AI and Incident Response Automation: 7 Proven Gains
AI and Incident Response Automation are reshaping cybersecurity operations in 2026.
As ransomware attacks accelerate and regulatory reporting deadlines tighten, manual incident response processes struggle to keep pace. Organizations are increasingly turning to artificial intelligence and automated orchestration platforms to reduce detection delays, contain threats faster, and strengthen compliance readiness.
The result is measurable performance improvement across detection speed, containment time, and regulatory response.
This article explores seven proven gains delivered by AI-driven incident response automation.
(Insert your WordPress Table of Contents block here.)
Table of Contents
What Is AI and Incident Response Automation?
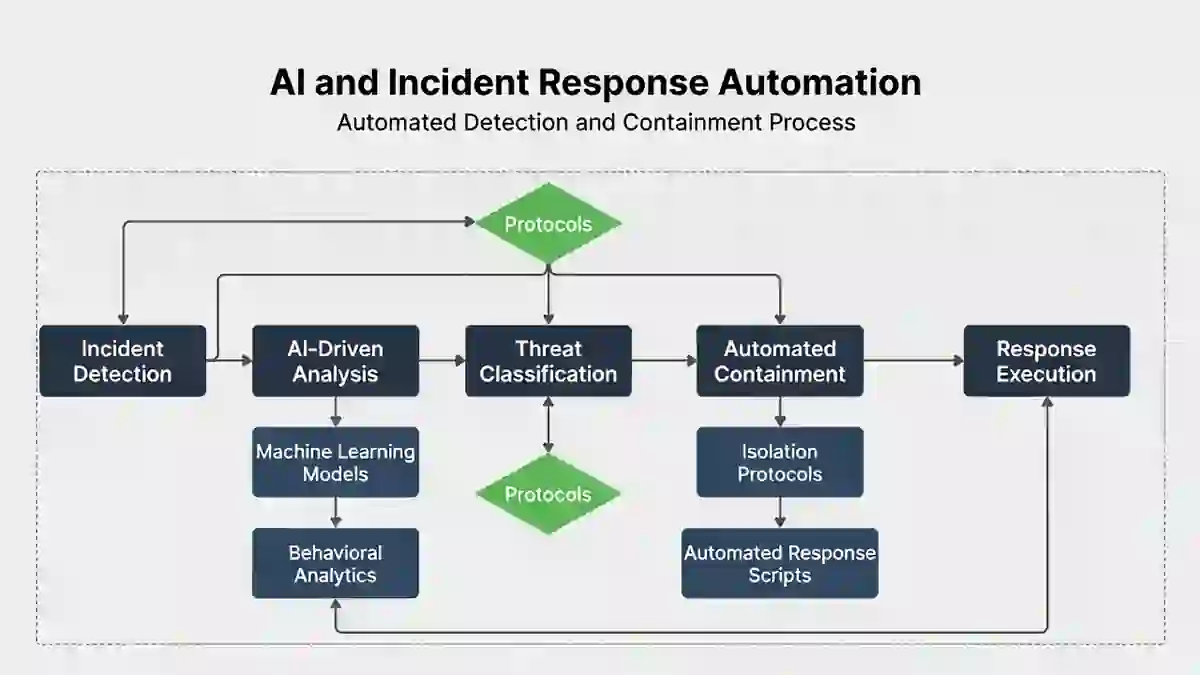
AI and Incident Response Automation refer to the use of machine learning, behavioral analytics, and automated workflows to detect and respond to cyber threats with minimal manual intervention.
These systems integrate with:
- SIEM platforms
- EDR and XDR tools
- Threat intelligence feeds
- SOAR (Security Orchestration, Automation and Response) solutions
Rather than waiting for analysts to manually review alerts, AI models identify patterns, prioritize risks, and trigger predefined response actions automatically.
👉 Related internal guide:
Mean Time to Detect (MTTD)
Why Automation Matters in 2026
Modern ransomware operators move rapidly.
Threat actors can escalate privileges and deploy encryption within hours.
Manual triage processes create delays that attackers exploit.
AI and Incident Response Automation reduce:
- Alert fatigue
- Investigation bottlenecks
- Human escalation delays
- Containment hesitation
Speed now defines resilience.
7 Proven Gains in 2026
1️⃣ Faster Alert Prioritization
AI filters false positives and escalates high-risk incidents immediately.
2️⃣ Reduced Detection Time
Behavioral analytics identify abnormal patterns early, shrinking Mean Time to Detect.
👉 See industry benchmarks
3️⃣ Immediate Endpoint Isolation
Automation quarantines infected systems without waiting for manual approval.
4️⃣ Automated Response Playbooks
Predefined workflows execute containment steps consistently.
5️⃣ Improved Threat Correlation
AI combines low-level alerts into meaningful incidents.
6️⃣ Real-Time Risk Scoring
Dynamic scoring helps security teams prioritize effectively.
7️⃣ Continuous Monitoring & Threat Hunting
Machine learning proactively searches for hidden adversaries.
AI and Incident Response Automation compress the detection-to-containment timeline significantly.
Impact on Detection Speed
Detection speed improves dramatically when AI reduces manual backlog.
Organizations using AI-powered monitoring report:
- Faster anomaly recognition
- Shorter investigation cycles
- Earlier ransomware disruption
Reduced detection time directly influences containment performance and regulatory flexibility.
Impact on Containment Time
Containment becomes faster when automation triggers immediate actions.
Instead of waiting for human approval, systems can:
- Disable compromised accounts
- Block malicious IP addresses
- Isolate infected endpoints
👉 Related: Average Ransomware Containment Time 2026
Shorter containment windows limit financial damage and data loss.
Compliance & Regulatory Benefits
Regulatory frameworks increasingly emphasize rapid incident reporting.
Under:
- CIRCIA 72-hour reporting rule
- SEC cybersecurity disclosure requirements
- UK 72-hour breach notification rule
delayed detection increases legal pressure.
AI and Incident Response Automation support compliance by:
- Accelerating incident classification
- Automatically logging response actions
- Creating audit-ready documentation
- Preserving forensic timelines
Automation gives organizations more time for executive and legal review before reporting deadlines.
Implementation Considerations
While AI offers significant benefits, organizations must manage:
- Integration complexity
- Model tuning requirements
- Overreliance on automation
- Analyst training needs
Automation enhances human decision-making — it does not replace it.
Balanced governance ensures effective outcomes.
Future Outlook
By late 2026, AI-driven automation is becoming standard in mature Security Operations Centers.
Emerging trends include:
- Predictive attack modeling
- Automated low-risk containment
- AI-assisted compliance reporting
- Self-healing network architectures
AI and Incident Response Automation will continue to redefine cybersecurity timing metrics.
Final Thoughts
AI and Incident Response Automation deliver measurable, proven gains in detection speed, containment time, and compliance readiness.
Organizations adopting automation achieve:
- Faster response cycles
- Reduced operational disruption
- Stronger regulatory alignment
- Improved executive visibility
In 2026, cybersecurity timing determines resilience.
Automation is no longer optional — it is strategic.


