Info Stealer Malware in 2026: 7 Dangerous Ransomware Risks
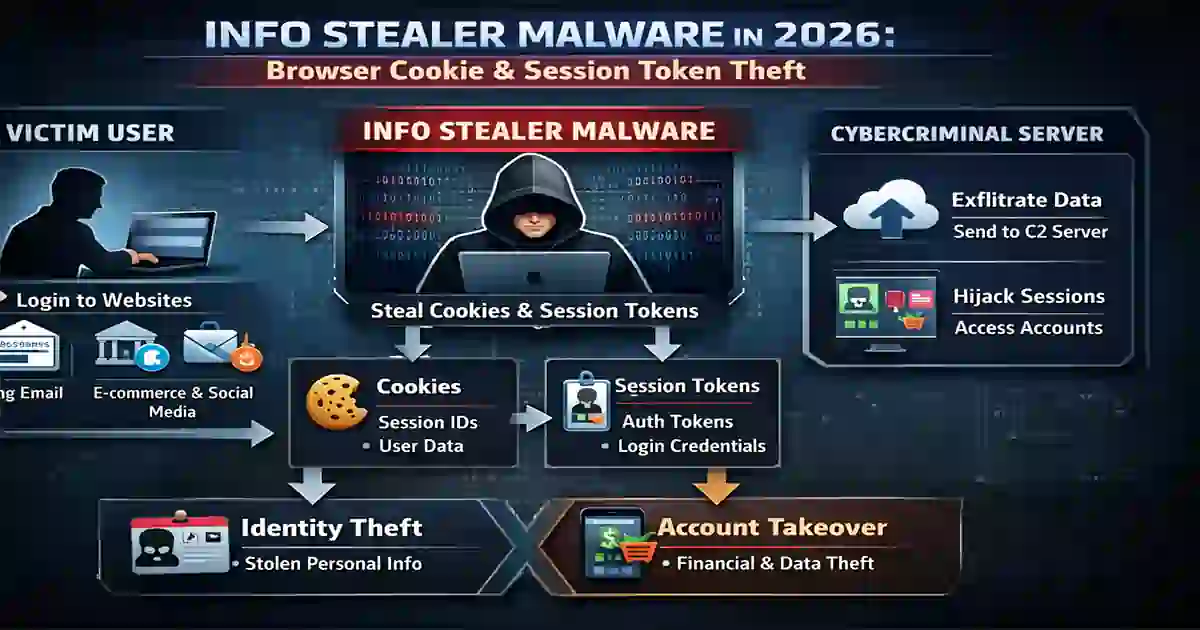
Info stealer malware in 2026 is no longer a minor credential-theft problem. It has become a practical entry point for account takeover, cloud compromise, data theft, extortion, and ransomware. What makes this threat especially serious is not just that attackers steal passwords. They also steal browser cookies, session tokens, saved credentials, wallet data, and system information that can help them reuse an already authenticated session.
That shift matters because many organizations still think of infostealers as low-end malware. In reality, they now sit much closer to the beginning of real business-impacting incidents. A single infected laptop can expose access to cloud services, finance tools, collaboration platforms, VPNs, and administrative systems. In many cases, the stealer operator does not even need to launch ransomware personally. The stolen access can be sold, reused, or passed along to another criminal group.
This is why info stealer malware in 2026 deserves attention from identity teams, cloud security teams, incident responders, and executives responsible for ransomware readiness.
Table of Contents
What Info Stealer Malware in 2026 Means
Info stealer malware in 2026 refers to malware designed to quietly extract useful data from an infected device. That usually includes usernames, passwords, browser cookies, session tokens, autofill data, email content, wallet information, and local files that reveal how the victim works.
The modern stealer is valuable because it collects more than secrets. It collects context. Attackers want to know which services the victim uses, which accounts are already active, what browser data is stored locally, and whether the machine belongs to an ordinary user or someone with access to sensitive systems.
That context can turn a simple malware infection into a much bigger problem. A victim with access to cloud administration, finance platforms, SaaS dashboards, backup systems, or shared enterprise accounts becomes a more attractive target. What used to look like commodity malware now functions as a feeder into a broader criminal access market.
This is one reason the topic fits naturally beside broader identity and ransomware coverage. Readers who want that bigger picture can continue with Top Cybersecurity Threats to Watch in 2026: 10 Critical Risks and 7 Critical Ransomware Initial Access 2026 Risks You Must Know.
Why Stolen Cookies and Tokens Matter
The biggest change in info stealer malware in 2026 is the growing importance of session theft.
A stolen password is dangerous, but it may still run into multi-factor authentication, conditional access rules, or suspicious login checks. A stolen session token can be even more useful because it may let the attacker act like a user who has already passed authentication. In practical terms, that can reduce the value of defenses focused only on the login moment.
That is why session security matters so much now. Browser cookies and tokens are not just technical artifacts. They are access artifacts. If attackers can extract them from an infected endpoint and replay them elsewhere, they may gain quiet access to email, cloud apps, collaboration systems, and business dashboards without triggering the same friction as a fresh login attempt.
This is also why phishing-resistant MFA remains important but not sufficient by itself. Strong authentication still blocks many common attacks, but defenders also need better control over the life and reuse of sessions. For a deeper look at that side of the problem, see Phishing-Resistant MFA Checklist: 12 Critical Steps.
Another overlooked issue is device sprawl. Contractors, personal devices used for work, synchronized browsers, and long-lived administrative sessions all increase risk. A compromise outside the office can still expose enterprise accounts inside the business.
How Info Stealer Malware in 2026 Leads to Ransomware
The path from infostealer to ransomware often begins quietly.
A user clicks a malicious ad, downloads cracked software, opens a fake update, follows a poisoned search result, or falls for a social-engineering lure. The infostealer lands on the device and begins collecting credentials, cookies, tokens, and system information. In some cases, the original operator monetizes the stolen data directly. In other cases, that data is sold or shared with another actor who wants enterprise access.
From there, the attack becomes more targeted. If the stolen logs show access to cloud consoles, finance tools, remote access services, admin portals, or shared SaaS accounts, the victim becomes more valuable. That can lead to privilege escalation, internal reconnaissance, data theft, extortion, or ransomware deployment.
This is why info stealer malware in 2026 should not be treated as an isolated malware event. It is often the first stage in a longer intrusion story. By the time encryption appears, the attacker may already have spent time exploring systems, finding valuable data, and identifying the best point of pressure.
This is also where containment speed becomes critical. If security teams are slow to revoke sessions, isolate endpoints, and investigate suspicious account activity, the attacker gets more time to turn stolen browser data into business impact. That makes Mean Time to Contain (MTTC): 10 Proven Ways to Minimize Impact and Average Time to Detect Cyber Attack in 2026: Latest Statistics useful companion reads.
7 Dangerous Ransomware Risks
1. Info Stealer Malware in 2026 Can Reuse Valid Sessions
The first risk is simple but powerful. Attackers may not need to log in the normal way if they can replay a valid session. That makes them harder to spot because they can appear to be the legitimate user rather than an obvious intruder failing repeated login attempts.
2. Info Stealer Malware in 2026 Turns Personal Devices Into Enterprise Exposure
The infected system is not always a corporate laptop. It may be a contractor device, a home PC, or a personal machine used for work. If that device stores business credentials or active sessions, the compromise can still lead directly to enterprise access.
3. Info Stealer Malware in 2026 Feeds the Access-Broker Economy
Stolen credentials and tokens are often monetized. Attackers do not always use the access themselves. They can sell it, trade it, or package it for buyers looking for organizations that fit a particular ransomware or extortion model. That lowers the barrier for later-stage attackers.
4. Info Stealer Malware in 2026 Shortens Time to Impact
A working session is more valuable than a vague lead. If an attacker already has valid access plus system context, the time between compromise and meaningful damage can shrink dramatically. That leaves defenders less room to investigate before the incident expands.
5. Info Stealer Malware in 2026 Is Cross-Platform
This is not only a Windows story anymore. Modern infostealer activity affects multiple environments, including browsers, macOS systems, Python-based tooling, cloud secrets, and developer workflows. Organizations that defend only one platform may miss important exposure elsewhere.
6. Info Stealer Malware in 2026 Scales Through Criminal Services
Infostealer malware is increasingly commercialized. Malware-as-a-service models let less sophisticated actors buy or rent tools that steal data at scale. That makes the ecosystem larger, faster, and more consistent than older one-off malware campaigns.
7. Info Stealer Malware in 2026 Blends Data Theft, Extortion, and Ransomware
The line between credential theft, data theft, and ransomware is now much thinner. Stolen access may first be used to quietly collect data, then to pressure the victim with extortion, and finally to deploy ransomware if the operator decides encryption adds leverage.
What Defenders Should Do Now
The first step is to stop dismissing infostealer alerts as routine malware noise.
If a device shows signs of stealer activity, responders should assume that credentials, cookies, and session tokens may have been exposed. Password resets matter, but they are not enough on their own. Teams may also need to revoke active sessions, review browser synchronization, investigate cloud logs, and check whether privileged accounts were accessed from unusual devices or locations.
The second step is identity hardening. Sensitive accounts should use phishing-resistant MFA, stronger session controls, better device trust, and tighter reauthentication rules for risky actions. This is particularly important for administrators, finance users, SaaS owners, and anyone with access to core infrastructure.
The third step is disciplined incident response. A good response is not just technical cleanup. It also requires a timeline, clear ownership, evidence collection, containment decisions, and follow-up monitoring. That is where these internal resources fit naturally:
- Cybersecurity Incident Response Timeline: 6 Proven Steps
- Data Breach Timeline Template: 9 Critical Response Steps
- Third-Party Risk Assessment Checklist 2026: 12 Proven Steps
Third-party exposure deserves special attention. Vendors, contractors, consultants, and service providers often extend the attack surface in ways that are easy to underestimate. If they store sessions, reuse browsers, or access shared systems from less controlled environments, they can widen identity risk significantly.
The fourth step is visibility. Security teams need enough telemetry to detect abnormal session use, impossible travel, suspicious device changes, unusual privilege activation, and signs that a stolen session is being reused in a different context. Without that visibility, a quiet session hijack may go unnoticed until data theft or ransomware is already underway.
Conclusion
Info stealer malware in 2026 matters because it turns small compromises into reusable access.
Instead of simply stealing passwords, attackers now target the information that keeps users logged in and systems connected. That makes the threat more efficient, more scalable, and more useful to criminal groups that want quiet entry into business environments. In many cases, the malware itself is only the first step. The real damage appears later, when stolen access is used for cloud compromise, data theft, extortion, or ransomware.
Organizations that still classify infostealers as minor commodity malware are underestimating the risk. In 2026, the better view is this: info stealer malware in 2026 is an identity and access threat with direct implications for ransomware defense, cloud security, incident response, and business resilience.