Supplier Cybersecurity Contract Template: 7 Best Tips
A Supplier Cybersecurity Contract Template is a practical resource used to define security obligations for vendors, suppliers, consultants, software providers, and outsourced partners. It helps organizations put cybersecurity expectations into written contract language before a supplier is allowed to access systems, data, or critical business services.
This topic fits naturally with supplier due diligence and third-party risk review. For example, organizations often begin vendor evaluation with a Vendor Security Questionnaire Template and a Third-Party Risk Assessment Checklist, then use contract clauses to formalize the controls a supplier must maintain.
Cybersecurity requirements in contracts often include access control, encryption, incident reporting, subcontractor restrictions, and business continuity terms. These controls help reduce the chance that a third-party weakness turns into a larger data breach or service disruption.

Table of Contents
What is a Supplier Cybersecurity Contract Template?
A Supplier Cybersecurity Contract Template is a structured set of clauses used during procurement, onboarding, legal review, or contract renewal. It helps businesses standardize security requirements across vendor agreements instead of drafting every clause from scratch.
This approach supports broader computer security and risk management goals. On Cybersecurity Time, it also connects naturally with resources such as the Information Security Guide and Cybersecurity Best Practices, because supplier security is part of a wider security governance program.
Why Supplier Cybersecurity Clauses Matter
Supplier cybersecurity clauses matter because vendors often process customer data, access internal systems, manage software, or support business operations. If a supplier is compromised, the customer organization may face security, operational, legal, or compliance consequences.
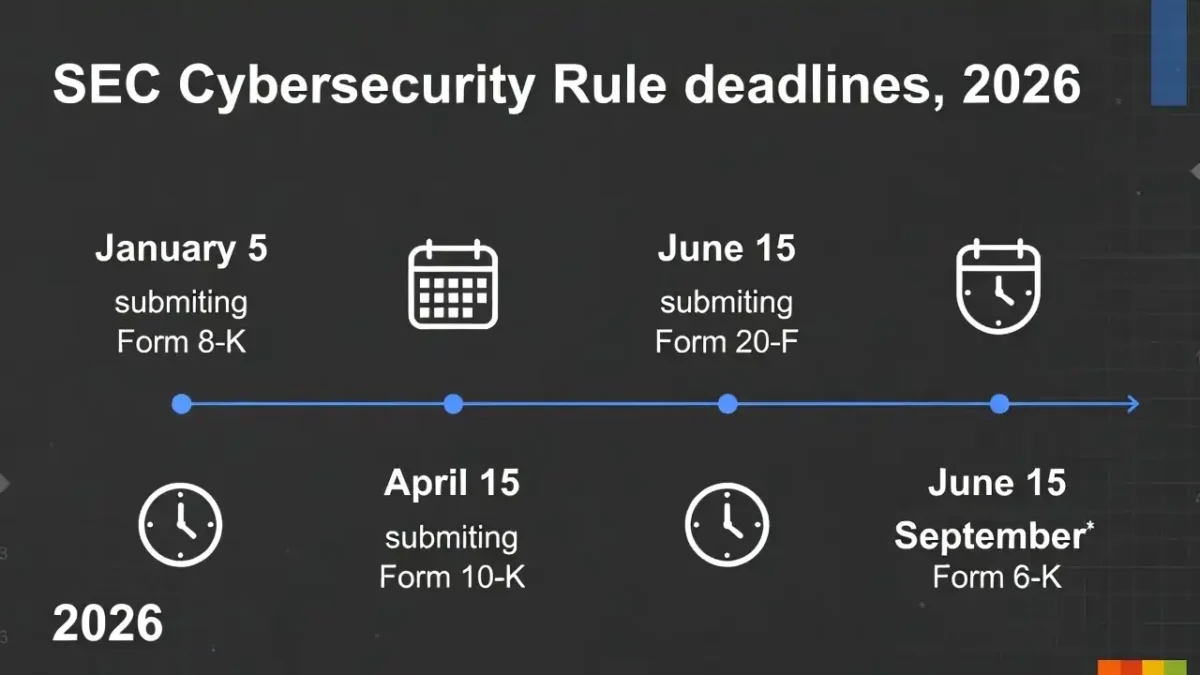
That is why contracts should clearly define obligations for security controls, reporting timelines, and vendor accountability. This becomes especially important when organizations must meet strict incident or disclosure timelines, as discussed in Incident Response Deadlines US UK and Cybersecurity Incident Response Timeline.

Common Sections in a Supplier Cybersecurity Contract Template
Most Supplier Cybersecurity Contract Template documents include several common sections.
Information Security Governance
This section states that the supplier must maintain documented security policies, assign responsibility for security oversight, and support basic governance requirements. This aligns with the broader principles explained in Information Security Guide.
Access Management
This section defines how supplier access is granted, reviewed, limited, and removed. In general security terms, access control refers to restricting access to authorized users and approved resources.
Encryption and Data Protection
This section explains how sensitive information must be protected while stored or transmitted. In general terms, encryption is used to protect information from unauthorized access.
Incident Reporting
This section defines when and how a supplier must report a suspected or confirmed security incident. This area can link naturally to Incident Response Deadlines US UK and SEC vs UK Cyber Reporting Deadlines.
Audit and Assurance
This section gives the customer the right to request evidence of controls, such as policies, assessments, summaries, or certifications.
Subcontractor Controls
This section explains whether subcontractors may be used and whether equivalent obligations must flow down to them.
Business Continuity and Recovery
This section addresses resilience, backup, continuity, and recovery planning. It also fits well with Average Time to Detect Cyber Attack and How to Reduce Cybersecurity Detection Time, because resilience depends on both prevention and fast detection.
7 Best Tips for a Supplier Cybersecurity Contract Template
1. Define Security Governance Clearly
Require the supplier to maintain security policies and assign responsibility for cybersecurity oversight.
2. Limit Access to Authorized Users
State that supplier access must follow least-privilege principles and be reviewed regularly.
3. Require Encryption
Include a clause requiring encryption or equivalent safeguards for sensitive data.
4. Set Incident Reporting Timelines
Require suppliers to notify your organization without undue delay after a suspected or confirmed incident.
5. Add Vulnerability Management Expectations
Require the supplier to identify and remediate vulnerabilities in systems used to deliver the service.
6. Include Logging and Monitoring Controls
Require appropriate logging, monitoring, and detection measures. This fits well with Cybersecurity Incident Response Timeline.
7. Define Data Return or Deletion
At contract end, require the supplier to return or securely delete customer data in accordance with the agreement.

Final Thoughts
A Supplier Cybersecurity Contract Template helps organizations turn security expectations into written supplier obligations. It supports stronger procurement, clearer accountability, and better protection against third-party cyber risk.
For CybersecurityTime.com, this topic works well with existing content such as Vendor Security Questionnaire Template, Third-Party Risk Assessment Checklist, Cybersecurity Best Practices, and Incident Response Deadlines US UK. Together, these pages create a strong internal content cluster around supplier security, vendor risk, and incident readiness.