Top Cybersecurity Threats to Watch in 2026: 10 Critical Risks
The cybersecurity landscape in 2026 is defined by acceleration. Attackers are moving faster, automation is more accessible, and digital infrastructure is more complex than ever.
Understanding the Top Cybersecurity Threats to Watch in 2026 is no longer optional for security leaders. The risks outlined below reflect current attack patterns observed across industry investigations, global research reports, and incident response engagements.
Organizations that recognize these trends early will be better positioned to reduce exposure and respond effectively.
Table of Contents
Why the Top Cybersecurity Threats to Watch in 2026 Matter
Threat actors increasingly operate in structured stages — reconnaissance, access, privilege escalation, lateral movement, and impact.
For a deeper breakdown of how attacks progress:
🔗 Internal Link: Cyber Attack Lifecycle Timeline
The Top Cybersecurity Threats to Watch in 2026 highlight not just individual risks, but systemic weaknesses that attackers continue to exploit.

1. AI-Enhanced Phishing Campaigns
Artificial intelligence has significantly improved phishing realism.
Modern phishing emails are personalized, context-aware, and grammatically refined. This reduces traditional detection signals and increases engagement rates.
According to the Verizon Data Breach Investigations Report, phishing remains a leading initial access vector.
In 2026, AI tools are amplifying its effectiveness.
2. Ransomware-as-a-Service (RaaS)
Ransomware groups now operate as scalable service providers.
Affiliates deploy ransomware using shared infrastructure and revenue-sharing models. This industrialization lowers entry barriers and increases global attack volume.
For real-world progression:
🔗 Internal Link: Ransomware Attack Timeline
Ransomware remains one of the Top Cybersecurity Threats to Watch in 2026 due to operational disruption and regulatory consequences.
3. Identity-Based Attacks
Identity systems have become primary targets.
Attackers increasingly exploit:
- MFA fatigue techniques
- Stolen credentials
- Session hijacking
- Token replay attacks
Identity compromise often bypasses perimeter defenses.
Improving detection speed is essential.
🔗 Internal Link: Mean Time to Detect (MTTD)
4. Cloud Misconfiguration Exploits
Cloud adoption continues to outpace governance.
Common exposure points include:
- Public storage buckets
- Over-permissioned IAM roles
- Unsecured APIs
Cloud security posture management will remain critical in 2026.
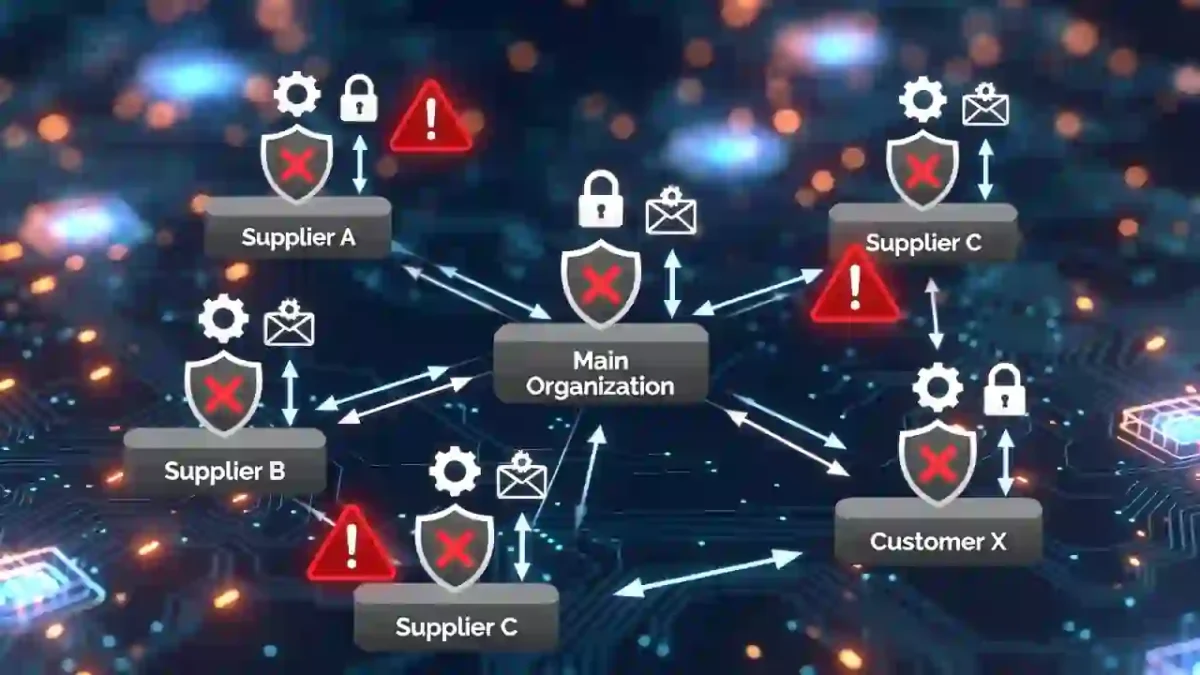
5. Supply Chain Compromise
Supply chain attacks allow adversaries to target multiple victims indirectly.
Compromised vendors, software updates, and service providers provide high-value entry paths.
These attacks scale rapidly and undermine trust-based access assumptions.
6. Zero-Day Exploitation
Time-to-exploit continues to shrink.
Threat actors weaponize newly disclosed vulnerabilities quickly, often before patch adoption becomes widespread.
🌍 External Link: CISA Known Exploited Vulnerabilities Catalog
Rapid patching cycles are essential defensive measures.
7. Deepfake and AI Impersonation
AI-generated voice and video impersonation attacks are increasing in sophistication.
Financial fraud incidents involving executive voice cloning have already been documented.
These attacks exploit human trust rather than software flaws.
8. Critical Infrastructure Targeting
Energy, healthcare, transportation, and public utilities remain strategic targets.
Geopolitical tensions continue to influence cyber activity directed at infrastructure systems.
Disruption risks extend beyond financial damage into national security.
9. Insider Risk in Hybrid Work Models
Remote and hybrid work environments have reshaped access patterns.
Insider risk now includes:
- Excessive permissions
- Data mishandling
- Unmanaged personal devices
Access governance and monitoring remain key control priorities.
10. IoT and Edge Device Exposure
IoT and edge devices introduce new attack surfaces.
Many lack:
- Strong authentication
- Centralized monitoring
- Automated patching
As adoption grows, unmanaged endpoints become attractive targets.
Industry Research Supporting the 2026 Outlook
The Top Cybersecurity Threats to Watch in 2026 align with findings from leading global research:
🌍 IBM Cost of a Data Breach Report
These reports emphasize the importance of visibility, response speed, and operational maturity.
For detection benchmarks:
🔗 Internal Link: Industry Benchmarks 2026
Strategic Priorities for 2026
To address the Top Cybersecurity Threats to Watch in 2026, organizations should focus on:
- Identity-first security models
- Continuous monitoring and automation
- Cloud configuration governance
- Regular incident response simulations
- Detection and response benchmarking
Preparation reduces impact. Speed reduces damage.
Frequently Asked Questions About Cybersecurity Threats in 2026
What is the biggest cybersecurity threat in 2026?
Identity-based compromise and ransomware remain among the most impactful threats due to their scalability and operational disruption potential.
Are AI-driven attacks increasing in 2026?
Yes. AI is improving phishing realism, automating reconnaissance, and enhancing social engineering campaigns.
Why are cloud threats growing?
Cloud adoption continues to expand faster than governance maturity, leading to configuration-related vulnerabilities.
Final Assessment
The Top Cybersecurity Threats to Watch in 2026 reflect a threat landscape shaped by automation, identity exploitation, and coordinated criminal infrastructure.
Organizations that prioritize visibility, continuous monitoring, and operational discipline will be better positioned to mitigate these risks.
Threat actors evolve quickly. Defensive maturity must evolve faster.


