Public vulnerability triage tool
CISA KEV Patch Priority Calculator
Estimate patch urgency using KEV evidence, exploit activity, internet exposure, business impact, data sensitivity, and compensating controls.
This is a decision-support calculator, not an official CISA score. Use it with your own asset inventory, change-management process, and legal or regulatory obligations.
CISA KEV Patch Priority Calculator
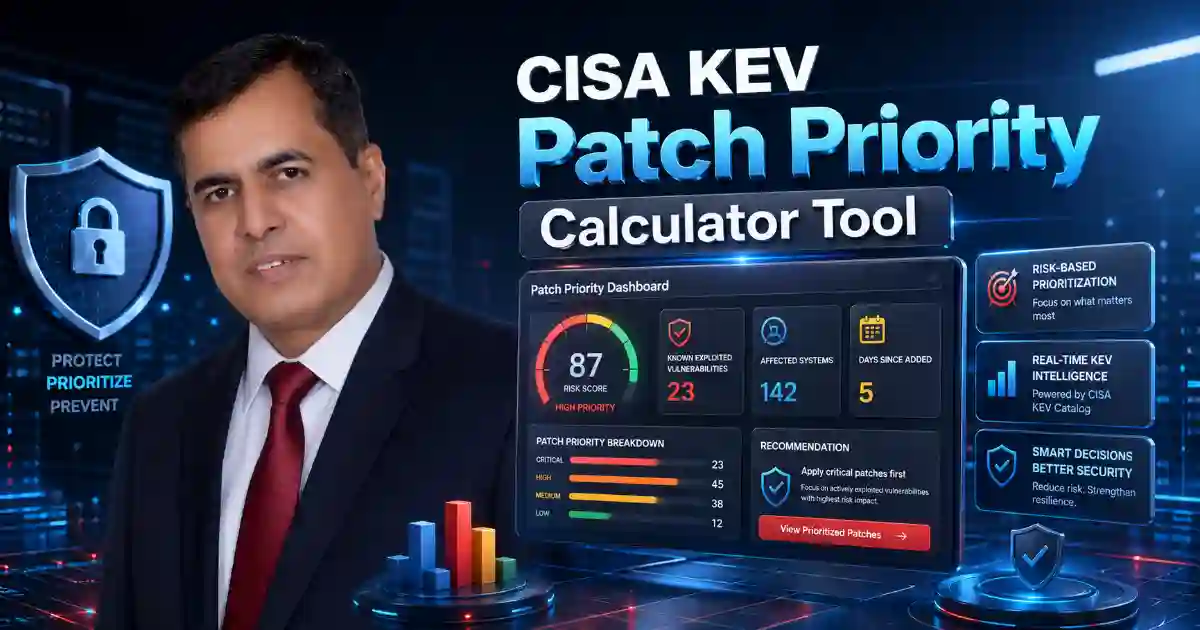
CISA KEV Patch Priority Calculator helps you decide which known exploited vulnerability should be fixed first. Many security reports show long CVE lists, technical scores, and urgent alerts. This tool makes the decision easier by turning important risk signals into a simple patch priority score.
Use this calculator to check KEV status, internet exposure, exploit activity, business impact, sensitive data risk, and compensating controls. The result helps you understand whether a vulnerability needs urgent action, fast patching, planned remediation, or normal monitoring.
This tool is useful for website owners, small businesses, IT teams, MSPs, cybersecurity freelancers, schools, nonprofits, healthcare teams, finance teams, and public-sector organizations.
What Is the CISA KEV Patch Priority Calculator?
The CISA KEV Patch Priority Calculator is a practical cybersecurity tool that helps users prioritize vulnerabilities listed in or related to CISA’s Known Exploited Vulnerabilities catalog.
A vulnerability becomes more serious when attackers are already exploiting it, especially if the affected system is public-facing or important to business operations. This tool helps you move beyond guesswork and focus on the risks that need attention first.
It is not an official CISA scoring system. It is a decision-support tool designed to help readers understand patch urgency in a simple way.
Why Patch Priority Matters
Not every vulnerability has the same risk. A low-exposure issue on a test system may not need the same urgent response as an exploited flaw on a public server, firewall, VPN, email system, admin panel, or customer database.
The CISA KEV Patch Priority Calculator helps users answer one important question:
Which vulnerability should we fix first?
This is especially helpful for users in the USA, UK, Canada, Australia, Germany, France, Netherlands, Ireland, Switzerland, Sweden, Denmark, and wider Europe, where vulnerability management and cyber risk planning are important for business security and compliance readiness.

How the Calculator Works
The calculator checks simple but important questions:
- Is the vulnerability listed in CISA KEV?
- Is the affected system internet-facing?
- Is exploit activity known or likely?
- Is the asset business-critical?
- Does the system store sensitive data?
- Are strong security controls already active?
- Is the patch easy, difficult, or risky to apply?
After reviewing these answers, the CISA KEV Patch Priority Calculator gives a score from 0 to 100.
Why Patch Priority Matters
Not every vulnerability has the same risk. A low-exposure issue on a test system may not need the same urgent response as an exploited flaw on a public server, firewall, VPN, email system, admin panel, or customer database.
The CISA KEV Patch Priority Calculator helps users answer one important question:
Which vulnerability should we fix first?
This is especially helpful for users in the USA, UK, Canada, Australia, Germany, France, Netherlands, Ireland, Switzerland, Sweden, Denmark, and wider Europe, where vulnerability management and cyber risk planning are important for business security and compliance readiness.
What the Score Means
Critical Priority
Fix immediately if possible. If patching is delayed, reduce exposure, restrict access, and monitor closely.
High Priority
Patch as soon as possible. Do not leave the issue open without a clear remediation plan.
Medium Priority
Schedule the patch soon. Confirm that existing controls are working.
Low Priority
Track the issue and fix it during the normal update cycle.
What to Do Next
After using the CISA KEV Patch Priority Calculator, review the result and take practical action.
First, confirm the affected asset. Then check vendor guidance, apply the patch if available, document the fix, and monitor the system after remediation.
If you cannot patch immediately, use temporary controls such as MFA, firewall rules, IP restrictions, network segmentation, endpoint protection, backups, and stronger logging.
Good patch management is not only about fixing systems. It is about knowing what matters most, acting quickly, and keeping clear evidence of what was done.
Helpful Cybersecurity Resources
For more guidance, review these trusted sources:
- CISA Known Exploited Vulnerabilities Catalog
- UK NCSC Vulnerability Management Guidance
- FIRST EPSS Exploit Prediction Scoring System
You can also explore related tools on Cybersecurity Time:
FAQ
Is this an official CISA tool?
No. This is an educational calculator that uses KEV status and other risk signals to support better patch decisions.
Who should use this tool?
Small businesses, website owners, IT teams, MSPs, schools, nonprofits, public-sector teams, and cybersecurity professionals can use it.
Should I patch only KEV vulnerabilities?
No. KEV vulnerabilities need serious attention, but you should also review CVSS, EPSS, vendor guidance, asset exposure, and business impact.
What if I cannot patch immediately?
Reduce exposure, restrict access, improve monitoring, apply temporary controls, and document why patching is delayed.
