UK Cyber Security and Resilience Bill 2026: 7 Key Changes
The UK Cyber Security and Resilience Bill 2026 is best understood as an update to the UK’s existing Network and Information Systems regime, not as a completely separate system. The government’s own bill materials say it reforms and adds to the Network and Information Systems Regulations 2018, with the stated aim of improving protection for services the public relies on in daily life. The bill factsheets say it was introduced to Parliament on 12 November 2025, and the UK Parliament site now shows the bill at report stage in the Commons.
That matters because the broad direction is no longer speculative. The government has already published a full set of Cyber Security and Resilience Bill factsheets covering scope, supplier designation, incident reporting, data centres, managed service providers, enforcement, and government powers. For operators of essential services, the practical question is no longer whether reform is coming. It is whether current governance, supplier oversight, incident escalation, and reporting workflows are ready for the model the bill is pointing toward.
Table of Contents

What UK Cyber Security and Resilience Bill 2026 means now
The current NIS framework already applies to operators of essential services in sectors such as energy, transport, health, drinking water, and digital infrastructure, as well as some digital services. The government’s Summary of the Bill says the new bill is designed to modernise that framework so it better reflects today’s cyber-risk environment, including stronger dependence on digital infrastructure and third-party service providers. That is why this topic sits as much inside operations and supplier management as it does inside compliance.
This also explains why internal links such as UK Incident Reporting Rules and Incident Response Deadlines US UK fit naturally here. The bill is not only about statutory language. It is about the practical question of how quickly a serious cyber event is detected, escalated, and reported once a service is at risk.
1. More organisations will fall into scope
One of the clearest changes in the UK Cyber Security and Resilience Bill 2026 is scope. The government’s Futureproofing factsheet says the bill will bring data centres, large load controllers, and medium and large managed service providers that meet the bill’s thresholds into scope of the NIS Regulations. It also says further entities judged essential to the day-to-day functioning of UK society or the economy could later be added through secondary legislation.
For essential services, that is a significant shift. It moves the law closer to the real structure of service delivery, where resilience often depends on platforms, hosting environments, and operational support providers that sit one layer behind the public-facing organisation. The older model left more of that dependency outside the centre of the legal framework. The new model is much less willing to treat those dependencies as somebody else’s problem.
2. Supplier risk becomes more visible
The bill also gives regulators a more direct way to deal with concentrated supplier risk. The government’s Designating critical suppliers factsheet says regulators will be able to designate critical suppliers so that the most important suppliers to essential and digital services can be subject to mandatory cyber requirements. The same factsheet explains that this is aimed at suppliers whose disruption could significantly affect essential or digital services and, through that disruption, have a serious impact on the economy or on the day-to-day functioning of society in the UK.
That is a practical recognition of how modern service failure often happens. A hospital, water provider, transport operator, or digital platform may appear well managed on paper and still be badly exposed through a small number of external providers. This is where internal links like Vendor Security Questionnaire Template and Supplier Cybersecurity Contract Template belong naturally. The bill’s supplier logic becomes much easier to act on once procurement, legal, and cyber teams treat supplier assurance as part of resilience rather than as a standalone purchasing task.
3. UK Cyber Security and Resilience Bill 2026 changes incident reporting
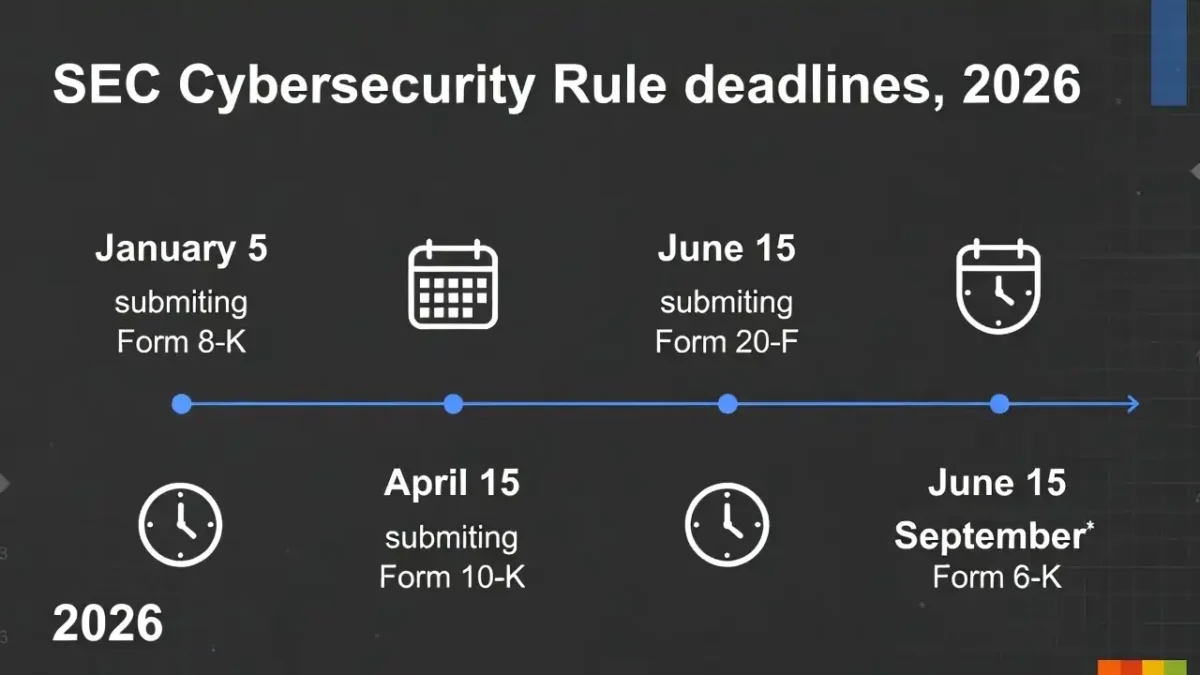
The incident-reporting provisions are likely to be the most visible operational change. The government’s Incident reporting factsheet says more forms of harmful cyber breaches will have to be reported, including successful ransomware, pre-positioning, and spyware incidents likely to have significant impacts in the UK even if visible disruption has not yet happened. It also says the bill introduces a two-stage reporting structure: a light-touch notification within 24 hours, followed by a fuller report within 72 hours, with the NCSC informed at the same time as regulators.
That is not just a procedural tweak. It changes what counts as “early enough.” Under this model, the hard part is not simply filling in a form. It is recognising quickly enough that an event has crossed into something potentially reportable. That is why Mean Time to Detect: 5 Proven Ways to Reduce Cyber Risk, Reduce Detection Time Regulatory Deadlines Risk, and Data Breach Timeline Template are useful internal links here. Once the reporting model rewards earlier visibility, detection speed stops being just a SOC metric and becomes part of compliance readiness.
4. Data centres and managed service providers become much more important
Two of the most consequential scope expansions are data centres and managed service providers. The government’s Data centres factsheet says the bill will bring data centres into scope by classifying data infrastructure as a relevant sector and data centres as an essential service. The Relevant managed service providers factsheet says medium and large MSPs that meet the bill’s definition of a relevant managed service provider will also come into scope and will be required to have appropriate and proportionate measures in place and report significant incidents to their regulator.
For essential service operators, that matters even if they are not themselves a data-centre operator or MSP. It means some of the external providers they rely on may soon face direct cyber obligations of their own. Over time, that should improve baseline resilience and visibility. But it also means procurement and supplier-governance questions will become more important, not less. That is why Cyber Essentials for UK Government Contracts also fits here as an internal link: across the UK, cyber requirements are increasingly turning into commercial and assurance requirements, not just internal technical controls.
5. Government and regulators get stronger coordination powers
The bill is not only about broader scope and quicker reporting. It also gives government stronger coordination tools. The government’s Power to direct regulated entities factsheet says the Secretary of State will be able to direct regulated entities to take necessary and proportionate action in response to imminent or live threats that put UK national security at risk. The companion Power to direct regulators factsheet says the Secretary of State will also be able to direct NIS regulators themselves to take action in response to such threats.
That is an important change in tone as well as law. The bill is being framed as a national-resilience instrument, not just an administrative update. For essential services, this means cyber governance should be read less as an IT matter and more as part of a wider public-interest and national-security framework. This is also where Board-Level Cybersecurity Metrics Guide fits naturally, because the bill’s logic clearly pushes cyber risk upward into executive and board-level accountability.
6. Enforcement and compliance costs become more serious
A broader regime would not matter much without stronger enforcement. The government’s Enforcement factsheet says the bill reforms the enforcement mechanisms in the NIS Regulations with the aim of creating a more effective and proportionate regime and improving compliance. The Cost recovery factsheet adds that regulators will be empowered to recover the full costs of their NIS functions, subject to safeguards such as transparency, consultation, and a prohibition on making a profit from the regime.
The practical message is simple. Under the updated regime, compliance is likely to become more formal, more visible, and harder to defer quietly. The UK is not just widening the legal perimeter. It is also building a framework that regulators can sustain and enforce more credibly over time.
7. Essential services will need stronger governance, not just better tooling
Taken together, the changes in the UK Cyber Security and Resilience Bill 2026 point to a governance shift more than a tooling shift. Broader scope, earlier reporting, supplier designation, stronger state direction powers, and more explicit enforcement all push cyber resilience into the shared space between operations, procurement, legal, communications, and leadership. The government’s Summary of the Bill makes that clear: the goal is to improve defences around services the public depends on, not simply to add another layer of paperwork.
That is why the strongest internal follow-ons for this article are Board-Level Cybersecurity Metrics Guide, Vendor Security Questionnaire Template, Supplier Cybersecurity Contract Template, and Incident Response Deadlines US UK. They continue the same story from governance to supplier control to reporting speed.

Final take on UK Cyber Security and Resilience Bill 2026
The clearest way to describe the UK Cyber Security and Resilience Bill 2026 is that it updates the NIS regime for the systems the country now actually relies on. It widens scope, brings more of the digital dependency chain into view, moves reporting earlier, strengthens government and regulator coordination powers, and makes enforcement more substantial. The bill is still moving through Parliament, but the practical direction is already clear enough that essential-service operators do not need to wait for the final parliamentary step before preparing.
For most organisations, the safest next move is not a dramatic overhaul. It is disciplined preparation: map critical suppliers, tighten early escalation, review whether contracts support faster notification and evidence sharing, and make sure cyber, legal, procurement, and leadership teams are working from the same assumptions. That is the most practical reading of where the bill is heading.