Essential Cybersecurity Tools: 7 Powerful Solutions Explained
Modern organizations rely on technology to operate, communicate, and store critical data. As cyber threats grow more sophisticated, deploying the right defensive technologies becomes essential.
Understanding essential cybersecurity tools helps organizations improve visibility, reduce detection time, and strengthen incident response capabilities.
From SIEM platforms to endpoint monitoring solutions, these tools form the operational backbone of modern security programs.
Table of Contents
Why Essential Cybersecurity Tools Matter
Cyber attackers increasingly automate their campaigns, exploit misconfigurations, and move laterally once inside a network.
Without the right tools, organizations struggle to:
- Detect malicious activity early
- Correlate suspicious events
- Investigate security alerts efficiently
- Respond before damage spreads
Essential cybersecurity tools provide the monitoring, automation, and intelligence required to limit breach impact.
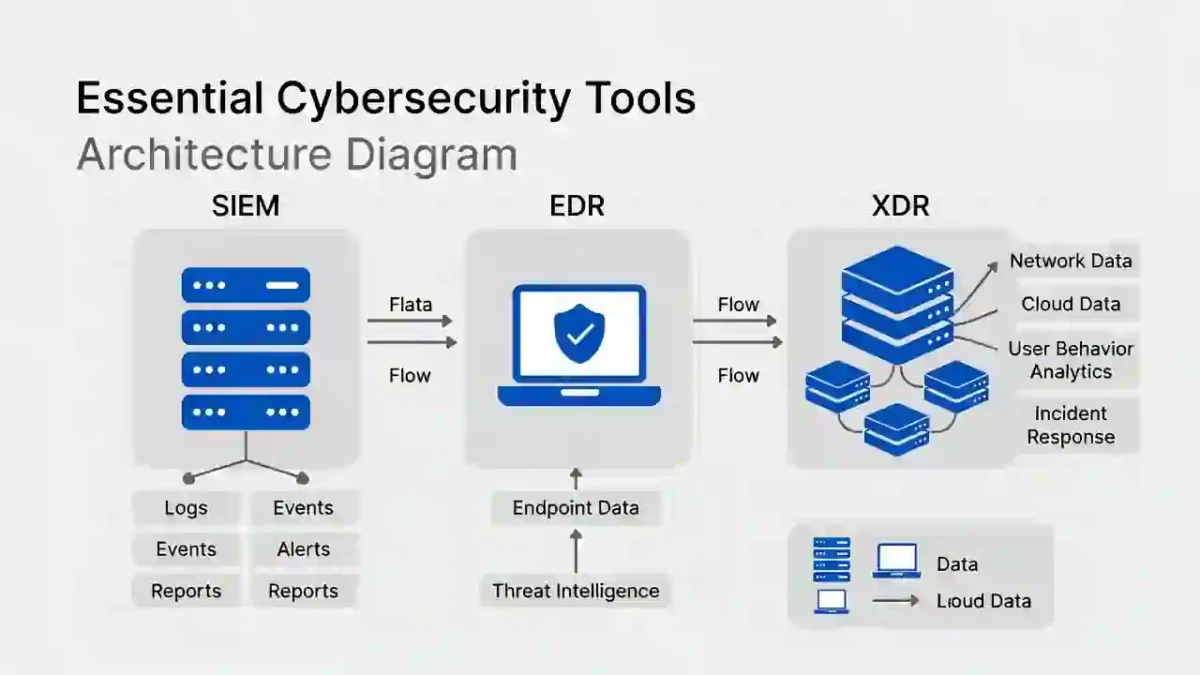
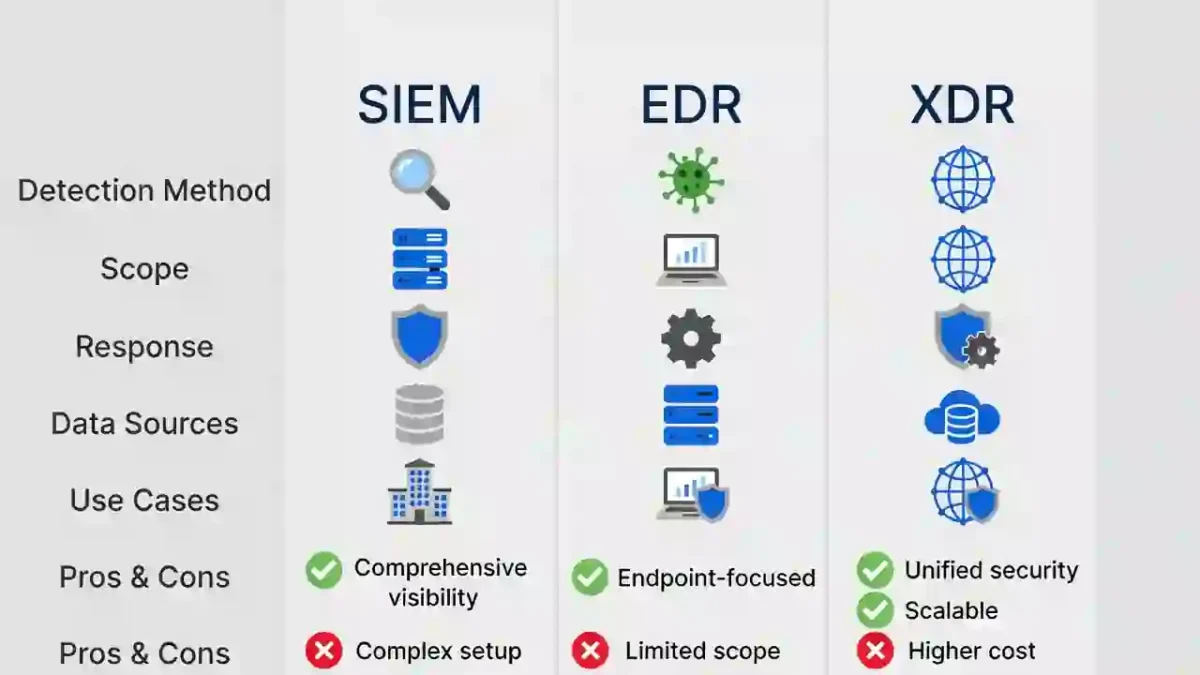
1️⃣ SIEM (Security Information and Event Management)
SIEM platforms centralize logs from:
- Servers
- Endpoints
- Network devices
- Cloud environments
They correlate events to identify suspicious behavior.
By aggregating telemetry across systems, SIEM solutions help reduce:
Improved log visibility strengthens early detection.
2️⃣ EDR (Endpoint Detection and Response)
EDR solutions monitor endpoints such as:
- Workstations
- Laptops
- Servers
- Mobile devices
They detect behavioral anomalies, isolate compromised systems, and provide forensic data.
EDR tools are especially effective against ransomware and credential misuse.
3️⃣ XDR (Extended Detection and Response)
XDR expands visibility beyond endpoints by integrating:
- Network telemetry
- Email security
- Cloud monitoring
- Identity systems
This unified approach reduces alert fatigue and improves investigation speed.
4️⃣ Firewalls
Firewalls inspect network traffic and enforce security rules.
They block unauthorized access and filter suspicious activity before it enters internal networks.
Modern next-generation firewalls include advanced inspection and application awareness.
5️⃣ IDS/IPS (Intrusion Detection and Prevention Systems)
IDS/IPS tools monitor network traffic for malicious patterns.
They detect:
- Known attack signatures
- Abnormal traffic behavior
- Exploit attempts
These systems provide early warning signals for potential breaches.
6️⃣ SOAR (Security Orchestration, Automation, and Response)
SOAR platforms automate repetitive security workflows.
They help:
- Trigger response playbooks
- Escalate high-risk alerts
- Coordinate cross-team actions
Automation reduces manual investigation delays and improves containment speed.
7️⃣ Threat Intelligence Platforms
Threat intelligence tools provide contextual data such as:
- Indicators of compromise (IOCs)
- Vulnerability insights
- Emerging attack techniques
According to the Verizon Data Breach Investigations Report:
Early visibility into threat trends strengthens defensive posture.
How Essential Cybersecurity Tools Work Together
No single tool provides complete protection.
Effective security operations integrate:
- SIEM for centralized visibility
- EDR for endpoint protection
- XDR for cross-environment detection
- SOAR for automation
- Threat intelligence for context
This layered approach reduces dwell time and limits attacker movement.
Choosing the Right Essential Cybersecurity Tools
When selecting tools, organizations should consider:
- Scalability
- Integration capabilities
- Cloud compatibility
- Automation features
- Reporting and analytics
Tools should align with business size, risk profile, and compliance requirements.
Final Thoughts
Essential cybersecurity tools provide the visibility and automation required to defend modern digital environments.
SIEM, EDR, XDR, and supporting technologies work together to improve detection, reduce response time, and strengthen resilience.
Organizations that strategically deploy and integrate these tools significantly reduce operational risk and improve security maturity.