Finance Sector Cybersecurity Checklist 2026: 17 Urgent Fixes
Cybersecurity in the financial sector is usually discussed in broader terms than system protection alone. Banks, insurers, payment providers, investment firms, and fintech platforms depend on technology for customer access, transaction processing, internal operations, third-party connectivity, and regulatory reporting. As a result, weaknesses in cybersecurity can affect not only confidentiality and integrity, but also service availability, customer trust, operational continuity, and legal exposure.
For that reason, a finance sector cybersecurity checklist 2026 is most useful when it is treated as a structured review of resilience rather than a simple list of technical settings. A workable checklist should help an organization identify its most important services, understand the dependencies behind them, review common sources of cyber risk, and assess how well it can respond when a disruption occurs.
This article presents a practical checklist in that sense. It is written for financial institutions that want a readable reference point rather than a sales-style guide or an overly compressed compliance summary.

Table of Contents
Why the financial sector needs a dedicated checklist
Cybersecurity guidance is often written in generic language, but financial organizations usually face a more concentrated combination of risks than many other industries. They manage sensitive financial and identity data, support high-value transactions, depend on tightly connected systems, and often rely on a wide range of external service providers. A technical issue can therefore become a business issue very quickly.
A payment outage, unauthorized access to accounts, failure of a critical vendor, or compromise of administrative credentials may affect customers directly and may also require immediate internal escalation. In that environment, security controls need to be considered alongside governance, operational resilience, reporting, fraud prevention, and third-party oversight.
A useful finance sector cybersecurity checklist 2026 should reflect those realities. It should not only ask whether a control exists, but whether it supports the way the institution actually operates.
That is why a finance sector cybersecurity checklist 2026 should focus not only on technical controls, but also on third-party oversight, resilience testing, and decision-making under regulatory pressure.

How to Use This Finance Sector Cybersecurity Checklist 2026
This checklist can be used in several ways.
For leadership teams, it can serve as a plain-language review of whether major cyber risks are visible, owned, and discussed at the right level. For security and infrastructure teams, it can act as a maturity check across core technical and operational controls. For risk and compliance teams, it can help connect cyber safeguards to oversight, resilience, and incident handling.
It is also useful as a reference point during audits, customer assurance reviews, internal planning, and governance discussions. A checklist is most effective when it helps different teams speak about the same issues in consistent terms.
Used properly, a finance sector cybersecurity checklist 2026 helps teams prioritize the controls that matter most to business services, customer trust, and regulatory readiness.
Relevant internal reading that fits naturally around this topic includes the Data Breach Timeline Template, the Third-Party Risk Assessment Checklist, the Okta Security Checklist, Mean Time to Detect, Mean Time to Respond, and MTTD vs MTTR vs MTTC vs Dwell Time.
Finance Sector Cybersecurity Checklist 2026: Core Review Areas
Finance sector cybersecurity checklist 2026 is a practical framework for banks, insurers, payment providers, fintech teams, and other financial organizations that need to reduce cyber risk without losing sight of operational pressure.
1. Define governance and accountability clearly
A financial organization should be able to explain who owns cybersecurity risk, how major issues are escalated, how often leadership reviews cyber matters, and which decisions require executive or board attention. Governance is most effective when responsibility is visible in practice rather than described only in policy language.
2. Identify important business services
Many security programs are organized around systems, but disruption is usually experienced through services. Financial firms should identify the services that matter most to customers and operations, such as payments, account access, lending operations, claims handling, trading, settlement, or treasury workflows. Once those services are defined, it becomes easier to assess dependencies and recovery priorities.
3. Maintain an accurate asset inventory
An institution should have a current view of its servers, endpoints, applications, cloud assets, internet-facing systems, administrative tools, and sensitive data stores. Asset visibility remains one of the foundations of cybersecurity because patching, monitoring, segmentation, and response all depend on it.
4. Strengthen identity controls
Identity remains one of the most common entry points for attackers. Weak authentication, poorly governed sign-on processes, stale accounts, and excessive privileges can all increase the chance that a routine compromise becomes a larger incident. Stronger identity governance, access reviews, and more reliable authentication controls are therefore central to financial-sector security.
For many firms, identity remains the most important section of a finance sector cybersecurity checklist 2026 because weak authentication and poor privilege design increase both breach risk and recovery time.
link: Passkeys vs MFA vs SMS 2FA
5. Review privileged access separately
Administrative access should not be treated as an ordinary extension of user access. Privileged accounts connected to cloud consoles, production systems, payment infrastructure, customer identity stores, and internal management tools should be controlled more tightly and reviewed more often.
6. Segment sensitive environments
Network and environment segmentation can reduce the effect of lateral movement after an initial compromise. Core applications, regulated data environments, customer identity systems, payment platforms, and other sensitive services should be separated according to business importance and access needs.
7. Review cloud and SaaS exposure
Cloud platforms and SaaS services are now deeply embedded in many financial environments. Permissions, logging, exposed integrations, storage configuration, encryption settings, and tenant administration should all be reviewed regularly. In many cases, cyber exposure grows gradually through convenience rather than through a single obvious mistake.
8. Prioritize vulnerability management by business risk
Not all vulnerabilities present the same level of danger. Financial firms generally need to prioritize internet-facing systems, identity infrastructure, remote access pathways, and assets that support important business services. The aim is not only to patch quickly, but to make decisions based on likely exploitability and operational consequence.
link: Ransomware Initial Access 2026
9. Improve detection quality
Detection is more useful when it focuses on activity that would genuinely matter in a financial environment. This may include suspicious logins, privilege escalation, abnormal administrative actions, unusual access to sensitive data, and anomalies in transaction-related behavior. A large volume of alerts is less useful than timely visibility into activity that signals real risk.
links: Mean Time to Detect and MTTD vs MTTR vs MTTC vs Dwell Time
10. Test incident response realistically
Incident response in finance often involves more than the security team. Legal, compliance, operations, communications, fraud teams, and senior leadership may all need to act in a short period of time. Tabletop exercises and scenario testing are most useful when they examine how those groups actually interact under pressure.
link: Data Breach Timeline Template
11. Clarify incident classification and reporting paths
Confusion during incidents often comes from uncertainty about classification, significance, and escalation. Firms should define how incidents are reviewed, who makes decisions, how facts are documented, and how reporting or disclosure processes are triggered. Clear process design reduces uncertainty during live events.
12. Assess third-party risk in business terms
Third-party risk is not limited to questionnaires or contract review. A vendor may introduce substantial operational exposure because it supports a critical service, has access to important systems, or represents a concentration dependency. Third-party review is strongest when it is connected to service mapping and operational impact.
No finance sector cybersecurity checklist 2026 is complete without measuring third-party risk in business terms such as service dependency, customer impact, and reporting obligations.
link: Third-Party Risk Assessment Checklist
13. Include software delivery and change processes
For digital banks, fintechs, and technology-heavy financial firms, software delivery forms part of the operational attack surface. Code repositories, pipelines, secrets management, build systems, and deployment controls should therefore be reviewed as part of the cybersecurity program rather than as a separate engineering concern.
14. Confirm backup and recovery capability
Backups are useful only when recovery works as expected. Financial firms should know whether important services can actually be restored, whether backup data is protected against tampering, and whether restoration has been tested under realistic conditions.
15. Exercise resilience scenarios
Resilience exercises can help reveal hidden dependencies, unclear ownership, and unrealistic recovery assumptions. Financial organizations benefit most from scenarios that involve both technical and operational consequences, such as supplier failure, account compromise, service disruption, or a prolonged outage affecting customer operations.
16. Use threat intelligence and metrics in a practical way
Threat intelligence and operational metrics are most valuable when they improve decisions. Detection time, response time, containment time, and dwell time can help an institution assess whether its controls are improving in practice. Metrics should support prioritization and learning rather than exist only for reporting.
links: Mean Time to Respond and MTTD vs MTTR vs MTTC vs Dwell Time
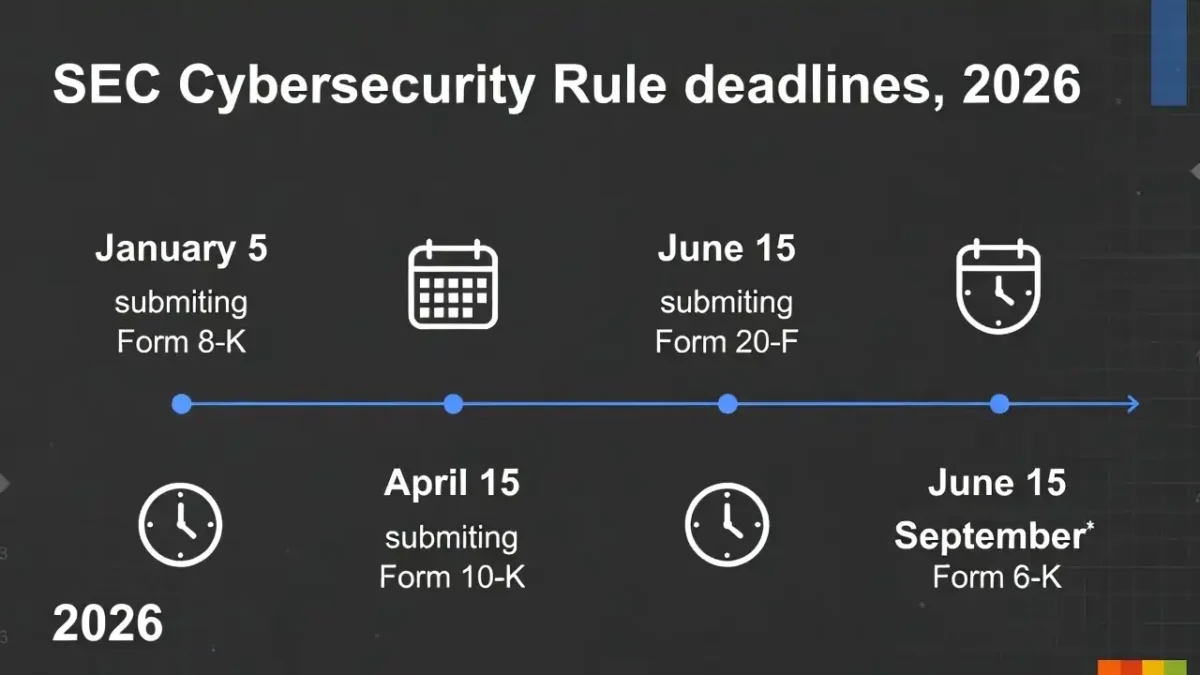
17. Map the checklist to a recognized framework
A checklist is easier to maintain when it is aligned to a broader structure. Doing so helps security, compliance, and leadership teams evaluate progress consistently and communicate using a shared model. External references such as NIST Cybersecurity Framework 2.0, the SEC cybersecurity disclosure rule, FCA operational resilience, and the NCSC Cyber Assessment Framework fit naturally in this section.
Common weaknesses that still appear in practice
Even mature organizations often show the same recurring gaps. Identity controls may be stronger than service dependency mapping. Vendor oversight may appear complete on paper while concentration risk remains poorly understood. Incident response plans may exist, but executive decision-making and reporting workflows may still feel uncertain when tested.
Another common issue is imbalance. Some institutions invest heavily in visible tools while underinvesting in inventories, access reviews, backup validation, segmentation, restoration testing, and escalation clarity. Those quieter disciplines are often the controls that matter most when an incident becomes operational.
A well-built finance sector cybersecurity checklist 2026 should be reviewed regularly as threats, suppliers, business services, and regulatory expectations change.
Conclusion
This finance sector cybersecurity checklist 2026 is most useful when it is treated as a working review tool rather than a one-time compliance exercise. It helps financial organizations connect governance, identity security, service continuity, vendor oversight, detection, response, and recovery into a single operating picture.
That is what makes such a checklist useful. It does not simply show whether controls exist. It helps show whether those controls support the way the institution actually works, and whether the organization is prepared to continue operating when conditions are no longer normal.