Cyber Essentials 2026 Changes Explained for UK Businesses
Cyber Essentials 2026 Changes Explained is now an important topic for UK businesses preparing for the next update to the UK’s baseline cyber certification. Many organisations use Cyber Essentials to strengthen basic security, improve customer trust, and stay eligible for public sector and supply-chain opportunities.
The reason Cyber Essentials 2026 Changes Explained matters so much is simple. Businesses do not just want to know what Cyber Essentials is. They want to know what is changing, what could cause failure, and what they should fix before the 2026 update takes effect.
The NCSC Cyber Essentials overview explains that Cyber Essentials remains a government-backed scheme built around five technical controls. The NCSC resources page also confirms that the 2026 updates are available as a preview and are scheduled to be adopted on 27 April 2026.
For your internal SEO cluster, this article should also connect to your Compliance & Reporting, Incident Response Deadlines US UK, and SEC vs UK Cyber Reporting Deadlines pages.
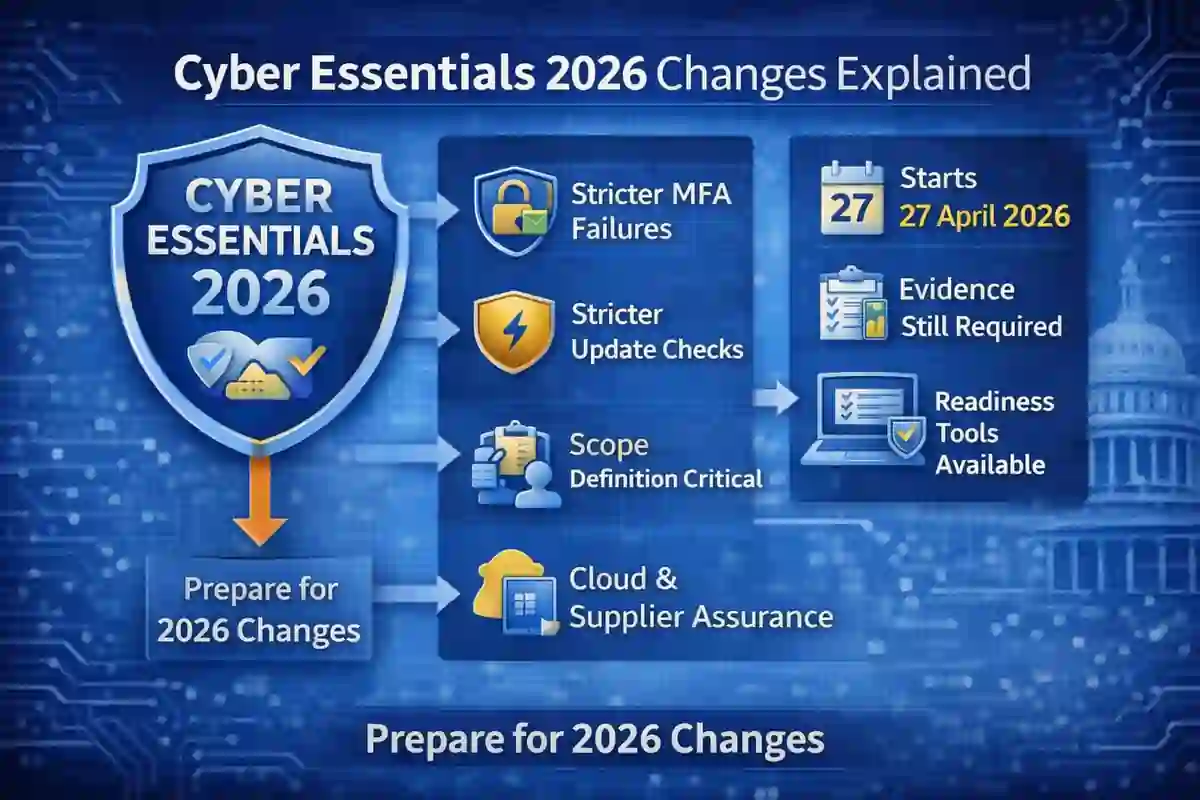
Table of Contents
What Cyber Essentials is
Cyber Essentials is a UK government-backed certification scheme designed to help organisations defend against common online threats. The framework focuses on five core technical controls: firewalls, secure configuration, security update management, user access control, and malware protection.
The GOV.UK Cyber Essentials scheme overview says an up-to-date certificate can help businesses bid for certain government contracts where financial or personal data is involved. That makes Cyber Essentials relevant not only to IT teams, but also to procurement, operations, compliance, and leadership teams.
Why Cyber Essentials 2026 Changes Explained matters
Cyber Essentials 2026 Changes Explained matters because the 2026 update is not just a wording refresh. It affects how organisations are assessed, how strict certain controls are marked, and how carefully businesses need to define their certification scope.
The NCSC Cyber Essentials resources page says the scheme is reviewed and updated regularly. IASME has also explained that the 2026 update includes stricter assessment handling in key areas. That means companies that rely on old summaries or old screenshots could make avoidable mistakes.
This is also why Cyber Essentials 2026 Changes Explained fits well with your site’s compliance content. It belongs next to articles like Top Cybersecurity Threats to Watch in 2026 and Cybersecurity Incident Response Timeline, because certification, readiness, and business resilience all connect.
Cyber Essentials 2026 Changes Explained: 7 key updates
1. The 2026 update goes live on 27 April 2026
The NCSC resources page says the 2026 changes are currently available as a preview and will be adopted on 27 April 2026. That gives businesses a preparation window before the new version becomes active.
2. The five technical controls stay the same
The overall structure does not disappear in 2026. Cyber Essentials still relies on the same five technical controls, but the scheme is becoming stricter in how some areas are reviewed and assessed.
3. MFA is becoming a bigger pass-or-fail issue
IASME’s update on the April 2026 changes says stricter marking now applies to critical practices such as multi-factor authentication. Weak MFA coverage can increase the risk of failure during assessment.
4. Patch management is under closer review
The same IASME update highlights timely security updates across the full scope as another area where organisations can fail. Businesses should review laptops, desktops, cloud-connected devices, and all in-scope systems, not just a few core assets.
5. Scope definition remains critical
One of the most important parts of Cyber Essentials 2026 Changes Explained is scope. If the certification boundary is unclear, the whole assessment becomes harder. Businesses need to know exactly which users, devices, cloud services, and offices are inside the scope.
6. Evidence can still be requested
Many smaller organisations assume Cyber Essentials is only a questionnaire. In reality, the requirements documentation says evidence may be requested before certification is awarded. That means screenshots, settings, update records, and access-control details should be ready.
7. Preparation support is easier than before
The NCSC links to readiness resources, guidance, and support material that make preparation more structured than many businesses expect. That is especially useful for SMEs that want a clearer path to certification.

Cyber Essentials vs Cyber Essentials Plus
Cyber Essentials is the baseline certification. Cyber Essentials Plus adds independent technical verification. For many SMEs, standard Cyber Essentials is the right first step. For organisations working in sensitive supply chains or government-related environments, Cyber Essentials Plus may provide stronger assurance.
The PPN 014 Cyber Essentials guidance shows why this distinction matters in procurement. Businesses should not assume both levels are treated the same in every contract or supplier relationship.
How UK businesses should prepare
The best way to handle Cyber Essentials 2026 Changes Explained is to prepare early.
Start by defining scope clearly. Then review the five technical controls one by one. After that, focus on the areas that now carry more assessment risk, especially MFA and timely patching.
Businesses should also gather proof before submission. Prepare screenshots of MFA settings, endpoint protection, update status, access controls, and cloud configuration. This reduces delays and improves confidence before assessment.
At this point in the article, add internal links to How to Reduce Cybersecurity Detection Time, Incident Response Deadlines US UK, and Top Cybersecurity Threats to Watch in 2026 to keep readers inside your compliance and cyber-readiness cluster.

Common mistakes to avoid
A major mistake is using outdated guidance instead of the latest preview documents and current scheme resources. Another common problem is weak MFA coverage. A third is assuming that patching only matters for a few core systems instead of the full in-scope environment.
Another mistake is treating Cyber Essentials 2026 Changes Explained like a simple paperwork update. It is really a readiness issue. Businesses that delay scope reviews and evidence collection can create unnecessary certification risk.
Cyber Essentials 2026 Changes Explained FAQ
When do the 2026 Cyber Essentials changes start?
The NCSC says the 2026 updates are scheduled to be adopted on 27 April 2026.
Are the five technical controls changing?
No. The same five technical controls remain in place, but Cyber Essentials 2026 Changes Explained shows that marking and assessment handling are becoming stricter in key areas.
Can weak MFA cause failure?
Yes. IASME says stricter marking applies to important practices such as MFA, which increases the risk of failure if it is not implemented properly.
Does Cyber Essentials still matter for UK contracts?
Yes. GOV.UK says an up-to-date certificate can help businesses bid for certain government contracts involving financial or personal data.
Final thoughts
Cyber Essentials 2026 Changes Explained is a strong pillar topic for your website because it combines UK compliance, supplier trust, cyber readiness, and practical business action. It is not just a theoretical update. It directly affects how UK organisations prepare for certification and avoid preventable mistakes.
For your site, Cyber Essentials 2026 Changes Explained should stay linked to Compliance & Reporting, SEC vs UK Cyber Reporting Deadlines, and Cybersecurity Incident Response Timeline. That strengthens topical authority and helps search engines understand the relationship between your UK compliance content and your broader cybersecurity guidance.