CISA KEV This Week: Vulnerabilities Actively Exploited Right Now
CISA KEV This Week is one of the most useful recurring topics for security teams, IT leaders, and risk managers because it focuses on vulnerabilities that are already being exploited in the wild, not just theoretically dangerous flaws. CISA says the Known Exploited Vulnerability (KEV) catalog is the authoritative source of vulnerabilities known to have been exploited, and it tells organizations to use the catalog as an input to their vulnerability management prioritization framework.
That makes CISA KEV This Week different from generic vulnerability news. The KEV catalog is not a broad list of all important CVEs. CISA says entries are added when a vulnerability has a CVE identifier, there is reliable evidence of active exploitation, and there is a clear remediation action such as a vendor patch or update.
This week’s topic is especially timely because CISA published two recent KEV alerts in the same week: one on March 3, 2026 adding two vulnerabilities to the catalog, and another on March 5, 2026 adding five more. That means CISA added seven new KEV entries across those two alerts, which is exactly why a weekly KEV roundup can become a high-value recurring series on your site.
For your site’s internal SEO, this post should connect to your Top Cybersecurity Threats to Watch in 2026, Cybersecurity Incident Response Timeline, and How to Reduce Cybersecurity Detection Time guides because all three help readers understand how active exploitation turns into operational risk.

Table of Contents
What CISA KEV This Week means
CISA KEV This Week refers to the latest vulnerabilities newly added to the Known Exploited Vulnerabilities catalog or highlighted in related CISA alerts. CISA says the catalog is maintained to help defenders keep pace with threat activity and better manage vulnerabilities that are already causing real harm.
This is important because many security teams still sort patching mainly by severity score. CISA says organizations should use the KEV catalog as an input to vulnerability prioritization, and it specifically mentions frameworks such as SSVC as useful ways to triage vulnerabilities with exploitation status and business context in mind.
For federal civilian agencies, the catalog carries direct operational weight. CISA says Binding Operational Directive 22-01 requires Federal Civilian Executive Branch agencies to remediate KEV vulnerabilities by the due date to protect federal networks, while also strongly urging all organizations to prioritize timely remediation of KEV catalog vulnerabilities as part of vulnerability management practice.
Why CISA KEV This Week matters now
CISA KEV This Week matters because it helps security teams answer a simple but critical question: what should we patch first right now? The KEV catalog narrows attention to vulnerabilities with evidence of real exploitation, which is much more actionable than a long list of theoretical issues. CISA says the catalog sends a clear message to prioritize remediation on the subset of vulnerabilities causing immediate harm based on adversary activity.
This also makes CISA KEV This Week a strong editorial fit for your website. Your site already covers active threats, breach timing, and detection-response topics through pages like Average Time to Detect Cyber Attack in 2026, Cyber Breach Detection Time, and Industry Benchmarks 2026: Critical Response Insights. A weekly KEV roundup adds a fast-moving threat-intelligence layer that supports those time-based guides.
What changed in CISA KEV This Week
The strongest hook for CISA KEV This Week is that CISA has been actively updating the catalog in March 2026. CISA published an alert on March 3, 2026 saying it had added two known exploited vulnerabilities to the catalog, and another alert on March 5, 2026 saying it had added five more based on evidence of active exploitation.
That kind of weekly movement is exactly why this series works. Your article does not need to pretend every CVE is equally urgent. Instead, CISA KEV This Week should teach readers that the latest catalog additions represent vulnerabilities CISA believes are already being used by attackers and therefore deserve faster review than ordinary backlog items.
The catalog itself also supports this recurring format. CISA’s catalog interface supports time filters such as Last 30 Days, Last 60 Days, Last 90 Days, and Last Year, and older CISA guidance says readers can sort by Date Added to Catalog in descending order to view the newest entries first. That makes it easy to turn CISA KEV This Week into a repeatable post format every week.
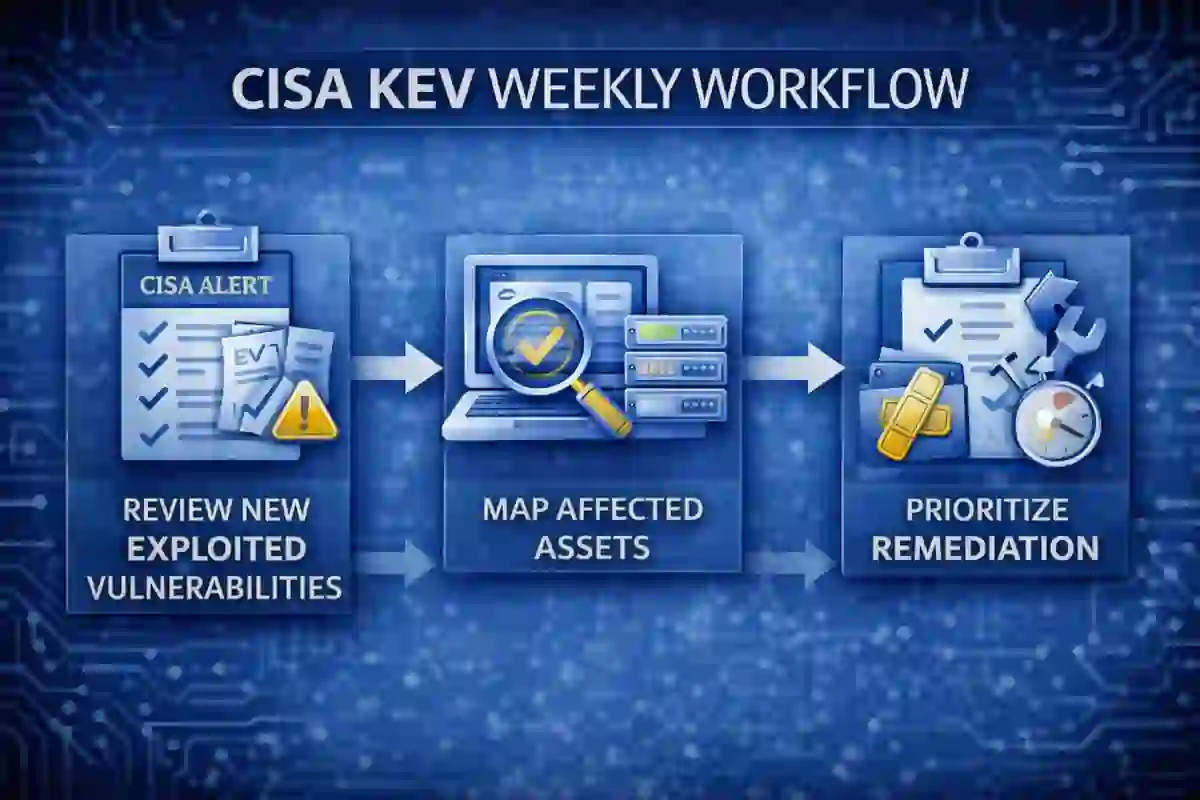
How to use CISA KEV This Week in your patch process
The best CISA KEV This Week post is not just news. It should help readers act.
1. Review the newest KEV additions first
Start each weekly cycle by reviewing the newest KEV entries and related CISA alerts. Because the KEV catalog is updated as new evidence appears, recent additions deserve immediate attention.
2. Map KEV entries to your actual asset inventory
A KEV entry matters most when it affects something you actually run. Map the week’s additions against internet-facing systems, remote access services, VPN appliances, firewalls, cloud workloads, business apps, and endpoints. This step is what turns CISA KEV This Week from awareness into real risk reduction. CISA’s own guidance frames KEV as a prioritization input, not as a disconnected threat feed.
3. Patch exploited vulnerabilities before non-exploited backlog items
If a vulnerability is actively exploited, it generally deserves faster action than a high-scoring issue with no evidence of exploitation. CISA’s message is to focus remediation on vulnerabilities causing immediate harm now. That is the operational value of CISA KEV This Week.
4. Use KEV with business context, not in isolation
CISA points organizations toward using frameworks such as SSVC to combine exploitation status with organizational context. That means your weekly KEV review should consider exposure, asset criticality, exploitability, vendor guidance, and compensating controls.
5. Escalate internet-facing and identity systems immediately
When a newly added KEV affects a perimeter device, remote access tool, or identity-related product, escalation should be faster because those systems often create outsized blast radius. This is where internal links to your Top Cybersecurity Threats to Watch in 2026 and Cybersecurity Best Practices articles help support the patching guidance with broader risk context.
6. Track closure, not just awareness
A weekly KEV review only matters if affected assets are actually remediated. Federal agencies are required to remediate KEV vulnerabilities by the due date under BOD 22-01, and non-federal organizations are strongly encouraged to prioritize them in the same spirit.
7. Turn CISA KEV This Week into a standing weekly meeting
The most practical way to operationalize CISA KEV This Week is to make it part of your regular patch review, threat-intelligence sync, or vulnerability board. That creates a repeatable process instead of ad hoc fire drills. CISA’s own positioning of KEV as a living list supports that recurring workflow.
At this point in the article, add internal links to How to Reduce Cybersecurity Detection Time, Average Time to Detect Cyber Attack in 2026, and Cybersecurity Incident Response Timeline so readers move from exploited-vulnerability awareness into detection and response action.

Who should monitor CISA KEV This Week
CISA KEV This Week is not just for vulnerability management teams. It is relevant to security operations, IT infrastructure, cloud teams, patch management owners, risk managers, and leadership teams that oversee cyber resilience. CISA describes KEV as part of building collective resilience across the cybersecurity community, not only for federal agencies.
This also makes the series globally useful, even though the catalog is run by a U.S. agency. CISA explicitly says it strongly recommends all organizations review and monitor the KEV catalog and prioritize remediation of listed vulnerabilities to reduce the likelihood of compromise by known threat actors.
CISA KEV This Week FAQ
What is CISA KEV This Week?
CISA KEV This Week is a recurring way to review the newest entries in CISA’s Known Exploited Vulnerabilities catalog and the latest CISA alerts covering vulnerabilities actively exploited in the wild.
Why is the KEV catalog more useful than a normal CVE list?
Because KEV focuses on vulnerabilities with evidence of active exploitation and a clear remediation path, which makes it more actionable for weekly prioritization.
Does BOD 22-01 apply to private companies?
The directive directly applies to Federal Civilian Executive Branch agencies, but CISA strongly urges all organizations to prioritize KEV remediation as part of vulnerability management practice.
How often does CISA update the KEV catalog?
CISA says it adds vulnerabilities when they meet the required conditions for catalog inclusion, which means updates happen as new qualifying exploitation evidence appears rather than on a fixed monthly schedule.
Final thoughts
CISA KEV This Week is a strong recurring pillar topic for your website because it combines real-time threat relevance, practical patching guidance, and ongoing search demand around actively exploited vulnerabilities. It also fits naturally with your existing content on detection speed, incident timelines, and current threat trends.
The best version of CISA KEV This Week on your site should do three things every week: show what changed, explain why it matters, and tell readers what to patch first. That gives search engines a clear recurring series and gives readers a practical reason to return. CISA’s own guidance supports exactly that kind of repeatable prioritization approach.


