Reduce Detection Time Regulatory Deadlines Risk
Cybersecurity incidents now trigger immediate regulatory consequences.
Organizations must reduce detection time regulatory deadlines exposure before reporting clocks begin shrinking. In 2026, detection speed determines whether security teams have sufficient time to investigate incidents, assess materiality, consult legal teams, and prepare compliant disclosures.
Failing to reduce detection time regulatory deadlines risk can create unnecessary compliance pressure and executive exposure.
Detection is no longer just a SOC metric — it is a governance safeguard.
Table of Contents
Why Reduce Detection Time Regulatory Deadlines Pressure Matters
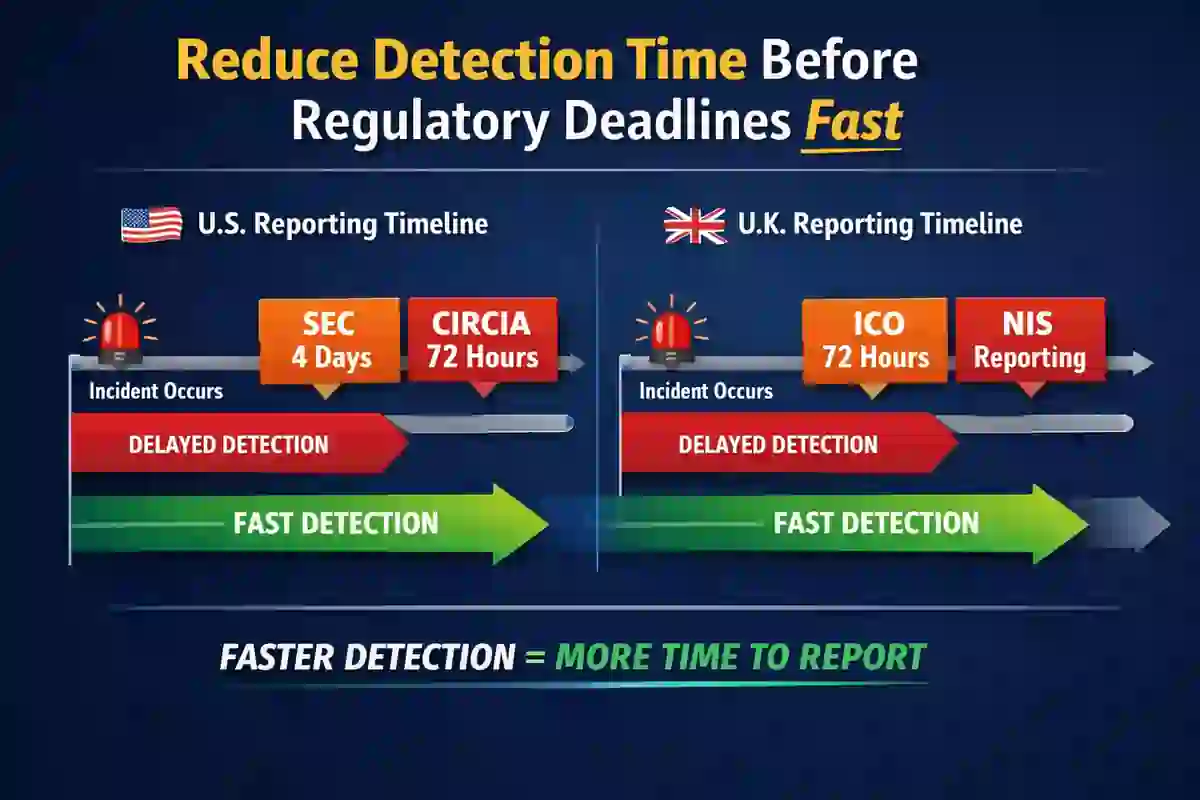
Regulatory timelines in the US and UK are strict.
Detection speed directly impacts:
- SEC 4-business-day disclosure windows
- CIRCIA 72-hour reporting rules
- UK ICO 72-hour breach notification requirements
- Ransomware payment reporting deadlines
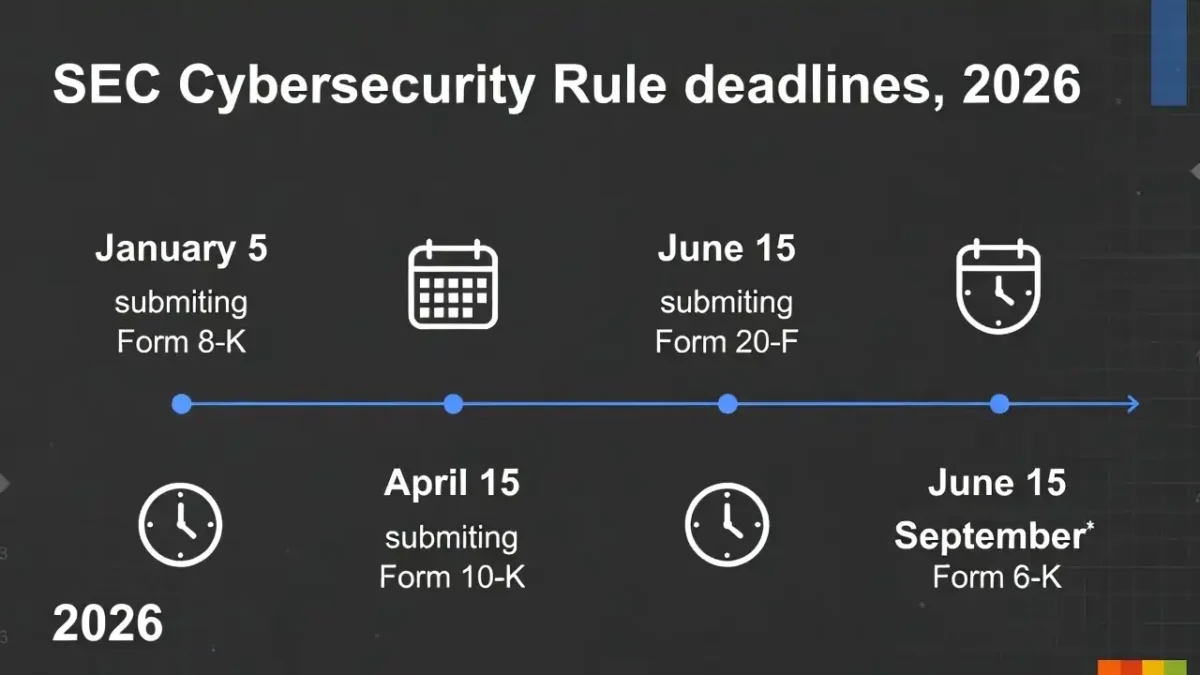
Under SEC cybersecurity disclosure rules:
Public companies must disclose material cyber incidents within four business days after determining materiality.
CIRCIA reporting requirements mandate 72-hour incident notification:
The UK ICO requires breach reporting within 72 hours under GDPR
If attackers remain undetected for extended periods, the available reporting window compresses rapidly.
Organizations that reduce detection time regulatory deadlines pressure gain critical decision-making flexibility.
How Detection Delays Increase Compliance Risk
Delayed detection creates several risks:
- Less time for forensic analysis
- Increased chance of incomplete reporting
- Higher regulatory scrutiny
- Increased reputational damage
- Greater legal exposure
The longer dwell time persists, the harder it becomes to provide accurate and defensible disclosures.
👉 Related topic: Dwell Time vs MTTD
Reducing dwell time and improving detection speed are essential compliance controls.
7 Proven Ways to Reduce Detection Time Regulatory Deadlines Risk
1️⃣ Improve Mean Time to Detect (MTTD)
Tracking and trending MTTD reveals detection inefficiencies.
👉 Internal guide: Mean Time to Detect (MTTD)
Lower MTTD directly supports efforts to reduce detection time regulatory deadlines exposure.
2️⃣ Deploy AI-Enhanced Threat Detection
AI-driven monitoring identifies behavioral anomalies faster than traditional rule-based detection.
👉 Related article: AI and Incident Response Automation
Automation reduces alert fatigue and improves early threat discovery.
3️⃣ Eliminate Alert Triage Bottlenecks
Slow alert classification creates detection delays.
Measure:
- Average triage time
- Analyst workload distribution
- Escalation speed
👉 SOC efficiency reference: SOC Efficiency Metrics 2026
Efficient triage plays a direct role in reducing detection time regulatory deadlines pressure.
4️⃣ Implement Continuous 24/7 Monitoring
Many incidents are discovered outside standard business hours.
Continuous monitoring or MDR services help close detection gaps.
Early discovery strengthens regulatory response posture.
5️⃣ Integrate External Threat Intelligence
Threat intelligence feeds improve identification of known indicators of compromise.
According to the Verizon Data Breach Investigations Report:
Delayed detection remains a leading breach factor across industries.
Improved intelligence integration helps reduce detection time regulatory deadlines risk.
6️⃣ Conduct Regulatory Simulation Exercises
Tabletop exercises should evaluate:
- Detection lag
- Escalation workflows
- Legal review timelines
- Disclosure preparation speed
Simulation reduces confusion during real incidents and improves compliance readiness.
7️⃣ Align Security, Legal & Compliance Teams
Detection alone is not enough.
Security teams must coordinate early with legal and compliance departments.
Clear escalation paths and predefined reporting workflows help organizations reduce detection time regulatory deadlines exposure effectively.
Executive & Board-Level Implications
Boards increasingly monitor:
- Detection speed
- Dwell time
- Containment performance
- Reporting readiness
👉 Governance reference: Board-Level Cybersecurity Metrics Guide
Reducing detection time regulatory deadlines exposure demonstrates proactive governance and regulatory preparedness.
In 2026, detection speed is a board-level performance indicator.
Final Takeaways
To reduce detection time regulatory deadlines pressure, organizations must:
- Measure and improve MTTD
- Automate detection workflows
- Reduce triage bottlenecks
- Integrate threat intelligence
- Conduct compliance simulations
- Align security with legal oversight
Regulatory clocks do not pause.
Faster detection provides strategic decision-making space, reduces legal exposure, and strengthens compliance resilience.
Operational efficiency now defines regulatory strength.