Ransomware Attack Timeline: 7 Critical Stages
A ransomware incident does not begin with encryption.
In real-world cases, the Ransomware Attack Timeline unfolds gradually. Attackers infiltrate, escalate privileges, move laterally, and often steal data before launching encryption.
By the time systems are locked, the attackers have already prepared for maximum disruption.
Understanding the Ransomware Attack Timeline gives security teams multiple opportunities to detect and disrupt the attack early.
Table of Contents

Stage 1: Initial Access
The Ransomware Attack Timeline begins with entry into the network.
Common access vectors include:
- Phishing emails
- Exploited vulnerabilities
- Stolen credentials
- Exposed remote services
Initial compromise often appears minor and may not trigger high-priority alerts.
For insight into detection delays:
🔗 Link: How Long Do Hackers Stay Undetected
Stage 2: Persistence and Foothold
After gaining entry, attackers establish persistence to maintain access.
Techniques include:
- Creating hidden admin accounts
- Installing remote access tools
- Modifying startup services
- Scheduled task manipulation
If detected at this stage, the incident can often be contained before major damage occurs.
Stage 3: Privilege Escalation
Attackers attempt to gain elevated permissions to expand control.
Privilege escalation allows them to:
- Disable security software
- Access domain controllers
- Manipulate backup systems
This stage is a major turning point in the Ransomware Attack Timeline.
For lifecycle context:
🔗 Link: Cyber Attack Lifecycle Timeline
Stage 4: Lateral Movement
With elevated privileges, attackers move across systems.
They identify:
- File servers
- Backup repositories
- Sensitive databases
Lateral movement significantly increases potential impact.
Modern attackers often use legitimate tools (living-off-the-land techniques) to avoid detection.
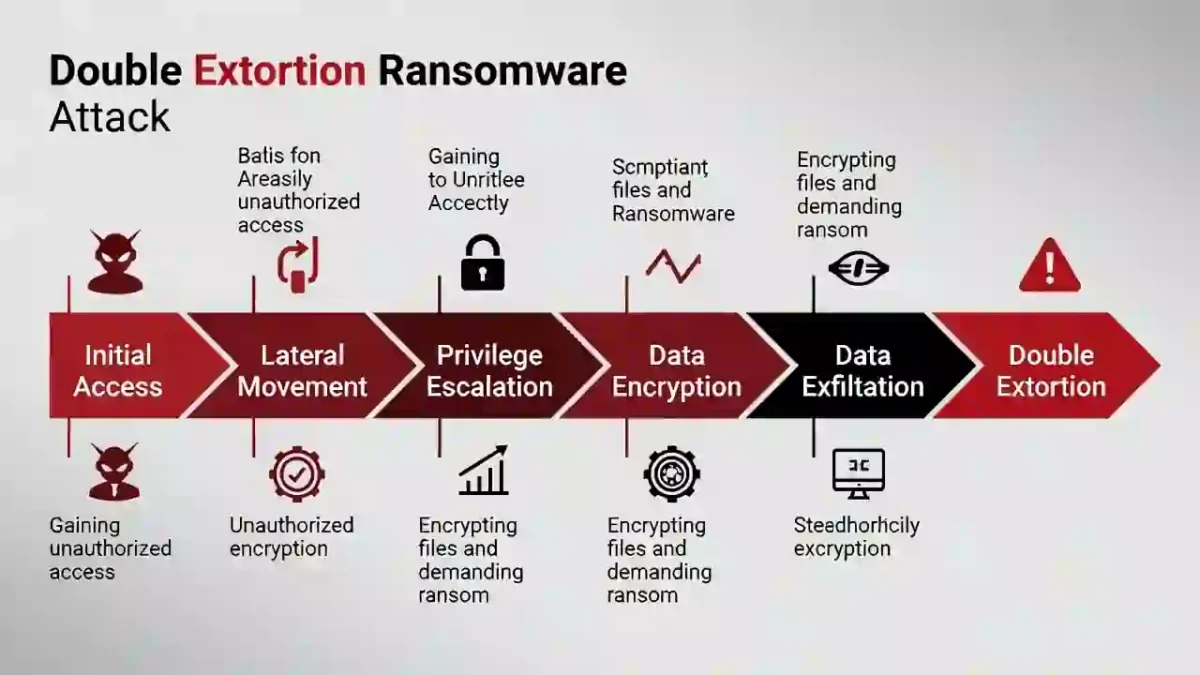
Stage 5: Data Exfiltration
Today’s ransomware groups frequently steal data before encryption.
This “double extortion” model increases pressure on victims.
According to:
🌍 External Link: CISA Stop Ransomware Guidance
Data theft now plays a central role in many ransomware campaigns.
Stage 6: Encryption Deployment
Encryption is the final operational step — not the first.
Before deploying ransomware, attackers often:
- Disable backups
- Terminate security processes
- Deploy encryption simultaneously across endpoints
Research from:
🌍 External Link: IBM Cost of a Data Breach Report
Shows that downtime costs escalate dramatically once encryption begins.
Stage 7: Extortion Phase
After encryption, attackers demand payment.
They may:
- Request cryptocurrency
- Provide proof-of-decryption samples
- Threaten data leaks
- Set strict deadlines
At this point, business impact becomes severe and recovery options narrow.
Industry analysis from:
🌍 External Link: Mandiant M-Trends Report
Shows that early-stage detection dramatically reduces overall damage.
How to Interrupt the Ransomware Attack Timeline
Organizations can disrupt the Ransomware Attack Timeline by improving early detection and response.
Key controls include:
- 24/7 monitoring
- Endpoint detection and response (EDR)
- Network segmentation
- Multi-factor authentication
- Offline and immutable backups
For performance comparison:
🔗 Internal Link: Industry Benchmarks 2026
Reducing detection time shortens the attack timeline and limits operational damage.
Final Analysis
The Ransomware Attack Timeline demonstrates that encryption is not the beginning of an attack — it is the final stage.
Most ransomware incidents follow predictable patterns: infiltration, persistence, escalation, movement, exfiltration, and encryption.
Organizations that understand each stage gain multiple opportunities to intervene before catastrophic impact occurs.
Early visibility is the strongest defense.


