Cybersecurity Incident Response Timeline: 6 Proven Steps

The Cybersecurity Incident Response Timeline defines how quickly an organization detects, contains, and recovers from a cyberattack.
In modern security operations, response speed determines overall impact.
Organizations with a structured incident response process limit data loss, reduce downtime, and lower breach costs. Slow reaction times allow attackers to escalate access and expand damage.
This guide explains the complete response lifecycle and how to improve each phase.
Table of Contents
What is a Cybersecurity Incident Response Timeline?
An incident response timeline is the sequence of actions taken from the moment a breach begins until systems are fully restored.
It includes:
- Detection
- Containment
- Eradication
- Recovery
- Post-incident review
The shorter this timeline, the less opportunity attackers have to cause harm.
For a broader breakdown of time-based metrics, see our guide on Cybersecurity Time
Why Response Time Matters
Cyberattacks progress quickly.
- Ransomware spreads in minutes
- Credentials may be abused silently
- Data theft often begins immediately
Delays increase dwell time and financial impact.
According to the IBM Cost of a Data Breach Report, Organizations that detect and contain threats faster experience significantly lower breach costs.
Speed is measurable. And it is controllable.
The 6 Steps in the Response Lifecycle

Most organizations follow the NIST SP 800-61 framework
1. Preparation
Preparation defines roles, responsibilities, and communication channels before an attack occurs.
This includes:
- A documented response plan
- Monitoring tools (SIEM, EDR)
- Backup strategies
- Escalation procedures
Strong preparation shortens every stage of the response process.
2. Detection
Detection begins when suspicious activity is identified.
This phase affects Mean Time to Detect (MTTD). Faster detection reduces lateral movement and data exposure.
3. Containment
Containment stops the spread of the attack.
Security teams may:
- Isolate compromised systems
- Disable affected accounts
- Block malicious traffic
Quick containment limits business disruption.
4. Eradication
Eradication removes the attacker’s presence.
Teams typically:
- Remove malicious files
- Patch vulnerabilities
- Reset credentials
Incomplete cleanup increases reinfection risk.
5. Recovery
Recovery restores operations safely.
This phase impacts Mean Time to Respond (MTTR). Systems should be monitored carefully during restoration.
6. Lessons Learned
Post-incident review strengthens future resilience.
Organizations evaluate:
- Detection delays
- Communication gaps
- Automation weaknesses
Continuous improvement shortens future timelines.
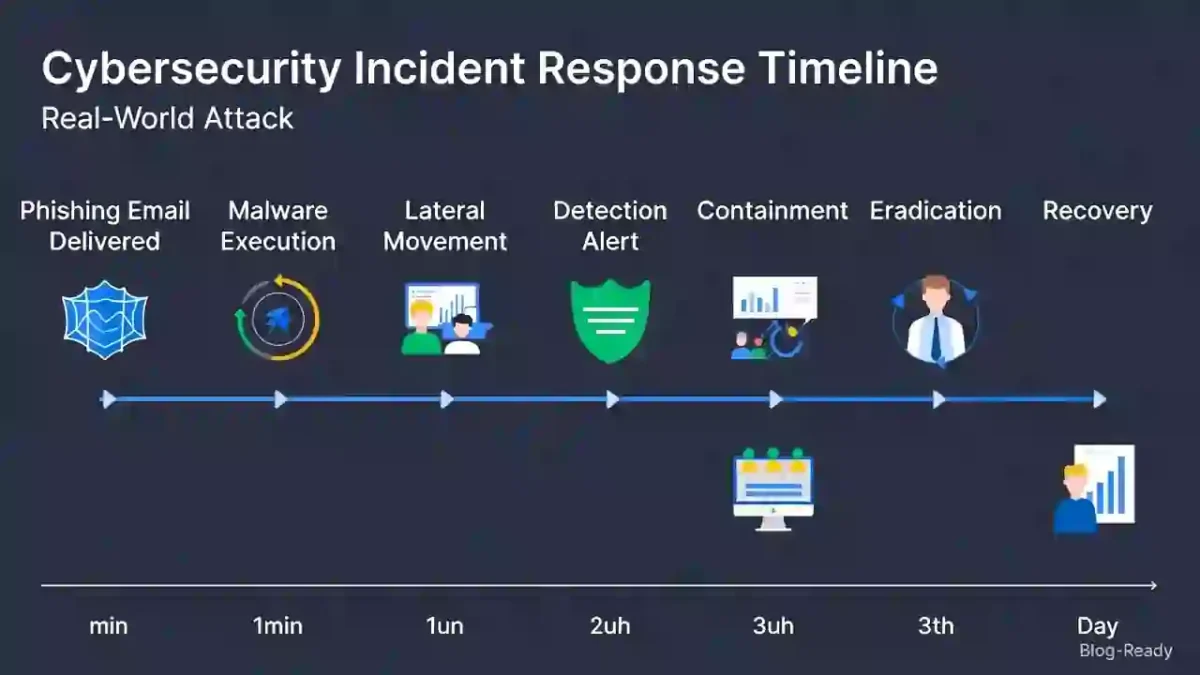
| Time | Event |
|---|---|
| 0 min | Phishing email delivered |
| 30 min | Malware executed |
| 2 hrs | Lateral movement |
| 4 hrs | Alert triggered |
| 5 hrs | Systems isolated |
| 48 hrs | Threat removed |
| 72 hrs | Systems restored |
Detection within hours instead of days significantly reduces impact.
See updated statistics here: Average Time to Detect a Cyber Attack
Key Metrics That Influence Response Speed
Important indicators include:
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Mean Time to Contain (MTTC)
- Dwell Time
Reducing these metrics improves operational resilience.
How to Shorten Your Response Timeline
Organizations can improve speed by:
- Implementing 24/7 monitoring
- Automating response workflows
- Segmenting networks
- Conducting regular simulations
For detailed guidance: Reduce Cybersecurity Detection Time
Final Thoughts
The Cybersecurity Incident Response Timeline is a measurable indicator of security maturity.
Organizations that detect early, contain quickly, and recover efficiently reduce financial and operational damage.
In today’s threat environment, response speed is a strategic advantage.


