Mean Time to Respond: 5 Proven Ways to Reduce Risk
Mean Time to Respond (MTTR) is a critical cybersecurity metric that measures how quickly a security team reacts after detecting a threat.
While detection identifies an attack, response speed determines how much damage is prevented. Slow incident response allows threats to escalate, while faster action limits impact and accelerates recovery.
This guide explains MTTR in cybersecurity, how it is calculated, and practical ways organizations can reduce response delays during cyber attacks.
Table of Contents
What Is Mean Time to Respond?
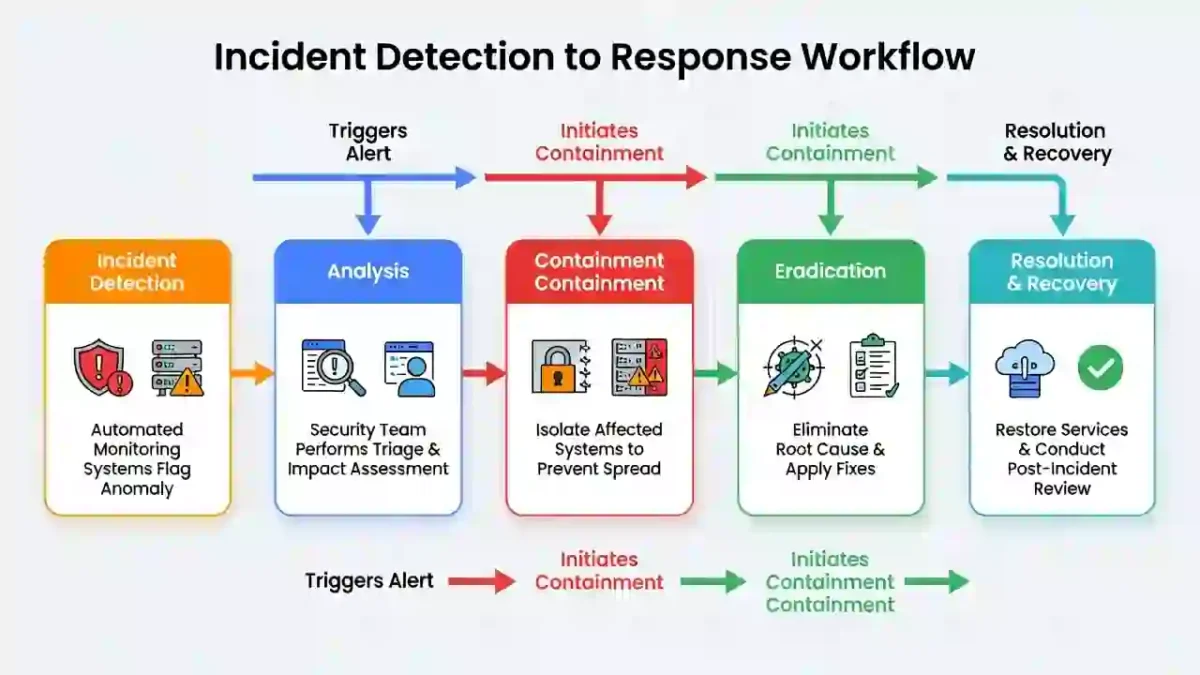
Mean Time to Respond refers to the average time required to contain and remediate a security incident after detection.
In simple terms, it measures how quickly a security team acts once an attack is discovered.
Response speed directly affects downtime, financial loss, and operational disruption across the organization.
Why Response Time Matters in Cybersecurity
When a cyberattack is detected, every minute counts.
Slow response can lead to:
- Ransomware spreading across systems
- Increased data exfiltration
- Prolonged system compromise
- Higher recovery and remediation costs
Reducing response delays is essential for improving overall Cybersecurity Time performance.
How Response Time Is Calculated
The standard formula for calculating response time is:
MTTR = Total Response Time ÷ Number of Incidents
Example
If three incidents require a combined 30 hours to contain:
- Average response time = 10 hours
Tracking this metric regularly helps security teams identify workflow gaps and improvement opportunities.
Average Incident Response Time
Average response duration varies widely depending on monitoring maturity and automation.
Industry observations show:
- Some organizations require days to contain attacks
- Mature SOC teams respond within hours
- Automated containment significantly shortens response cycles
For authoritative research, refer to:
5 Proven Ways to Reduce Response Time
1. Automate Incident Containment
Automated playbooks isolate compromised systems immediately.
Automation removes manual delays and speeds containment during active attacks.
2. Define Clear Escalation Procedures
Clear roles and communication paths eliminate confusion.
Defined ownership ensures faster decision-making under pressure.
3. Conduct Incident Response Drills
Regular simulations improve coordination and reduce delays during real incidents.
Practice builds muscle memory for faster action.
4. Use Centralized Case Management
Unified case tracking tools streamline investigations and reduce handoff delays.
This improves visibility across security teams.
5. Integrate Detection With Response Tools
Connecting SIEM and EDR tools enables rapid containment actions.
Strong integration reduces gaps between alerting and remediation.
How Response Time Compares to Other Security Metrics
Response speed works alongside other key metrics:
Together, these metrics provide a full picture of incident handling efficiency.
Frequently Asked Questions
What is a good Mean Time to Respond?
Leading organizations aim to contain threats within hours rather than days.
How can organizations reduce response time during a cyberattack?
By automating workflows, defining escalation paths, and integrating security tools.
Is response time the same as detection time?
No. Detection identifies the threat, while response focuses on containment and remediation.
Final Thoughts
Mean Time to Respond is a core indicator of cybersecurity effectiveness.
Organizations that automate processes, train teams, and continuously refine response workflows significantly reduce operational risk and long-term impact from cyber incidents.
Improving response efficiency strengthens overall security posture and resilience.


