Ransomware Detection Timeline: 6 Critical Stages
Ransomware attacks rarely begin with encrypted files.
Long before systems are locked, attackers move quietly inside networks. They escalate privileges, identify high-value assets, disable protections, and often steal sensitive data before encryption is deployed.
Understanding the ransomware detection timeline helps organizations identify warning signs earlier and reduce operational damage before disruption spreads.
This guide explains the six critical stages of a ransomware attack and highlights where detection and containment efforts are most effective.
Table of Contents
Understanding the Ransomware Detection Timeline
The ransomware detection timeline refers to the structured sequence attackers follow after gaining initial access.
Encryption is usually the final stage — not the first.
Most campaigns include:
- Entry through phishing or stolen credentials
- Establishing continued access
- Expanding internal control
- Exfiltrating sensitive data
- Deploying encryption
- Demanding ransom
Organizations that reduce Mean Time to Detect (MTTD) significantly lower financial and operational impact.
👉 Learn more about Mean Time to Detect Cybersecurity MTTD
Stage 1: Initial Compromise
Attackers typically gain entry through:
- Phishing emails
- Compromised credentials
- Exploited vulnerabilities
- Misconfigured remote services
The Verizon Data Breach Investigations Report consistently identifies credential misuse as a leading cause of breaches:
Early Indicators
- Suspicious login attempts
- Authentication failures
- Unusual geographic access
- Unexpected remote sessions
Strong authentication reduces exposure.
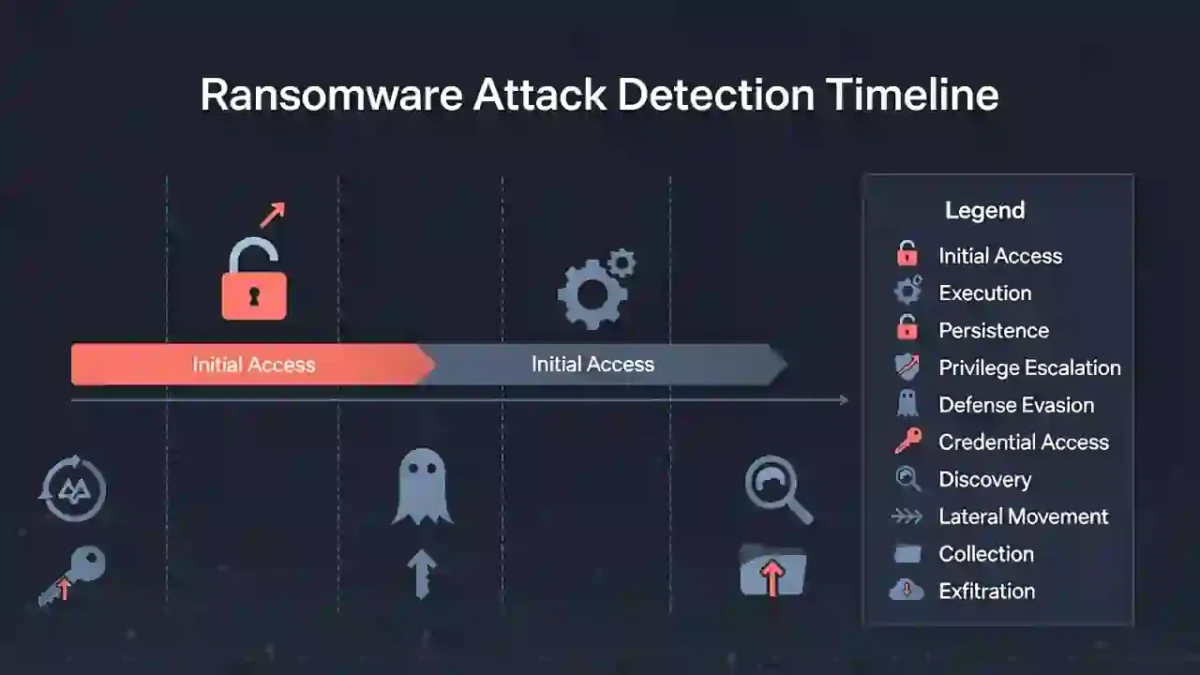
Stage 2: Persistence
Once inside, attackers ensure continued access.
Common methods:
- Creating hidden administrator accounts
- Installing remote access tools
- Modifying startup services
Monitoring account creation and configuration changes can interrupt this stage early.
Stage 3: Privilege Escalation & Lateral Movement
Attackers expand control across systems.
This stage includes:
- Credential harvesting
- Accessing domain controllers
- Moving laterally using legitimate tools
Reducing lateral movement lowers dwell time.
👉 Learn about dwell time:
Network segmentation significantly limits spread.
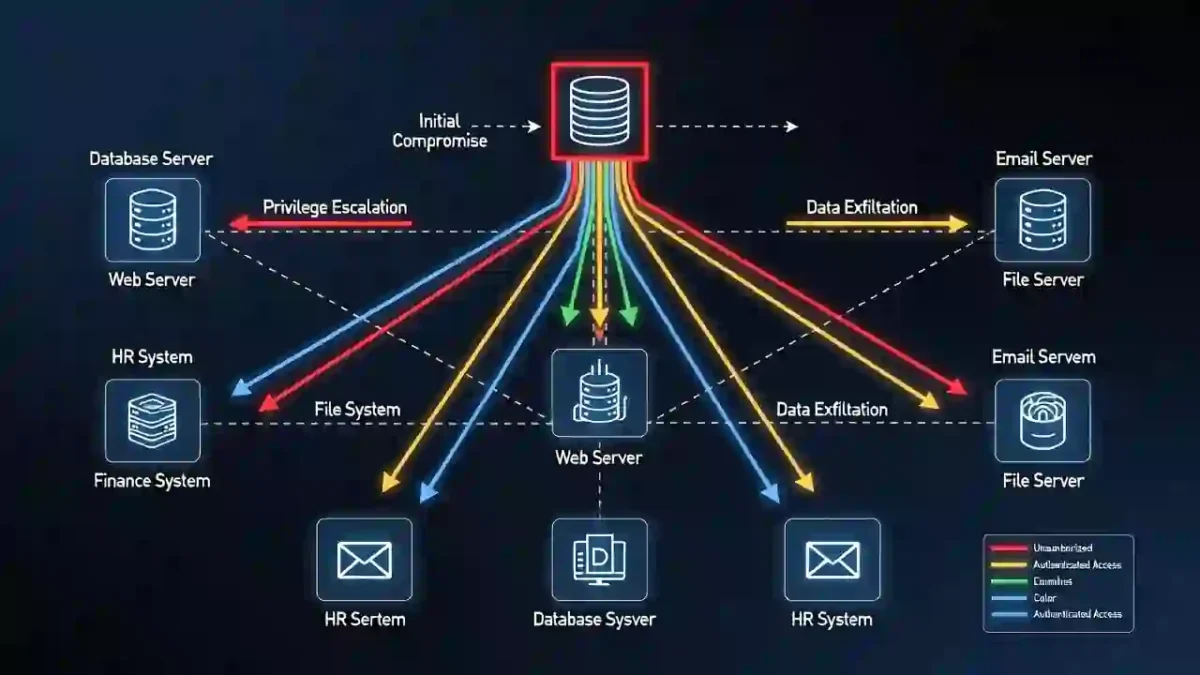
Stage 4: Data Theft
Modern ransomware groups often steal data before encryption.
This enables double extortion.
Warning signs:
- Large outbound data transfers
- Suspicious cloud uploads
- Encrypted outbound traffic
CISA provides ransomware defense guidance here:
Monitoring outbound traffic is critical.
Stage 5: Encryption Deployment
Encryption is the most visible stage.
Indicators include:
- Rapid file modification
- High system resource usage
- Disabled security software
- Ransom messages appearing
By this stage, backup systems may already be compromised.

Stage 6: Containment & Recovery
Containment limits further damage.
Immediate response actions:
- Isolating affected systems
- Disabling compromised accounts
- Blocking malicious IP addresses
- Preserving forensic evidence
NIST Incident Response guidance:
Reducing Mean Time to Respond (MTTR) improves recovery speed.
Reducing Dwell Time
Organizations can reduce exposure by:
- Enforcing multi-factor authentication
- Patching vulnerabilities quickly
- Deploying endpoint detection tools
- Segmenting networks
- Testing backups regularly
Each control interrupts the ransomware detection timeline before full disruption occurs.
Final Thoughts
A ransomware attack follows a predictable pattern.
Encryption is rarely the beginning — it is the result of earlier undetected activity.
Organizations that understand the ransomware detection timeline detect threats earlier, reduce dwell time, and contain incidents before widespread disruption occurs.
Preparedness, layered defenses, and continuous monitoring remain the strongest protection against modern ransomware.