Dwell Time: 5 Proven Ways to Reduce Cyber Attack Risk
Dwell Time refers to the total period an attacker remains undetected inside an organization’s environment.
When intruders are not discovered quickly, they gain time to explore systems, escalate privileges, and access sensitive data. Reducing this hidden attacker presence is one of the most effective ways to limit damage and lower overall cyber risk.
This guide explains what dwell time means in cybersecurity, why it matters, how it is measured, and how organizations can significantly reduce attacker exposure.
Table of Contents
What Is Dwell Time?
Dwell Time is the length of time a cyber attacker remains inside a system before being detected and removed.
In simple terms:
It measures how long malicious activity goes unnoticed.
Shorter attacker presence means faster detection, quicker response, and less opportunity for damage.
Why Attacker Presence Duration Matters
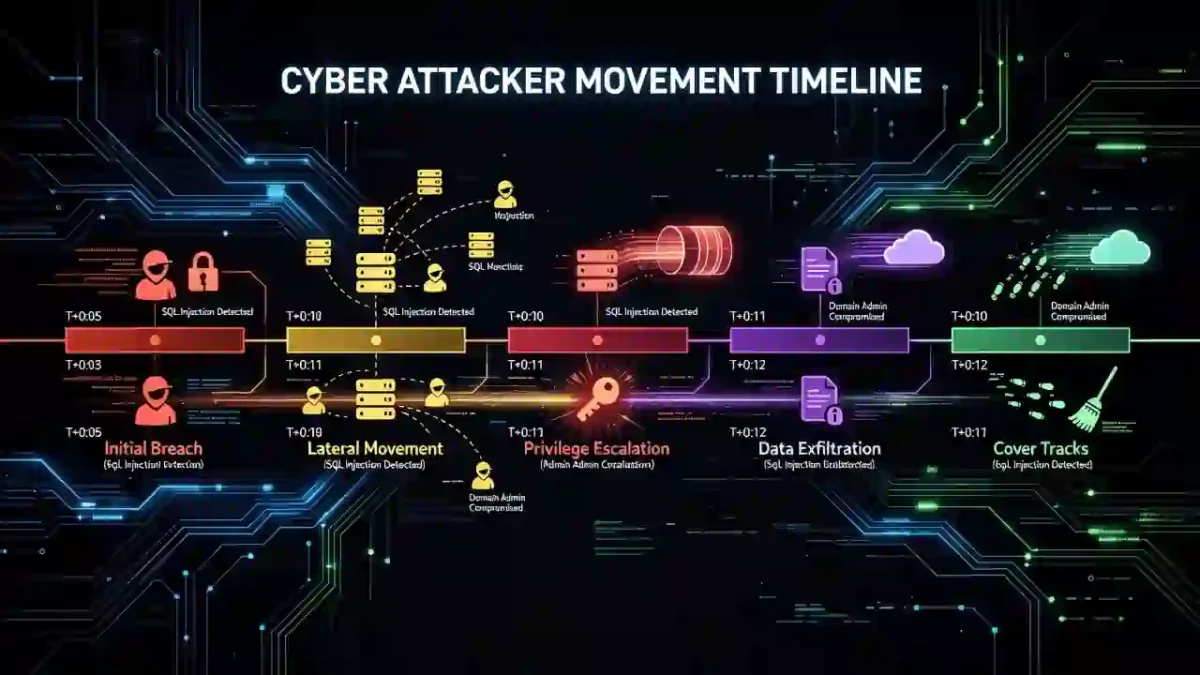
Attackers rarely act immediately. While they remain hidden, they often:
- Move laterally across networks
- Escalate user privileges
- Identify high-value assets
- Exfiltrate data
- Prepare ransomware or destructive actions
The longer an intruder operates undetected, the greater the risk of data theft, service disruption, and regulatory exposure.
Reducing attacker presence duration improves overall Cybersecurity Time performance and strengthens organizational resilience.
How Attacker Presence Is Measured
Attacker presence is calculated using two timestamps:
- The moment of initial compromise
- The moment the threat is detected
Presence Duration = Detection Time − Compromise Time
Shorter durations indicate stronger monitoring and faster visibility into malicious activity.
Average Attacker Presence in Cyber Attacks
The average attacker presence varies depending on security maturity.
General trends show:
- Some organizations discover breaches after weeks or months
- Mature security teams reduce undetected activity to days or hours
- Automated monitoring dramatically shortens exposure windows
For authoritative industry data, review Data Breach and News Events
5 Proven Ways to Reduce Attacker Presence
1. Improve Threat Detection Capabilities
Advanced detection tools help identify malicious activity earlier, reducing the amount of time attackers remain hidden.
2. Use Continuous Monitoring
Always-on monitoring identifies suspicious behavior faster than periodic reviews and manual checks.
3. Apply Behavioral Analytics
Behavior-based detection identifies abnormal activity even when no known malware signature exists.
4. Automate Incident Response
Automated containment actions remove attackers faster once suspicious activity is confirmed.
5. Conduct Regular Threat Hunting
Proactive threat hunting uncovers hidden intrusions that automated tools may miss.
Relationship to Other Cybersecurity Metrics
Attacker presence duration works closely with other time-based security metrics, including:
- Detection speed (MTTD)
- Response speed (MTTR)
- Containment time (MTTC)
Together, these measurements define how quickly an organization can detect, respond to, and eliminate threats.
Frequently Asked Questions
What is dwell time in cybersecurity?
It is the amount of time an attacker remains inside a system before detection.
Why is long attacker presence dangerous?
Extended undetected access allows attackers to steal data, spread malware, and increase damage.
What is a good benchmark?
High-performing organizations aim to reduce attacker presence to hours or a few days.
Final Thoughts
Dwell Time is a critical cybersecurity indicator because it directly affects breach impact.
Organizations that improve monitoring, automate response, and invest in early detection significantly reduce attacker exposure and long-term risk.
Shorter attacker presence leads to faster recovery, lower costs, and stronger overall security.


