Third-Party Risk Assessment Checklist 2026: 12 Proven Steps
Third-party risk assessment checklist planning should be part of every serious security program in 2026. If your business relies on SaaS apps, cloud platforms, payment processors, MSPs, outsourced developers, or data processors, a strong third-party risk assessment checklist helps reduce breach exposure before a weak supplier becomes your incident.
Table of Contents
Why a third-party risk assessment checklist matters in 2026
A modern third-party risk assessment checklist is more than a vendor questionnaire.
It helps security teams identify which suppliers can access sensitive data, disrupt operations, weaken resilience, or create compliance pressure. The NIST CSF 2.0 quick-start guide for C-SCRM recommends identifying technology suppliers, determining criticality, and defining supplier requirements, while NIST SP 800-161 Rev. 1 connects cyber supply chain risk directly to enterprise risk management.
That pressure is not limited to one region. The EU’s NIS2 framework applies a common cybersecurity baseline across 18 critical sectors, the UK ICO contracts guidance requires written contracts when controllers use processors and when processors use subprocessors, and DORA oversight applies in the EU financial sector with explicit focus on ICT third-party risk.

Third-Party Risk Assessment Checklist: 12 Essential Steps
1. Build a complete vendor inventory
Start with a full list of vendors, tools, and service providers that can touch your data, systems, source code, backups, payments, identities, or customer communications.
Include cloud providers, payroll systems, support partners, plugins, analytics tools, AI tools, contractors, legal firms, and outsourced developers. If a supplier can affect confidentiality, integrity, availability, or reporting obligations, it belongs in your review scope.
2. Tier suppliers by criticality
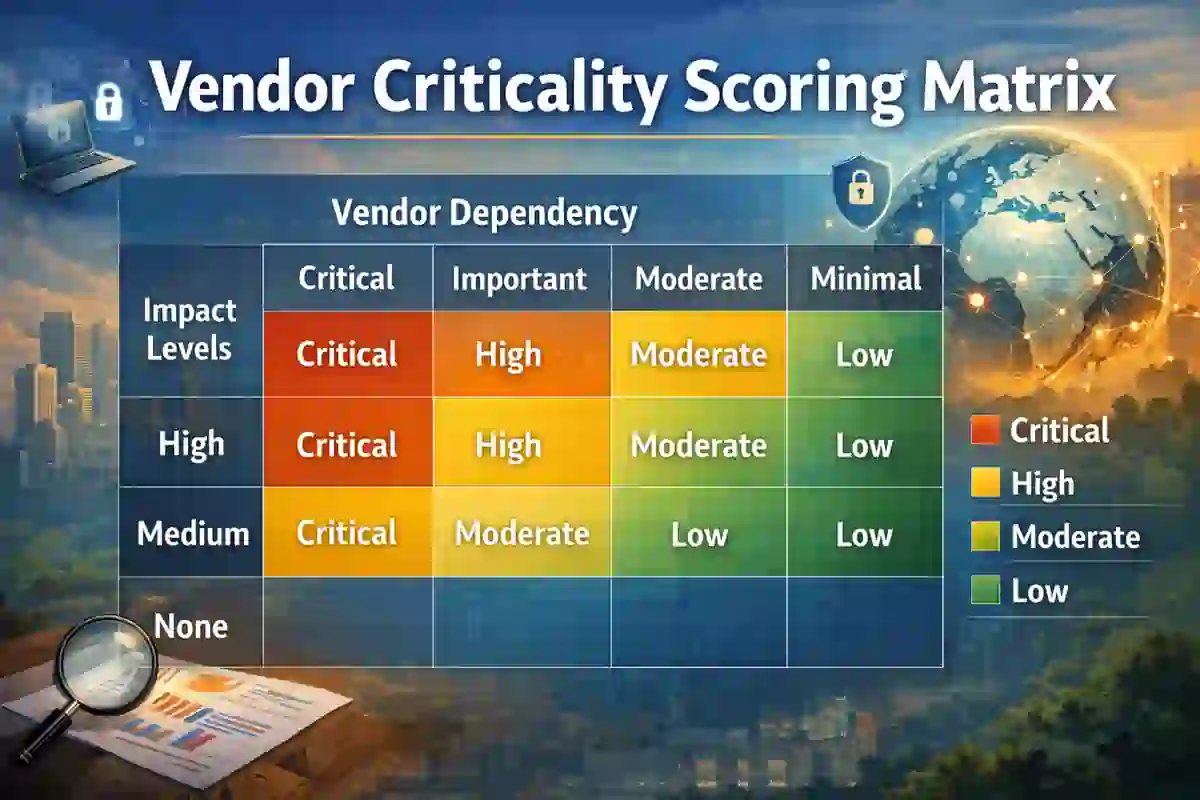
Not every vendor creates the same risk.
Classify suppliers as critical, high, medium, or low risk based on privileged access, production dependency, data sensitivity, concentration risk, customer impact, and how hard the vendor would be to replace. This keeps your process practical instead of treating every supplier the same way.
3. Map each supplier to legal and contractual obligations
Your third-party risk assessment checklist should ask which laws, frameworks, customer commitments, and internal policies apply before controls are reviewed.
A US public company may need supplier-related incidents escalated into SEC cybersecurity disclosure workflows. A UK business handling personal data should confirm processor and subprocessor contract terms. An EU operator in a covered sector should consider NIS2 obligations, and a financial entity should also assess DORA-specific ICT third-party requirements.
4. Ask for evidence, not marketing language
A mature review process looks for proof.
Ask for security policies, penetration test summaries, patching standards, backup procedures, logging details, access-control documentation, vulnerability management processes, and independent assurance where available. A sales deck is not evidence.
5. Review identity and privileged access
This checklist should examine MFA, SSO, least privilege, role separation, access reviews, service account management, and fast offboarding.
If a supplier can access production systems, admin panels, customer records, or source code, weak identity controls become your risk too. This is where security teams often discover hidden admin paths that were never approved formally.
6. Verify monitoring and incident notification
A practical third-party risk assessment checklist must confirm how quickly a vendor can detect, investigate, and report suspicious activity.
Ask how long logs are retained, who reviews alerts, how evidence is preserved, and how fast customers are notified after a confirmed incident. This is a good place to add internal links to Mean Time to Detect and the Board-Level Cybersecurity Metrics Guide because vendor visibility affects both operational detection speed and executive reporting.
7. Test resilience, backup, and recovery capability
Ask what happens if the supplier is unavailable for six hours, one day, or three days.
Review backup frequency, restore testing, recovery objectives, geographic redundancy, single-region dependency, and crisis communication plans. For stronger internal topic clustering, add links to Average Ransomware Containment Time 2026 and CIRCIA 72-Hour Reporting Rule.
8. Check software supply chain practices
If the vendor provides software, integrations, agents, APIs, or firmware, your third-party risk assessment checklist should go deeper.
Ask about secure development practices, dependency management, code signing, vulnerability disclosure, patch turnaround, and whether an SBOM can be shared where appropriate. CISA describes SBOM as a transparency resource that helps organizations understand software components and dependencies.
9. Strengthen the contract
Treat the contract as a security control, not paperwork.
The agreement should define security obligations, breach notification support, audit rights, confidentiality, data return or deletion, subprocessor approval, and end-of-contract handling. The UK ICO makes clear that controllers need written contracts with processors, and processors also need written terms with subprocessors.
10. Look beyond the direct vendor
A complete vendor review should examine fourth-party dependencies as well.
Ask which hosting providers, identity platforms, support tools, subcontractors, and storage services the supplier relies on. Hidden dependencies can become a major source of concentration risk, outage exposure, or delayed incident response.

11. Score the risk and record the decision
Use weighted scoring for access, data sensitivity, resilience, legal impact, subcontractor exposure, and incident readiness.
Then make a clear decision: accept the risk, require remediation, restrict access, increase monitoring, or replace the vendor. This keeps your process defensible and measurable.
12. Reassess continuously
The best third-party risk assessment checklist is not a one-time onboarding document.
Review critical vendors quarterly, reassess high-risk suppliers at least annually, and trigger an immediate review after incidents, ownership changes, major architecture changes, or newly introduced subcontractors. The UK NCSC supply chain guidance is built around maintaining control and oversight over time.
Regional checks for the US, UK, and Europe
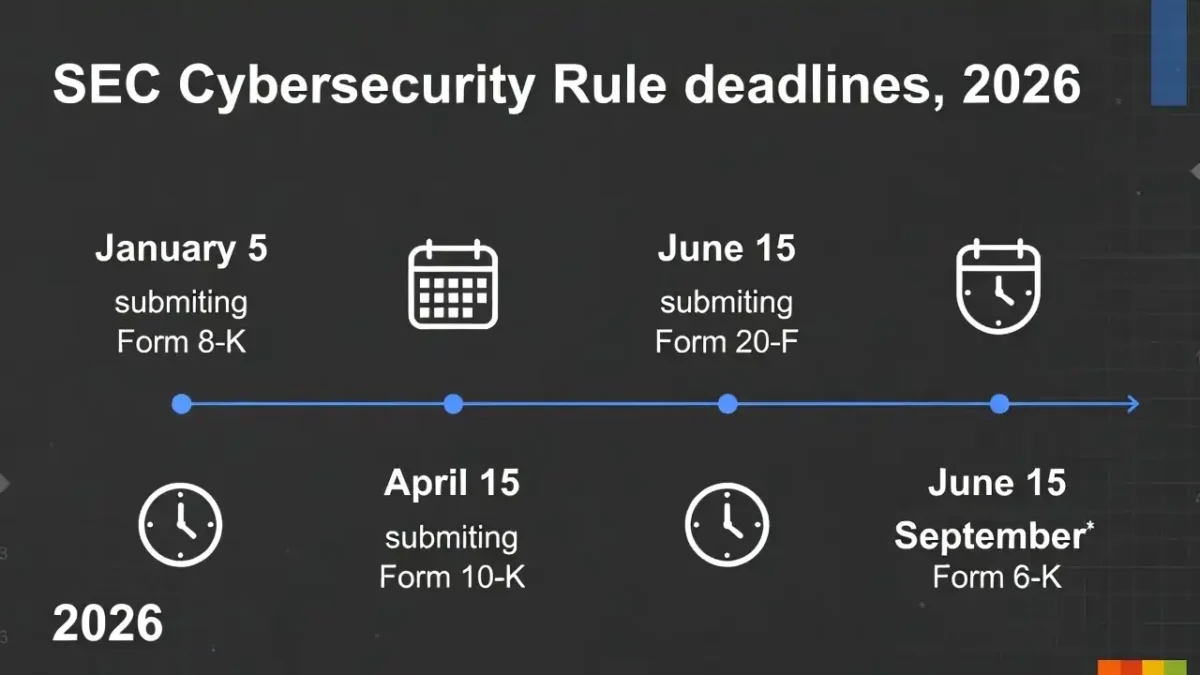
For the United States, your third-party risk assessment checklist should confirm whether supplier incidents can be escalated quickly enough for legal review, executive review, and disclosure decisions where applicable. The SEC’s rules require disclosures about cybersecurity risk management, strategy, and governance for covered public companies.
For the United Kingdom, it should verify processor contracts, subprocessor approval, audit rights, breach cooperation, and data return or deletion obligations. Those are core points in ICO guidance for controller-processor arrangements.
For Europe, it should determine whether NIS2 applies and, if you are in financial services, whether DORA adds specific ICT third-party oversight expectations. NIS2 covers 18 critical sectors, and DORA has applied since 17 January 2025 in the EU financial sector.
Add one more internal link here to your Information Security Guide because vendor oversight is one part of a broader information security strategy.
Final Thoughts
A well-written third-party risk assessment checklist for 2026 helps organizations move from reactive vendor review to measurable risk reduction.
When you inventory suppliers, tier them by impact, review contracts, check software supply chain practices, and monitor fourth-party exposure, you reduce both cyber risk and compliance pressure.