Cyber Risk Planning Tool
Data Breach Cost Estimator
Estimate breach impact, urgency, cost drivers, and containment priorities in minutes.
Enter your scenario to see plain-English risk meaning.
Check whether regulator, customer, vendor, insurance, or contractual notification is required.
2. Main cost drivers
This helps users understand why the estimate changed.
3. What to do next
Prioritize containment, evidence, notification review, and safe recovery.
4. Board / owner summary
Copy, print, or save this for internal planning.
Privacy Note: This tool is designed for educational use. It should calculate results in the browser and should not store your answers unless you separately add tracking, forms, or analytics.
Data Breach Cost Estimator: Know the Risk Before It Becomes a Crisis
Data Breach Cost Estimator helps you understand how much a data breach could cost your business, website, online store, agency, or organization. A breach can create more than one problem. It can stop operations, expose customer records, damage trust, increase legal pressure, trigger ransomware recovery costs, and force urgent security work.
This tool is made for real users, not only cybersecurity experts. You do not need complex technical knowledge. Enter basic details such as company size, records exposed, downtime, legal exposure, sector, detection delay, and ransomware involvement. The Data Breach Cost Estimator then gives a rough impact range and shows what you should fix first.
This is useful because most people do not ask, “How much could a breach cost?” until something has already gone wrong. By then, the business may already be losing money, customers may be worried, and staff may not know what to do next.
Use this tool as an early-warning guide. It is not legal advice, insurance advice, forensic advice, or a formal audit. It is a practical calculator that helps you move from confusion to action.

Why This Tool Matters
A data breach is not only an IT issue. It is a business issue. If your website, email, cloud account, customer database, payment system, or employee files are affected, the impact can spread quickly.
The Data Breach Cost Estimator helps answer important questions:
- How serious could this incident become?
- What is increasing the cost?
- Is downtime the biggest problem?
- Are customer records involved?
- Does ransomware make it urgent?
- Should legal, insurance, or incident response support be contacted?
- What action should come first?
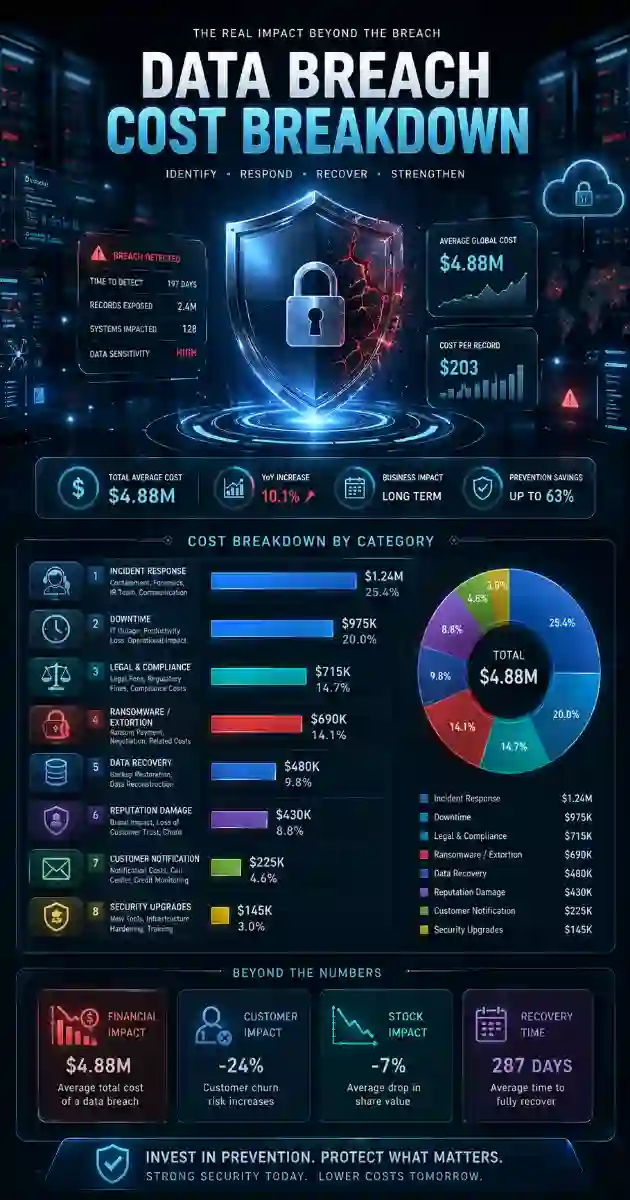
IBM’s 2025 Cost of a Data Breach Report is widely used as a breach-cost benchmark, and public reporting around that report lists the global average breach cost at about USD 4.44 million. The exact cost for each business is different, but the lesson is clear: faster detection, stronger preparation, and better response planning matter.
What is the Data Breach Cost Estimator?
The Data Breach Cost Estimator is a public-friendly cybersecurity calculator. It gives a rough estimate of possible breach impact based on common risk factors.
It is designed to be simple, but still useful. Instead of giving only one number, a strong estimator should explain what is driving the cost. A breach involving 200 records and no downtime is very different from a ransomware incident involving 50,000 records, customer data, several days of downtime, and weak backups.
This tool helps translate cybersecurity risk into business language. That makes it easier for owners, managers, clients, and non-technical users to understand the situation.
Who Should Use This Tool?
The Data Breach Cost Estimator is useful for:
- Small business owners
- Website owners
- Ecommerce stores
- SaaS companies
- Marketing agencies
- IT support providers
- Managed service providers
- Healthcare clinics
- Finance firms
- Law firms
- Accounting firms
- Schools and nonprofits
- Freelancers and consultants
- Cybersecurity awareness teams
Any organization that stores customer data, employee records, payment-related information, login credentials, private files, or business documents can use this tool to understand possible impact.
What Inputs the Tool Uses
The Data Breach Cost Estimator uses practical inputs that normal users can answer.
Company Size
Company size affects how complex recovery may become. A larger organization may have more staff, systems, customers, vendors, contracts, and public communication needs.
Records Exposed
Records exposed means the estimated number of customer, employee, user, or business records affected. More records can increase notification work, legal review, support requests, and trust damage.
Downtime
Downtime is one of the easiest costs to feel. If your website, online store, booking system, email, payment platform, or internal tools stop working, revenue and productivity can drop quickly.
Sector
Some sectors have higher risk because they handle sensitive data. Healthcare, finance, legal, education, ecommerce, SaaS, and professional services often need stronger response planning.
Detection Delay
A breach found quickly is usually easier to contain. A breach that stays hidden can increase investigation time, attacker activity, and exposure.
Legal Exposure
Legal exposure depends on the affected country, data type, contracts, customers, and applicable regulations. Personal data, financial data, health data, children’s data, login credentials, and identity documents usually require more care.
Ransomware Involvement
Ransomware can increase urgency because systems may be encrypted, backups may be targeted, and stolen data may be used for extortion. CISA’s StopRansomware Guide is designed to help organizations reduce ransomware risk and respond more effectively.
How to Understand Your Result
Your result should not be treated as a final invoice. It is a planning estimate.
A good result should show:
- Estimated low-to-high breach cost range
- Likely midpoint estimate
- Risk level
- Main cost drivers
- Ransomware warning if relevant
- Downtime warning if relevant
- Legal exposure reminder
- Containment priorities
- Simple business-owner summary
This makes the tool more useful than a basic calculator. Users do not only want numbers. They want to know what the number means and what to do next.
7 Powerful Risk Fixes After a Breach Estimate
1. Isolate affected systems
If a system may be compromised, disconnect it from the network where safe to do so. Do not destroy evidence. The goal is to stop further damage while preserving useful information.
2. Preserve logs and evidence
Save alerts, screenshots, server logs, firewall logs, email headers, user activity, payment alerts, and suspicious files. Evidence helps investigators understand what happened.
3. Reset passwords and remove suspicious access
Reset passwords for affected accounts. Revoke suspicious sessions. Remove old users. Check administrator accounts first because attackers often target privileged access.
4. Check backups before restoring
Do not assume backups are safe. Confirm that backups exist, are clean, and can actually be restored. This is especially important when ransomware is involved.
5. Identify what data was affected
Try to understand whether customer records, employee records, payment-related data, login credentials, private documents, or regulated data were accessed, stolen, changed, or deleted.
6. Review notification duties
Some incidents may require notification to customers, regulators, partners, insurers, or payment providers. In the EU, qualifying personal data breaches may require notification to the supervisory authority without undue delay and within 72 hours after awareness.
7. Fix the root cause
After containment, fix the weakness that allowed the incident. This may involve patching software, removing malware, improving MFA, disabling unused accounts, securing cloud storage, or improving monitoring.
International Notes for Premium Countries and Europe
The Data Breach Cost Estimator is useful for global audiences, especially in high-value digital markets such as the United States, Canada, United Kingdom, European Union, Germany, France, Netherlands, Switzerland, Australia, New Zealand, and UAE/Dubai.
International users should remember that breach response rules can vary by country, sector, contract, and data type. The EU has specific personal data breach notification rules, while other countries may have different timelines and thresholds. The FTC also provides business guidance on data breach response and consumer protection in the United States.
For a more structured security program, NIST Cybersecurity Framework 2.0 organizes cybersecurity outcomes around Govern, Identify, Protect, Detect, Respond, and Recover. This is helpful because breach cost is not only about response. It is also about preparation, governance, detection, and recovery.
Related Cybersecurity Time Tools
Frequently Asked Questions
What is the Data Breach Cost Estimator?
The Data Breach Cost Estimator is an educational cybersecurity tool that estimates possible breach impact using company size, exposed records, downtime, ransomware involvement, legal exposure, sector, and detection delay.
Is this tool only for large companies?
No. Small businesses, ecommerce stores, agencies, startups, nonprofits, consultants, and website owners can also use it. A smaller breach can still cause serious damage if customer data, passwords, payments, or business systems are affected.
Does this tool replace a cybersecurity expert?
No. It gives a rough estimate and practical next steps. A real incident may require legal advice, cyber insurance review, forensic investigation, and professional incident response support.
Why does ransomware increase breach cost?
Ransomware can increase cost because systems may be locked, backups may be damaged, stolen data may be threatened, and recovery may require specialist help.
What should I do first after a breach?
Start by isolating affected systems, preserving evidence, resetting compromised credentials, checking backups, identifying affected data, and reviewing notification duties.
Does the tool store my answers?
The recommended plugin version should calculate results in the browser and avoid storing visitor answers. Add a clear privacy note below the tool for user trust.
