AI Vulnerability Exploitation Patch Windows: Critical Trend
If you are tracking AI vulnerability exploitation patch windows, the main trend is clear: defenders are getting less time between disclosure, exploit adaptation, and real-world attacks. Google’s Threat Intelligence Group says it expects AI to accelerate reconnaissance, vulnerability discovery, and exploit development in 2026, and its 2025 review says it tracked 90 zero-day vulnerabilities exploited in the wild, with 43 affecting enterprise products. That is why AI vulnerability exploitation patch windows are now becoming a serious concern for global security teams. (cloud.google.com)
The phrase AI vulnerability exploitation patch windows does not mean AI is replacing attackers. It means AI is shrinking the time attackers need for tasks that once slowed them down, such as code review, target mapping, exploit adaptation, and vulnerability triage. Google’s 2026 forecast points directly to that acceleration, while the UK NCSC continues to treat AI-related cyber risk as a major live issue in its threat reporting. (cloud.google.com; ncsc.gov.uk)
For defenders, AI vulnerability exploitation patch windows matter because patching programs were already under pressure before AI started accelerating offensive workflows. Google says there is a shrinking gap between public disclosure of n-day vulnerabilities and widespread exploitation by multiple groups, especially in enterprise software and edge technologies. That makes old monthly patch assumptions less reliable than they used to be. (cloud.google.com)
This trend also changes how teams should think about prioritization. CISA says organizations should use the Known Exploited Vulnerabilities Catalog as an input to vulnerability prioritization, which fits directly with the idea that AI vulnerability exploitation patch windows are shrinking and patch decisions must become more threat-informed. For internal context, this article fits naturally with your KEV vs CVSS Patch Priority, Cybersecurity Metrics, and Board-Level Cybersecurity Metrics Guide. (cisa.gov)
Table of Contents
What Does It Mean When Patch Windows Shrink?
A shrinking patch window means defenders have less time to identify, assess, test, approve, and deploy a fix before attackers begin exploiting a vulnerability at scale. In practical terms, AI vulnerability exploitation patch windows describe a world where the time between disclosure and meaningful attacker activity gets shorter. Google’s latest review says the disclosure-to-exploitation gap is narrowing, especially for enterprise software. (cloud.google.com)
This is not just a zero-day problem. Google also says the gap is shrinking for n-day vulnerabilities, which means even vulnerabilities with patches available can become urgent very quickly once technical details spread. For internal context, this section also fits with How to Reduce Cybersecurity Detection Time and How to Reduce Cyber Breach Detection Time. (cloud.google.com)
Why AI Changes Vulnerability Exploitation Speed
Google says AI is likely to accelerate reconnaissance, vulnerability discovery, and exploit development in 2026. Those are exactly the attacker phases that used to give defenders time. When those phases speed up, AI vulnerability exploitation patch windows become smaller. (cloud.google.com)
The biggest near-term risk is not fully autonomous exploitation. It is that AI lowers the effort needed to summarize advisories, interpret affected systems, adapt proof-of-concept logic, and identify exposed targets. Even when a human is still directing the attack, AI can remove enough friction to make old patch timelines feel dangerously slow. That is an inference grounded in Google’s current threat forecast. (cloud.google.com)
For internal readers, this section also pairs naturally with AI Reducing Breach Detection Time 2026, Cybersecurity Best Practices, and Cybersecurity Time. (cybersecuritytime.com)
Where the Trend is Showing Up First
Google’s 2025 zero-day review says attackers increasingly focused on enterprise software, security appliances, networking devices, edge infrastructure, and operating systems, with 43 of the 90 tracked zero-days affecting enterprise products. That means AI vulnerability exploitation patch windows are especially relevant for organizations that rely on internet-facing business systems, identity platforms, VPNs, gateways, and virtualized infrastructure. (cloud.google.com)
Google also highlights edge devices as attractive targets because they often sit at the perimeter and may not have the same visibility controls defenders rely on elsewhere. In environments like that, even a short patch delay can increase risk sharply. For internal follow-on reading, this also fits with Industry Benchmarks 2026: Critical Response Insights and Mean Time to Detect: 5 Proven Ways to Reduce Risk. (cloud.google.com)

7 Reasons Patch Windows Are Shrinking
1. AI speeds up exploit support work
Google says AI is likely to accelerate exploit development in 2026. Even partial acceleration shortens how much time defenders have. (cloud.google.com)
2. Reconnaissance is easier to automate
Google also says AI will accelerate reconnaissance, which means faster identification of exposed systems after disclosure. (cloud.google.com)
3. Vulnerability discovery is speeding up
If AI helps find more vulnerabilities faster, vendors and defenders both face more pressure at once. (cloud.google.com)
4. Enterprise and edge systems are under heavy pressure
Google’s data shows that enterprise products and edge technologies are a major target class, which makes rapid patching more important. (cloud.google.com)
5. The disclosure-to-exploitation gap is shrinking
Google explicitly says the gap between disclosure of n-days and widespread exploitation is narrowing. That is one of the clearest signals behind AI vulnerability exploitation patch windows. (cloud.google.com)
6. Exploitation evidence matters more than raw severity
CISA’s KEV guidance shows that known exploitation should drive urgency more strongly than theoretical severity alone. For internal continuity, this also supports KEV vs CVSS Patch Priority. (cisa.gov)
7. Attackers only need one exposed weakness
Google says increasing software and device complexity expands the attack surface, and attackers only need a single exposed point of failure. For internal context, this also pairs with Dwell Time vs MTTD. (cloud.google.com)
What Security Teams Should Change Now
The first change is strategic: stop assuming a monthly patch cycle is enough for every class of vulnerability. Routine cadence still matters, but AI vulnerability exploitation patch windows mean exposed, exploited, identity-related, and edge-related issues need a faster lane. CISA’s KEV guidance strongly supports this threat-informed model. For internal context, this section also fits with Compliance & Reporting. (cisa.gov)
The second change is procedural: triage needs to begin closer to disclosure. If AI is compressing attacker workflows, defenders need faster exposure mapping, faster vendor review, and faster decision-making. That means knowing which assets are exposed and which delays are caused by process rather than risk. For internal support, this also aligns with Reduce Detection Time Regulatory Deadlines Risk and How to Reduce Cybersecurity Detection Time. (cloud.google.com)
The third change is cultural: vulnerability management should be treated less like backlog administration and more like threat response. If a newly disclosed issue affects an exposed identity service, appliance, VPN, or edge platform, the question should be how much attacker time you are buying by waiting. Internally, this also works with SOC Efficiency Metrics 2026. (cybersecuritytime.com)
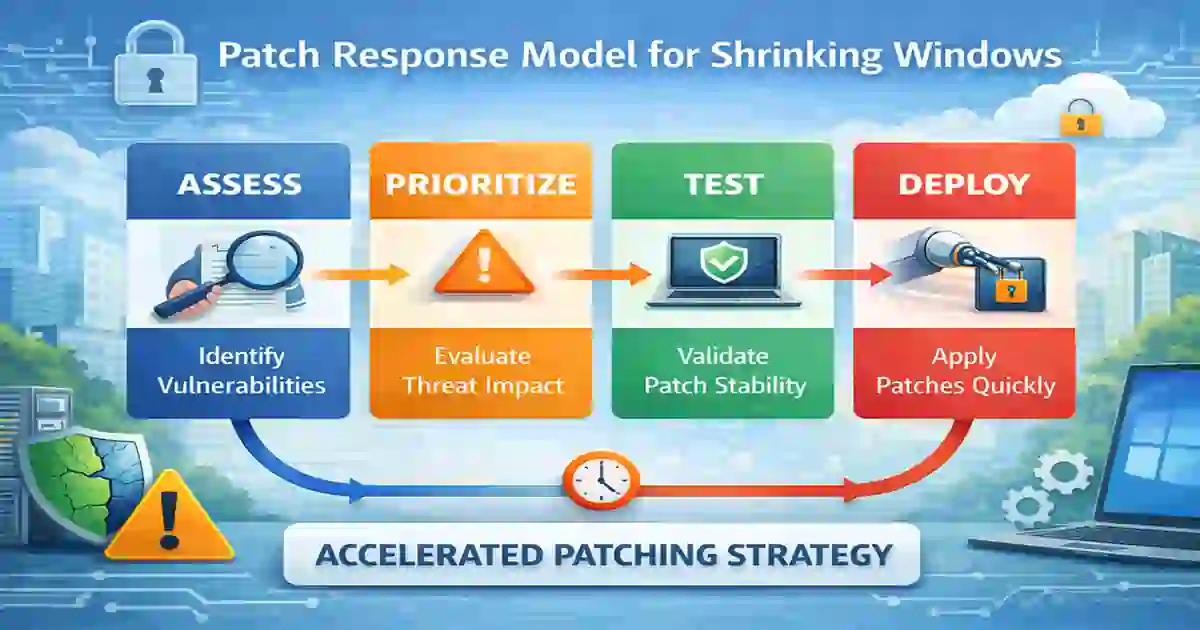
A Smarter Patch Response Model
A practical response model for AI vulnerability exploitation patch windows starts with exploitation evidence. First, check active exploitation sources such as the CISA KEV Catalog. Second, determine whether the asset is internet-facing, privileged, or business-critical. Third, assess whether a patch, mitigation, or compensating control exists. Fourth, accelerate remediation when the issue affects enterprise or edge technologies under active pressure. (cisa.gov)
In practice, organizations should separate vulnerabilities into at least two lanes: a routine patch lane and an accelerated threat lane. The accelerated lane should cover exploited flaws, highly exposed systems, and technologies where disclosure-to-exploitation timelines are compressing fastest. For internal readers, this section also pairs with Board-Level Cybersecurity Metrics Guide and Cybersecurity Metrics. (cybersecuritytime.com)
Final Verdict
The most important fact about AI vulnerability exploitation patch windows is not that AI is replacing attackers. It is that AI is compressing the time between disclosure, exploit adaptation, and target selection, which leaves defenders with less room for delay. Google’s current forecast is explicit on that point, and its 2025 data shows that the pressure is concentrated on the enterprise and edge technologies many organizations depend on most. (cloud.google.com)
For global security teams, the message is clear: AI vulnerability exploitation patch windows are shrinking because attacker workflows are speeding up. The organizations that adapt best will be the ones that prioritize exploitation evidence, exposure, and asset criticality over slow, one-size-fits-all patch cycles. For internal follow-on reading, this also supports Cybersecurity Time, How to Reduce Cyber Breach Detection Time, and Reduce Detection Time Regulatory Deadlines Risk. (cloud.google.com)
FAQ
Is AI already making exploitation faster?
Major threat intelligence guidance now expects AI to accelerate reconnaissance, vulnerability discovery, and exploit development, which makes faster exploitation more likely even when humans still direct the attack flow. (cloud.google.com)
Are patch windows shrinking only for zero-days?
No. Google says the gap is shrinking for n-day vulnerabilities too, not only true zero-days. (cloud.google.com)
Which systems are under the most pressure?
Enterprise software, operating systems, security appliances, networking devices, and edge infrastructure are under especially strong pressure based on Google’s latest review. (cloud.google.com)
What should organizations prioritize first?
Start with exploited vulnerabilities, exposed and critical assets, and technologies that sit at the perimeter or enable privileged access. CISA’s KEV catalog is one of the best starting points for that model. (cisa.gov)