Vendor Security Questionnaire Template: 7 Key Questions
A Vendor Security Questionnaire Template helps organizations assess the cybersecurity posture of third-party vendors before sharing sensitive data, granting access, or signing contracts. In both the US and UK, vendor reviews are now a core part of third-party risk management, especially where vendors handle customer data, connect to internal systems, or support regulated operations. The NIST Cybersecurity Framework emphasizes supply-chain and external dependency risk, while the UK National Cyber Security Centre treats supply-chain security as a major part of modern cyber resilience. For internal context, this topic fits naturally with your Compliance & Reporting and Information Security Guide.
A strong Vendor Security Questionnaire Template gives procurement, security, legal, and risk teams a consistent way to compare vendors and document due diligence. Instead of relying on marketing claims, buyers can ask structured questions about governance, access control, incident response, vulnerability management, and compliance. That also makes the process easier to explain internally, especially for leadership teams already focused on measurable cyber risk, which is why this post also connects well to your Board-Level Cybersecurity Metrics Guide and Cybersecurity Metrics.
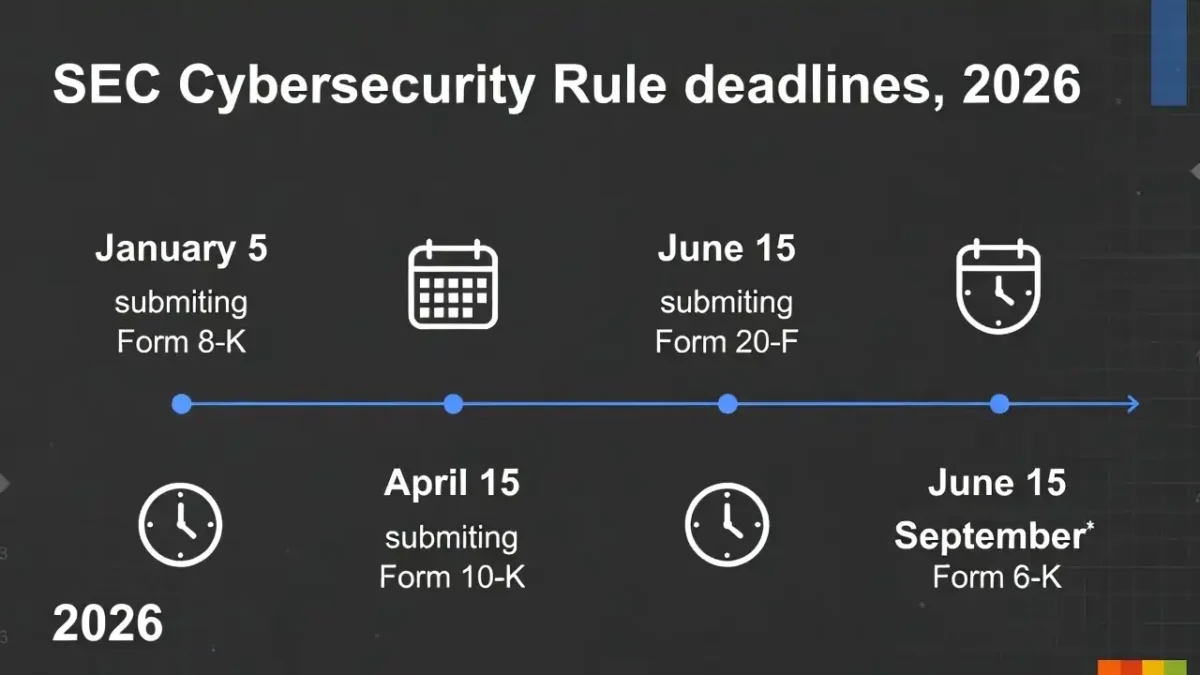
The practical goal of a Vendor Security Questionnaire Template is not to create paperwork for its own sake. It is to help buyers identify weak controls before a vendor becomes a real source of operational, legal, or reputational exposure. That matters more now because cybersecurity obligations increasingly intersect with reporting timelines, executive oversight, and regulatory scrutiny. Internally, that makes this article a strong companion to your SEC Cyber Rule Timeline 2026 and CIRCIA 72-Hour Reporting Rule.
Table of Contents
What Is a Vendor Security Questionnaire?
A Vendor Security Questionnaire Template is a structured set of questions used to evaluate the security practices of a third-party provider. It is commonly used for SaaS vendors, cloud providers, consultants, managed service providers, payment processors, and any supplier that may process, store, or access sensitive business information. The broad idea aligns with established third-party and supply-chain security principles in the NIST Cybersecurity Framework and the NCSC supply-chain security guidance. For internal readers, this section also pairs well with your Cybersecurity Best Practices post.
A good questionnaire helps buyers move beyond vague assurances. Instead of asking whether a vendor “takes security seriously,” it asks whether the vendor enforces MFA, encrypts sensitive data, runs vulnerability scanning, maintains an incident response plan, and undergoes independent audits. In practice, that kind of structured review turns security from a vague trust issue into a measurable risk issue, which also aligns with the way your site covers Metrics Comparison and MTTD vs MTTR vs MTTC vs Dwell Time.
Why US and UK Buyers Use Security Questionnaires
US and UK buyers use a Vendor Security Questionnaire Template because third-party exposure is now a major business risk. A vendor can become the weak link between internal systems, regulated data, customer trust, and incident response obligations. That is why vendor review is now common in procurement, legal review, privacy review, and security review. Externally, this fits with NIST and NCSC supply-chain guidance; internally, it connects naturally to your Compliance & Reporting hub.
There is also a regulatory reason. Buyers increasingly need evidence that they reviewed supplier risk before onboarding a third party. Even where a law does not prescribe one exact form, governance expectations increasingly favor documented due diligence. That is especially true where vendors may affect breach reporting, materiality decisions, or operational resilience. Internally, this is why the post also pairs well with Reduce Detection Time Regulatory Deadlines Risk and SEC Cyber Rule Timeline 2026.
For many organizations, a Vendor Security Questionnaire Template also improves consistency. Without one, different teams ask different things, compare vendors unevenly, and miss obvious gaps. A shared template creates repeatability across onboarding and reassessment. This is the same logic behind using standardized metrics internally, which makes Cybersecurity Metrics and SOC Efficiency Metrics 2026 helpful related reads.
Vendor Security Questionnaire Template Structure
A practical Vendor Security Questionnaire Template should be organized into clear sections rather than one long list of random questions. That makes it easier for vendors to answer, easier for buyers to review, and easier to compare responses across suppliers. Most strong questionnaires follow a structure that covers governance, access control, data protection, vulnerability management, incident response, and compliance. That kind of structured approach also matches the disciplined operational style reflected in your Cybersecurity Incident Response Timeline article.
It also helps to align the questionnaire loosely with known frameworks instead of inventing categories from scratch. Buyers often map questions to ideas from NIST, ISO/IEC 27001, or SOC 2. The questionnaire does not need to reproduce those frameworks line by line, but the structure should reflect the controls buyers actually care about. Internally, this also pairs well with your Information Security Guide.
7 Key Questions in a Vendor Security Questionnaire Template
1. Who owns security in the vendor organization?
Every Vendor Security Questionnaire Template should start by identifying accountability. Buyers should ask whether the vendor has a named security lead, a documented security program, and executive oversight for cyber risk. If a vendor cannot clearly state who owns security, that is a warning sign. Internally, this also aligns with the governance themes in your Board-Level Cybersecurity Metrics Guide.
2. How is access controlled?
Access control should be one of the strongest sections in any Vendor Security Questionnaire Template. Buyers should ask whether the vendor enforces MFA, reviews privileged access, disables stale accounts, and limits administrative permissions. Access control weakness often turns small errors into major incidents. For internal support, this point also pairs well with Passkeys vs MFA vs SMS 2FA, which is directly relevant to authentication strength.
3. How is sensitive data protected?
A good Vendor Security Questionnaire Template should ask how the vendor encrypts data at rest and in transit, segregates customer data, handles backups, and manages retention and deletion. If the vendor processes regulated or confidential information, this section becomes even more important. Internally, this section also fits naturally with your Information Security Guide and Cybersecurity Best Practices.
4. How are vulnerabilities identified and patched?
Buyers should ask whether the vendor performs vulnerability scanning, runs penetration tests, tracks remediation deadlines, and has a documented patching process. This is one of the most useful parts of a Vendor Security Questionnaire Template because it shows whether the vendor treats security as an ongoing process. For internal support, this also pairs well with KEV vs CVSS Patch Priority, which is directly relevant to patch prioritization logic.
5. What is the incident response process?
A strong Vendor Security Questionnaire Template should ask whether the vendor has a written incident response plan, how incidents are escalated, how customers are notified, and what timelines exist for reporting. If a vendor cannot explain its response process, buyers may have to assume notification will be slow and chaotic during a real incident. Internally, this section links naturally to Cybersecurity Incident Response Timeline and Reduce Detection Time Regulatory Deadlines Risk.
6. What certifications or independent reviews exist?
Many buyers use a Vendor Security Questionnaire Template to ask whether the vendor has certifications or audit reports such as SOC 2, ISO/IEC 27001, or independent penetration testing results. Certifications do not replace real review, but they can provide added confidence and reduce guesswork. Internally, this also fits with your Compliance & Reporting content.
7. How is ongoing risk monitored?
The best Vendor Security Questionnaire Template does not treat security as a one-time onboarding checkbox. Buyers should ask how often controls are reassessed, whether material changes are disclosed, and how security incidents or significant control failures are communicated over time. This matters because vendor risk changes after onboarding, not just before it. Internally, that long-term measurement mindset also connects naturally to Cybersecurity Metrics and Industry Benchmarks 2026: Critical Response Insights.

Example Vendor Security Questionnaire Template
A simple Vendor Security Questionnaire Template can start with company profile questions, then move into governance, access control, data protection, vulnerability management, incident response, and compliance evidence. A practical example would ask who owns cyber security, whether MFA is enforced, whether customer data is encrypted, how critical vulnerabilities are patched, how customers are notified after incidents, and whether any independent certifications or audits exist. The goal is not to create a massive list. The goal is to surface meaningful security signals early. Internally, this also pairs well with Cybersecurity Time and Compliance & Reporting.
Best Practices for Vendor Security Reviews
Using a Vendor Security Questionnaire Template well requires more than sending a form and filing the answers away. Buyers should verify important claims with evidence, review answers in context, and apply more scrutiny to vendors with sensitive access or critical functions. A short questionnaire may be enough for a low-risk marketing tool, but not for a cloud provider holding sensitive customer data. That same risk-based logic is visible across your internal content on Cybersecurity Metrics and Board-Level Cybersecurity Metrics Guide.
It also helps to reassess vendors over time instead of treating onboarding as the end of the process. Security posture can change after mergers, staffing changes, architectural changes, incidents, or new regulations. Buyers should define which vendors require annual reassessment, which ones require event-driven review, and which ones need contractual notification obligations. Internally, that ongoing review mindset fits naturally with SOC Efficiency Metrics 2026 and How to Reduce Cybersecurity Detection Time.

Final Verdict
A well-designed Vendor Security Questionnaire Template helps US and UK buyers reduce third-party cyber risk before vendors become embedded in the business. It gives security, procurement, legal, and leadership teams a common language for evaluating vendor controls, comparing suppliers, and documenting due diligence. Externally, that approach aligns with NIST and NCSC supply-chain guidance; internally, it fits neatly with Compliance & Reporting and Board-Level Cybersecurity Metrics Guide.
The strongest vendor review programs do not use a questionnaire as a paperwork ritual. They use it as the start of a risk conversation. That means asking better questions, verifying the answers that matter most, and adapting scrutiny based on the vendor’s real access, data exposure, and business criticality.
FAQ
What is a vendor security questionnaire?
A vendor security questionnaire is a structured set of questions used to assess a third party’s cybersecurity practices before or during a business relationship. It is commonly used in procurement, security review, and compliance review. For internal context, this also fits with Compliance & Reporting.
Why do companies use a Vendor Security Questionnaire Template?
Companies use a Vendor Security Questionnaire Template to evaluate supplier risk consistently, compare vendors fairly, and document due diligence before granting access or sharing sensitive data. For related internal reading, see Cybersecurity Best Practices.
Are vendor security questionnaires required by law?
Not always in one exact format, but many frameworks and risk programs strongly support supplier review and due diligence. In regulated environments, documented vendor review is often a practical expectation even when no single universal questionnaire is mandated. For internal support, this also pairs with Compliance & Reporting.
How often should vendors be reassessed?
That depends on the vendor’s criticality, access, and data sensitivity. High-risk vendors are commonly reassessed annually or whenever there is a major change, incident, or control failure. For internal continuity, this also aligns with Board-Level Cybersecurity Metrics Guide.