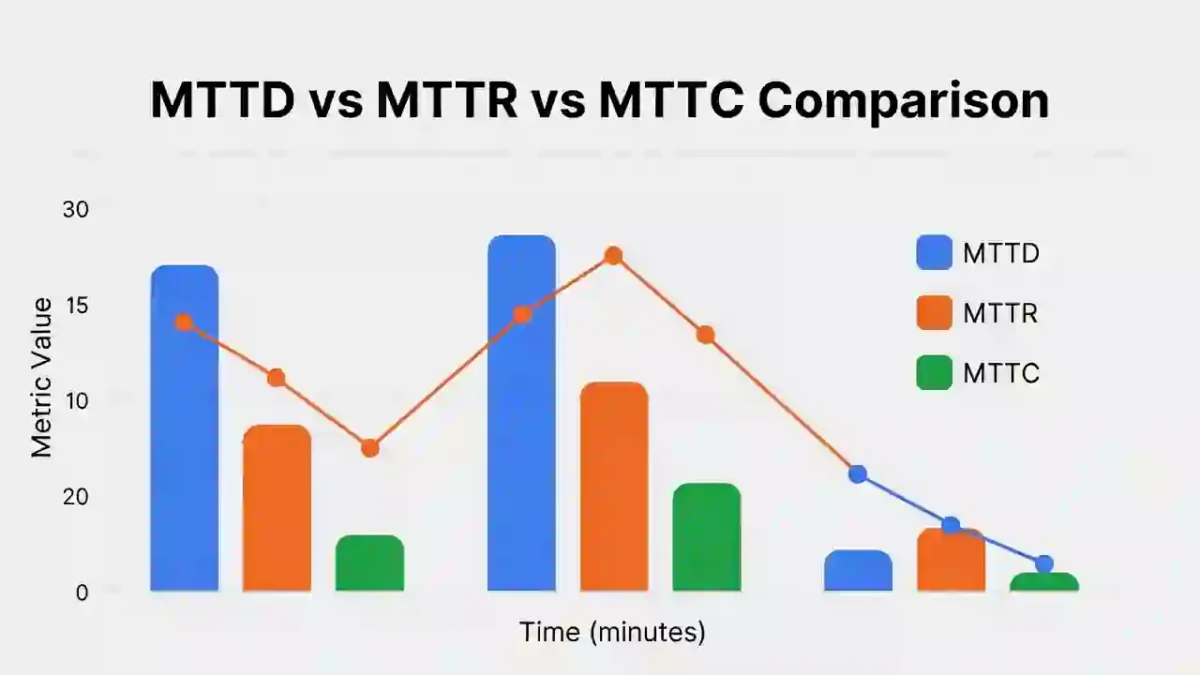
MTTD, MTTR, and Containment Analysis
The PayPal Data Breach 2026 can be evaluated through three key metrics:
Mean Time to Detect (MTTD)
Measures how quickly the breach was discovered.
Lower MTTD reduces overall exposure.
Learn more: Mean Time to Detect Cybersecurity
Mean Time to Respond (MTTR)
Measures how quickly response begins after detection.
Faster response reduces spread and impact.
Comparison guide: MTTD vs MTTR vs MTTC vs Dwell Time
Mean Time to Contain (MTTC)
Measures how long it takes to fully isolate the threat.
Rapid containment significantly lowers financial and regulatory risk.
Impact on U.S. Users
PayPal is widely used across:
- E-commerce platforms
- Subscription services
- Small businesses
- Peer-to-peer payments
Users should:
- Enable two-factor authentication
- Monitor transaction activity
- Be cautious of phishing emails
- Update passwords
For identity theft guidance: Tdentity Theft
7 Key Lessons from the PayPal Data Breach 2026
- Detection speed limits damage.
- Continuous monitoring reduces dwell time.
- Third-party risk must be controlled.
- Automation accelerates containment.
- Incident response planning is essential.
- Transparency maintains user trust.
- Time-based metrics reveal true security strength.
FAQs
Was financial data exposed?
Investigations suggest limited exposure, but full forensic results will determine final impact.
How long were attackers undetected?
Exact dwell time has not been publicly disclosed.
How can businesses prevent similar incidents?
By improving detection speed, response procedures, and containment strategies.


