Credential Stuffing vs Password Spraying: 7 Critical Risks
When defenders compare Credential Stuffing vs Password Spraying, they are looking at two login attack patterns that target the same surface but rely on different weaknesses. Both can lead to account takeover, yet they do not begin in the same way and they do not leave the same kind of evidence behind.
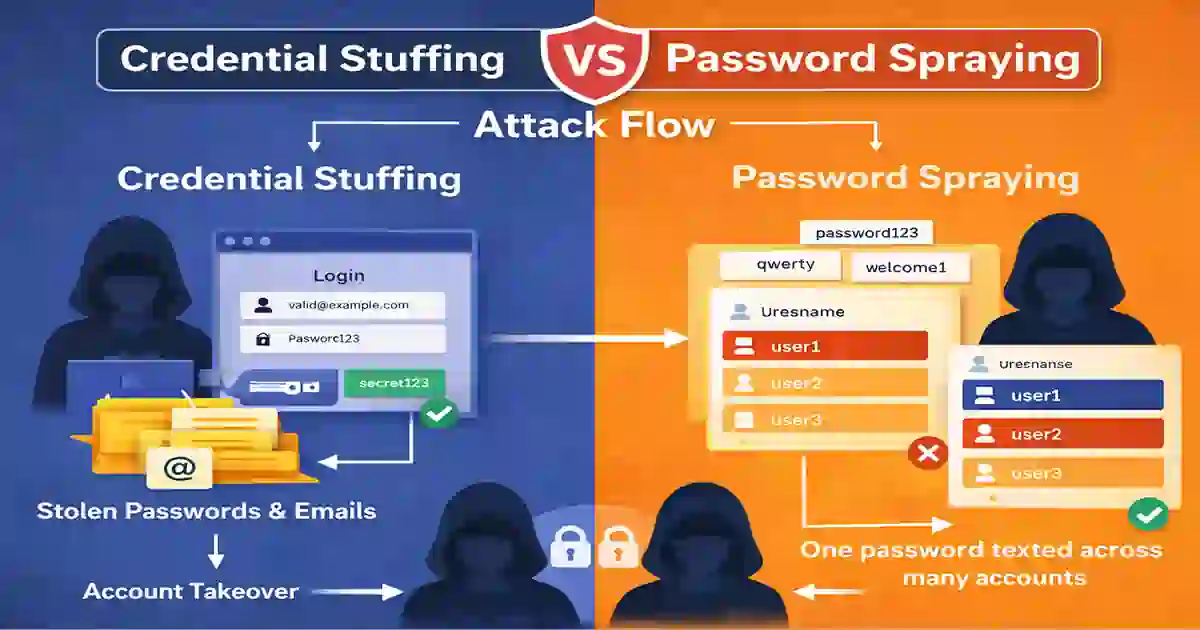
Credential stuffing uses real username-password pairs stolen from earlier breaches, credential dumps, or malware-collected logs and tests them against a different service. Password spraying works differently. Instead of relying on known credential pairs, attackers try one or a few common passwords across many accounts, usually in a way designed to avoid simple lockout thresholds. CISA lists password spraying and credential stuffing as separate brute-force sub-techniques, and Microsoft maintains a dedicated password spray investigation playbook because the detection pattern is distinct.
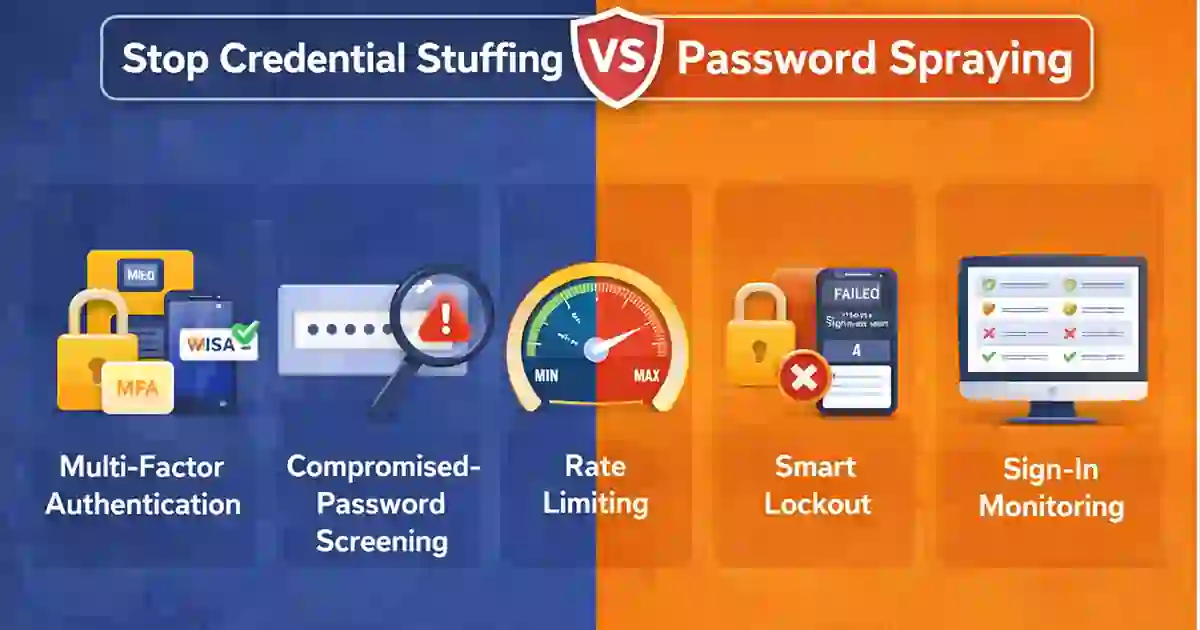
That distinction matters because the defenses are not identical. Credential stuffing depends mainly on password reuse. Password spraying depends mainly on weak or predictable password choices. NIST’s digital identity guidance continues to recommend rate limiting and screening passwords against compromised or commonly used values as important defenses against online guessing attacks.
A simple way to remember the comparison is this:
- Credential stuffing reuses credentials that are already known.
- Password spraying tests passwords that are likely to be common.
Table of Contents
What is Credential Stuffing vs Password Spraying?
Credential stuffing is an attack in which threat actors take real username-password pairs from previous compromises and test them against another website, cloud service, or application. Password spraying is different. Instead of working from known credentials, the attacker tries a small set of common passwords across a broad range of usernames. Microsoft’s password spray guidance notes that these attacks are investigated as a separate pattern because they are usually spread across many identities rather than concentrated on one account.
That is why Credential Stuffing vs Password Spraying is not just a wording issue. It affects how defenders should review failed sign-ins, configure throttling, and prioritize identity protections.
Organizations comparing these attack types should pay close attention to stronger authentication, sign-on policy, and identity monitoring. Guidance from CISA and Microsoft is useful here because both sources distinguish password spraying from broader brute-force activity.

Why These Attacks Are Often Confused
The confusion is understandable. Both attacks target authentication systems. Both can produce waves of failed sign-ins. Both can end in unauthorized access and account takeover.
But the attacker logic is different. Credential stuffing assumes that stolen credentials are still valid because users reuse passwords. Password spraying assumes that some users still choose weak or familiar passwords. That difference may sound small, but it changes what defenders should look for in logs and how they should harden sign-in workflows.
That article on your site covers strong authentication, brute-force protection, throttling, and inactive account cleanup for internet-facing systems.
7 Critical Risks in Credential Stuffing vs Password Spraying
1. The password source is different
This is the core distinction in Credential Stuffing vs Password Spraying.
Credential stuffing starts with real credentials stolen somewhere else. Password spraying starts with guesses based on common password habits. Because of that, credential stuffing is tied to password reuse, while password spraying is tied to weak-password hygiene. CISA’s technique mapping separates the two for that reason.
2. The log pattern is different
Credential stuffing usually appears as many username-password pairs being tested in volume. Password spraying usually appears as one password, or a very short list of passwords, being tried across many accounts. Microsoft’s investigation playbook highlights that broad, distributed pattern in password spray incidents.
This is why defenders who only watch for repeated failures against one account may catch noisy brute-force attempts but still miss password spraying.
3. Password spraying is often designed to stay quiet
A noisy attack is easier to catch. Password spraying is often built to avoid that. By spreading attempts across many identities and often spacing them out, attackers reduce the chance of obvious lockouts or simple threshold-based alerts. Microsoft’s playbooks explicitly frame password spray as a distinct investigative problem for this reason.
Credential stuffing can also be distributed, especially when automated tooling is involved, but its main goal is different: testing known credential pairs at scale.
4. Credential stuffing depends on password reuse
Credential stuffing succeeds when a password exposed on one service still works on another. That is why old breach data can remain valuable to attackers long after the original incident. It also explains why stolen credentials continue to show up in early-stage compromise activity.
Stolen credentials remain valuable long after the original breach because password reuse allows them to be tested across unrelated services. That is one reason credential abuse continues to appear in early-stage intrusions.
5. Password spraying depends on weak password choices
Password spraying does not require a breach dataset. It only requires that some users still choose simple or predictable passwords. That is why password blocklists, screening against common values, and smart lockout controls matter so much. NIST recommends screening memorized secrets against commonly used, expected, or compromised values, and it also requires effective rate limiting by the verifier.
6. The common targets are not always the same
Credential stuffing is especially common against consumer-facing services such as ecommerce logins, streaming accounts, travel platforms, and broad SaaS user bases. Password spraying is more often discussed in enterprise identity systems such as Microsoft 365, VPN portals, and federated sign-in environments. Microsoft’s password spray guidance is written for organization-wide investigations, which reflects that enterprise emphasis.
This enterprise emphasis matters because password spraying is often associated with broad identity systems, remote access portals, and federated sign-in environments rather than consumer account ecosystems alone.
7. The best first defense is not identical
The strongest starting controls overlap, but they are not exactly the same.
For credential stuffing, the best first steps usually include MFA, compromised-password checks, anomaly detection, and bot-aware login protection. For password spraying, the strongest first steps usually include banned-password lists, rate limiting, smart lockout, and broad monitoring across many identities. NIST’s guidance supports rate limiting and blocklists, while Microsoft’s guidance supports distinct investigation and response for password spray activity.
Safer defaults reduce exposure before an attacker ever reaches the login page, which is why prevention matters as much as detection.
Which Attack is Harder to Detect?
Between the two, password spraying is often harder to detect early in enterprise environments because the activity is intentionally spread out and may resemble ordinary failed sign-ins at first. Microsoft’s investigation guidance supports that view by focusing on broad patterns across many accounts rather than a burst against one user. Credential stuffing can also be difficult to identify, especially when attackers use rotating infrastructure, but its signature is still different: many real credential pairs being tested in volume.
That is why defenders should separate Credential Stuffing vs Password Spraying in their detection logic instead of treating every login attack as a single category.
How to Reduce Credential Stuffing vs Password Spraying Risk
The most practical defense is a layered one.
Organizations should require MFA where possible, screen passwords against common and compromised values, apply rate limiting to failed logins, disable stale accounts, and monitor failed sign-ins across the whole environment rather than only per user. NIST explicitly supports rate limiting and password screening, and Microsoft’s password spray playbooks reinforce the need for broad sign-in visibility.
Credential abuse rarely exists in isolation. In many intrusions, stolen credentials or weak authentication controls are only the beginning, followed by broader privilege abuse, persistence, and lateral movement. That is why layered identity defenses should be treated as part of a wider intrusion-prevention strategy. NIST Digital Identity Guidelines and the Microsoft password spray investigation guide.
Credential Stuffing vs Password Spraying: Final Comparison Table
| Factor | Credential Stuffing | Password Spraying |
|---|---|---|
| Password source | Stolen real credentials | Common guessed passwords |
| Main weakness exploited | Password reuse | Weak password choices |
| Attack pattern | Many username-password pairs | One or a few passwords across many accounts |
| Breach data required | Usually yes | No |
| Lockout avoidance | Sometimes | Often central to the tactic |
| Common targets | Consumer platforms and web services | Enterprise identity systems |
| Best first defense | MFA and compromised-password checks | Banned passwords and smart lockout |
These distinctions align with CISA’s technique mapping, Microsoft’s investigation playbooks, and NIST’s defensive guidance on online guessing and password screening.
Conclusion
In the end, Credential Stuffing vs Password Spraying is really a comparison between two different paths to account takeover.
Credential stuffing is about reusing credentials that are already known. Password spraying is about testing passwords that are likely to be common. Both are serious, but they exploit different weaknesses and should not be defended in exactly the same way. The strongest programs treat them as separate risks and respond with layered identity controls built around MFA, weak-password prevention, compromised-password screening, rate limiting, and better visibility into authentication behavior.