Passkeys vs MFA vs SMS 2FA: Which Stops Phishing Best?
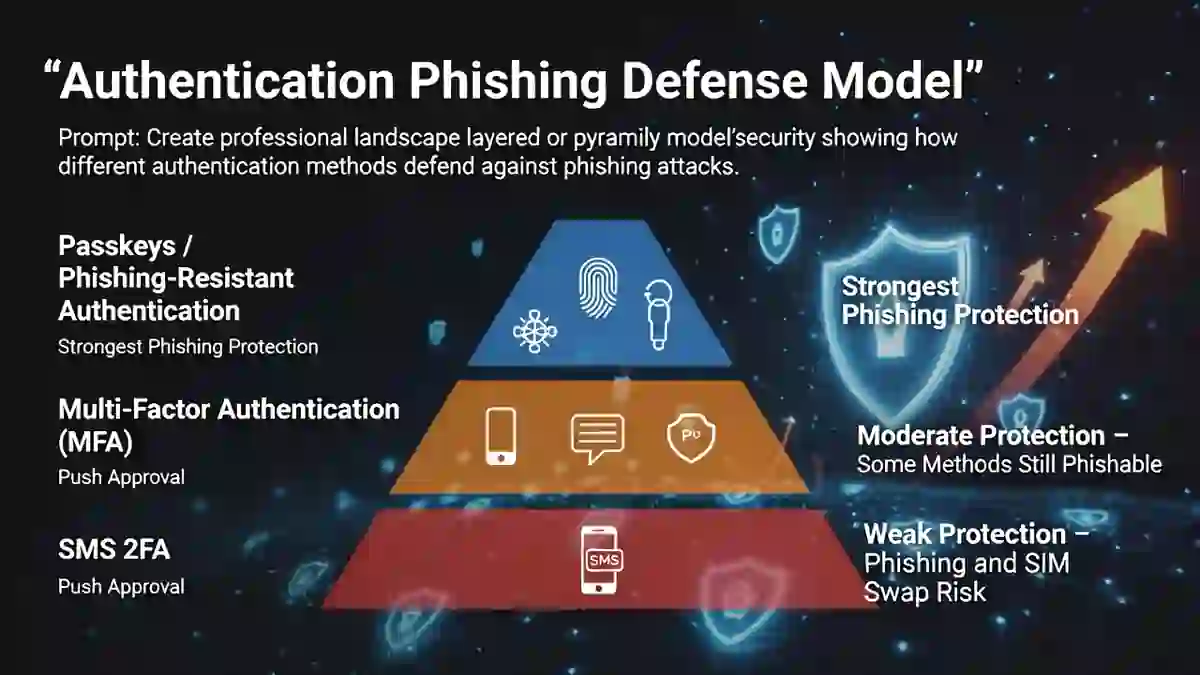
If you are comparing Passkeys vs MFA vs SMS 2FA, you are really asking which login method best resists modern phishing attacks. The current answer from major security guidance is clear: passkeys and other phishing-resistant MFA methods are stronger than traditional MFA that relies on one-time codes, and SMS 2FA is the weakest of the three against phishing and telecom-based attacks. The FIDO Alliance says passkeys provide phishing-resistant passwordless sign-in based on public-key cryptography, while Microsoft’s phishing-resistant MFA guidance explicitly treats phishing-resistant MFA as a distinct security goal. (fidoalliance.org)
This matters because many organizations still say “we have MFA” as if all MFA stops phishing equally well. It does not. A user can still be tricked into giving away an SMS code or an authenticator app code on a fake website, but properly implemented passkeys are designed to resist that kind of phishing flow. The FIDO Alliance says passkeys replace passwords with cryptographic key pairs and provide phishing-resistant sign-in, and Microsoft says phishing-resistant MFA is part of stronger identity protection. (learn.microsoft.com)
The best short answer to Passkeys vs MFA vs SMS 2FA is this: passkeys stop phishing best, phishing-resistant MFA is the right strategic standard, and SMS 2FA should be treated as a weaker fallback, not the gold standard. Even NIST’s digital identity guidance has long documented risks around out-of-band authenticators such as SMS, including the need for protected channels and resistance to man-in-the-middle attacks, while industry and vendor guidance now strongly favors phishing-resistant methods. (pages.nist.gov)
For internal site structure, this article fits naturally with your live pages on Compliance & Reporting, Cybersecurity Metrics, Board-Level Cybersecurity Metrics Guide, and Cybersecurity Best Practices.
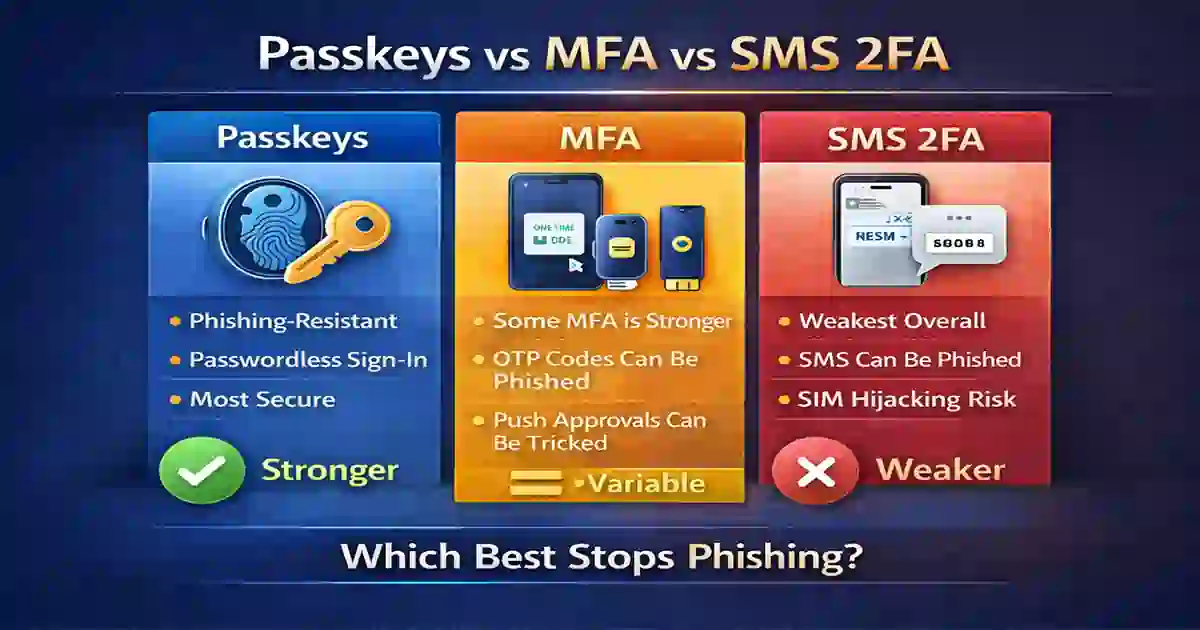
Table of Contents
What Are Passkeys?
Passkeys are a passwordless sign-in method built on public-key cryptography. The FIDO Alliance says passkeys replace passwords with cryptographic key pairs and can be synced across devices or bound to a specific device. The private key stays with the user’s device, and the service uses the public key for authentication. That design is what makes passkeys far more resistant to credential theft and phishing than password-and-code workflows. (fidoalliance.org)
The key advantage in the Passkeys vs MFA vs SMS 2FA comparison is that passkeys are origin-bound. In practical terms, a fake phishing site cannot easily trick the authenticator into signing for the wrong domain the way it can trick a person into typing a password or one-time code. That is why the FIDO Alliance describes passkeys as phishing-resistant, and why major platforms keep moving toward them. (fidoalliance.org)
For internal readers, this section also pairs well with your live Information Security Guide and Essential Cybersecurity Tools.
What is MFA?
MFA, or multi-factor authentication, means using more than one factor to verify identity, such as something you know, something you have, or something you are. The problem is that “MFA” is a broad category, not a single technology. Some MFA methods are much stronger than others. Microsoft specifically distinguishes phishing-resistant MFA from weaker MFA patterns, which is an important point many security teams still miss. (learn.microsoft.com)
In the Passkeys vs MFA vs SMS 2FA debate, generic MFA often means one-time passcodes from an authenticator app, push approvals, hardware keys, or smart cards. Some of those are stronger than others. The category is useful, but it can also be misleading because an organization can truthfully say “we use MFA” even if its users are still vulnerable to phishing kits that relay credentials and OTPs in real time. Microsoft’s guidance and current enterprise security practice increasingly push organizations toward phishing-resistant MFA, not just any MFA. (learn.microsoft.com)
This section also connects naturally to your internal Cybersecurity Metrics and Board-Level Cybersecurity Metrics Guide, because authentication strength is a governance and risk issue as much as a technical one.
What is SMS 2FA?
SMS 2FA is a common two-factor method where a one-time code is sent by text message to the user’s phone number. It is still widely used because it is familiar and easy to deploy, but it is also the weakest option in the Passkeys vs MFA vs SMS 2FA comparison when phishing resistance is the priority. NIST SP 800-63B has long discussed the risks and requirements around out-of-band authenticators, and more recent industry commentary has increasingly highlighted telecom interception, SIM swapping, and relay attacks as major concerns. (pages.nist.gov)
SMS 2FA is better than password-only login, but it is not phishing-resistant. A user can still be tricked into entering the code on a fake site, and the code can potentially be intercepted or redirected through telecom-related attacks. That is why modern guidance increasingly treats SMS as a weaker fallback rather than the end state for strong authentication. (pages.nist.gov)
For internal relevance, this section also pairs well with your live Cybersecurity Basics and Cybersecurity Best Practices.
Passkeys vs MFA vs SMS 2FA: Main Difference
The main difference in Passkeys vs MFA vs SMS 2FA is not simply convenience. It is phishing resistance.
Passkeys are designed to be phishing-resistant because the authentication flow is based on cryptographic keys tied to the legitimate service. Generic MFA can be strong or weak depending on the factor used. SMS 2FA is the weakest against phishing because users can be tricked into handing over the code and because the channel itself has extra risk. The FIDO Alliance and Microsoft both support the move toward phishing-resistant authentication, not just basic MFA. (fidoalliance.org)
That means the Passkeys vs MFA vs SMS 2FA question is really about whether your authentication system is phishing-resistant by design, phishing-resistant only in some cases, or still vulnerable to common phishing workflows. Security teams that treat all MFA as equal often overestimate their protection. (learn.microsoft.com)
This section also works well with your internal Compliance & Reporting and Cybersecurity Time homepage.

7 Critical Facts About Passkeys vs MFA vs SMS 2FA
1. Passkeys are phishing-resistant by design
The FIDO Alliance says passkeys provide phishing-resistant sign-in security. That is the strongest single fact in this comparison. (fidoalliance.org)
2. Not all MFA is phishing-resistant
Microsoft explicitly uses the phrase phishing-resistant MFA, which shows that some MFA methods meet that bar and others do not. (learn.microsoft.com)
3. SMS 2FA is better than passwords alone, but weaker than modern alternatives
NIST SP 800-63B documents the security requirements and risks around out-of-band authenticators, which is one reason the market has shifted toward stronger methods. (pages.nist.gov)
4. Passkeys improve security and usability at the same time
The FIDO Alliance emphasizes that passkeys are not only more secure, but also faster and easier than passwords plus codes. That is one reason adoption is accelerating. (fidoalliance.org)
5. Generic OTP-based MFA can still be phished
Modern phishing kits and adversary-in-the-middle attacks can capture passwords and one-time codes in real time. That is why security guidance now focuses on phishing-resistant authentication, not only on “having MFA.” This is an inference supported by Microsoft’s phishing-resistant MFA guidance and the security rationale behind passkeys. (learn.microsoft.com)
6. SMS 2FA carries additional telecom and SIM-related risk
Beyond ordinary phishing, SMS 2FA also carries risks tied to number porting, SIM swapping, and message interception concerns. That is why it is increasingly treated as a lower-assurance fallback. This is an inference consistent with NIST’s treatment of out-of-band methods and current industry direction. (pages.nist.gov)
7. The best strategic target is phishing-resistant authentication, not just MFA compliance
Organizations should stop asking only “Do we have MFA?” and start asking “Is our authentication phishing-resistant?” That is the more mature question behind the entire Passkeys vs MFA vs SMS 2FA comparison. (learn.microsoft.com)
This section also supports internal links to Cybersecurity Metrics, Board-Level Cybersecurity Metrics Guide, and Cybersecurity Best Practices.
Which One Stops Phishing Best?
The best answer to Passkeys vs MFA vs SMS 2FA is clear: passkeys stop phishing best.
That is because passkeys are built on cryptographic authentication that is tied to the correct service and does not depend on the user typing a reusable secret or a phishable one-time code into a webpage. By contrast, generic MFA can still be vulnerable if it depends on OTP entry or approval flows that users can be tricked into authorizing. SMS 2FA is the weakest because it is both phishable and dependent on a less secure delivery channel. (fidoalliance.org)
If the only question is “Which method best stops phishing?” then the ranking is usually:
- Passkeys
- Phishing-resistant MFA methods
- Traditional OTP-style MFA
- SMS 2FA
That ranking is a practical synthesis of the current guidance from the FIDO Alliance, Microsoft, and NIST. (fidoalliance.org)
This section also fits with your internal Information Security Guide and Compliance & Reporting.
What Should Organizations Deploy?
The best strategy is not to ask whether Passkeys vs MFA vs SMS 2FA has a single winner in every environment. The better strategy is to set a target architecture.
For most organizations, the right target is:
- Primary: passkeys or other phishing-resistant MFA
- Secondary: strong non-SMS MFA where passkeys are not yet supported
- Fallback: SMS 2FA only where necessary, and ideally only temporarily
That approach balances security maturity with real-world compatibility. It acknowledges that not every app and workforce is fully ready for passkeys today, but it still moves the organization toward a clearly safer end state. (learn.microsoft.com)
A practical rollout plan usually starts with high-risk users, admin accounts, remote access, and identity platforms first. Then it expands to broader workforce authentication as support improves. This section also supports internal links to your Board-Level Cybersecurity Metrics Guide, Cybersecurity Metrics, and Cybersecurity Best Practices.
Final Verdict
When comparing Passkeys vs MFA vs SMS 2FA, passkeys stop phishing best.
That does not mean all MFA is bad. It means the security industry is moving beyond the old idea that any MFA is equally strong. The better question is whether your authentication is phishing-resistant. On that measure, passkeys lead, stronger phishing-resistant MFA methods follow, and SMS 2FA falls behind. (fidoalliance.org)
For global organizations in 2026, the most practical path is to deploy passkeys where possible, use stronger MFA where passkeys are not yet available, and keep SMS 2FA only as a fallback. That is the clearest answer to Passkeys vs MFA vs SMS 2FA for teams that want to reduce phishing-driven account compromise. (learn.microsoft.com)
FAQ
Are passkeys better than MFA?
Passkeys are a form of strong authentication and are generally better than phishable MFA methods when phishing resistance is the priority. (fidoalliance.org)
Is SMS 2FA still worth using?
Yes, it is better than password-only access, but it is weaker than passkeys and stronger phishing-resistant MFA options. (pages.nist.gov)
Can MFA still be phished?
Yes. Some MFA methods can still be phished, especially those relying on one-time codes or user approvals that can be relayed. (learn.microsoft.com)
What should businesses deploy first?
High-risk users, admins, and identity platforms should usually be first in line for passkeys or other phishing-resistant authentication. (learn.microsoft.com)


