Ransomware Initial Access in 2026: Brute Force, Stolen Credentials, and Exploits

Ransomware initial access 2026 is still driven by a small number of practical entry points. The most common patterns remain brute force attacks against exposed services, stolen credentials used as valid access, and exploitation of unpatched internet-facing systems. Microsoft’s latest Digital Defense Report says incident-response cases commonly began with phishing or social engineering, unpatched web assets, and exposed remote services.
That matters because ransomware usually does not begin with encryption. It begins with access. Once attackers establish a foothold, they can move into privilege escalation, internal discovery, lateral movement, and data theft before the final extortion stage. This is why your internal guide on the Ransomware Attack Timeline fits naturally near the beginning of the article. The same progression is also reflected in your Ransomware Detection Timeline.
For readers who want basic background definitions, ransomware is malicious software used to block access to systems or data, usually for extortion. In practice, though, the more useful security question is not what ransomware is, but how the attacker got in before deployment.
Table of Contents
What Ransomware Initial Access Means
Ransomware initial access is the moment an attacker first gets into an environment.
That access may come from a guessed password, a stolen login session, a compromised admin account, a vulnerable edge device, or a flaw in a public-facing application. In plain language, it is the point where the attacker stops being outside and starts being inside.
This is why ransomware initial access 2026 matters so much. If defenders interrupt the intrusion here, the rest of the attack often never happens.
Stopping an intrusion at the initial access stage can prevent privilege escalation, lateral movement, data theft, and eventual ransomware deployment.
For broader background, computer security and identity and access management This early stage sits at the intersection of basic computer security and identity and access management, because both disciplines shape how attackers gain and keep access.
Why Ransomware Initial Access 2026 Still Matters
Security teams often spend too much time thinking about ransomware execution and not enough time thinking about the access path that made it possible. That is usually where the real failure happens.
Microsoft’s published incident-response data says 28% of investigated breaches began with phishing or social engineering, 18% with unpatched web assets, and 12% with exposed remote services. Those figures point to the same conclusion: identity security, patching, and exposure reduction still shape the early stage of many serious attacks.
Ransomware prevention depends on broad security hygiene, especially strong authentication, exposure reduction, cloud hardening, and disciplined patch management.
Brute Force Attacks Still Work
Brute force remains one of the simplest access methods because many organizations still expose remote services to the internet with weak passwords, poor throttling, or incomplete MFA. In current threat reporting, attackers continue to use password spraying and weak or default credentials against public-facing services. That is one reason brute force still matters in ransomware initial access 2026.
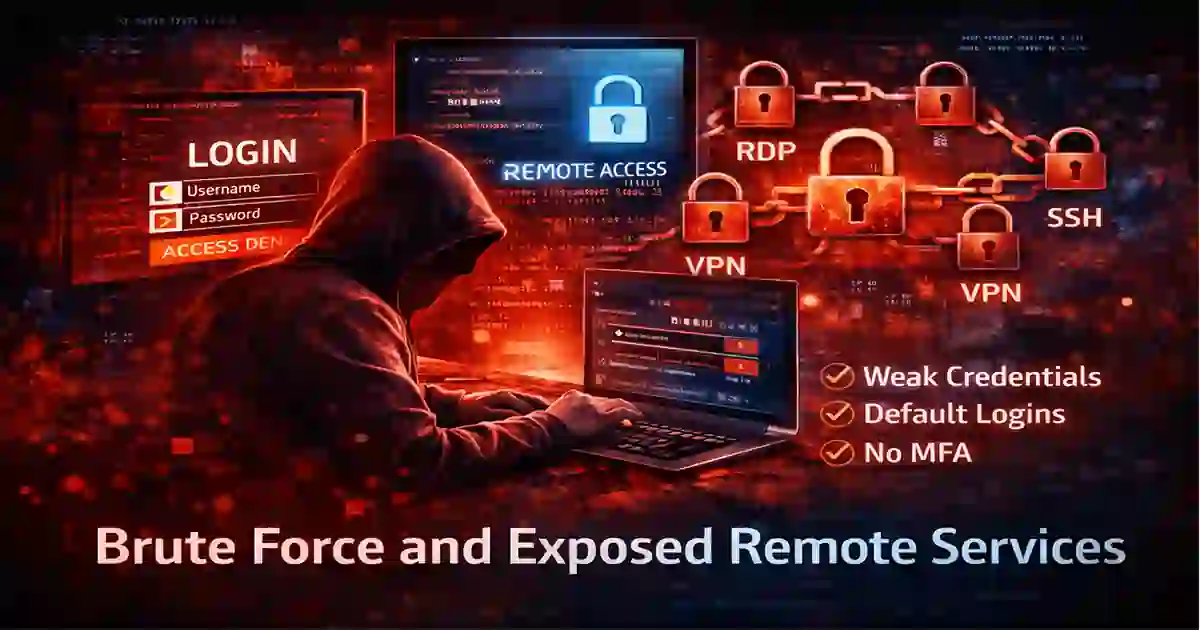
These internet-facing services deserve strict hardening and monitoring because they are often the first systems attackers test for weak access controls.
What to check
- Internet-exposed remote admin services
- Weak or reused passwords
- Missing account lockout or throttling
- Default credentials on appliances
- Remote access paths without strong MFA
For readers who want a basic definition, brute-force attack At this point, it helps to distinguish brute-force attempts from password spraying and credential reuse, because the detection patterns are not identical.
Stolen Credentials Are Harder to Detect
Stolen credentials are one of the clearest themes in ransomware initial access 2026. Attackers increasingly prefer to log in as normal users instead of launching noisy malware at the start of the intrusion.
This creates a serious visibility problem. A successful login can look legitimate unless defenders also check the surrounding context, such as device trust, session behavior, impossible travel, repeated MFA prompts, and unusual privilege use.
Phishing-resistant authentication reduces the value of stolen passwords and makes account takeover materially harder.
What to check
- Unusual successful logins
- Impossible travel alerts
- Repeated MFA prompts
- Dormant accounts becoming active again
- New device registrations tied to sensitive accounts
For general background, credential stuffing and phishing Credential theft often starts with phishing, credential stuffing, or session abuse rather than with malware at the first step.
Exploits Still Open the Door
Exploitation remains a major access route because public-facing systems are still patched too slowly or exposed too broadly. Microsoft’s report says 18% of incident-response breaches began through unpatched web assets. That is why exploits remain central to ransomware initial access 2026 even when the vulnerabilities are already known and already fixable.
Internet-facing web applications, VPN gateways, appliance firmware, identity systems, and remote management platforms should sit near the top of the patch queue. This section pairs well with your internal post on Edge VPN Vulnerabilities to Patch First in 2026 and with the more general Cybersecurity Best Practices page. The site’s recent content clearly treats edge and identity exposure as priority risks.
What to check
- Unpatched public-facing applications
- Legacy or unsupported edge devices
- Known remote-code-execution flaws
- Authentication bypass vulnerabilities
- Public proof-of-concept exploits for exposed systems
For broader explanation, exploit (computer security) is In practical terms, exploitation means attackers are using a known or newly discovered weakness to gain access before defenders close it.
Why Attackers Combine Methods
One of the most common defensive mistakes is treating brute force, stolen credentials, and exploits as if they were separate subjects.
In real intrusions, they overlap.
An attacker may phish a user, collect credentials, use those credentials on an exposed service, and then exploit an internal weakness to move further. Your Top Cybersecurity Threats to Watch in 2026 article already frames threats as structured stages rather than isolated incidents, which In real intrusions, access methods overlap and often appear as a chain rather than a single isolated event.
This is why ransomware initial access 2026 should be understood as an access chain, not just one login event.
How to Reduce Ransomware Initial Access 2026 Risk
To reduce ransomware initial access 2026 risk, organizations need stronger identity controls, less internet exposure, faster patching, and better early detection.
1. Strengthen identity security
Use phishing-resistant MFA, reduce unnecessary privileges, and monitor risky login behavior closely. Identity hardening should focus on phishing-resistant MFA, privilege reduction, risky-sign-in monitoring, and tighter administrative controls.
2. Reduce exposed remote services
Remove unnecessary public access to RDP, VPN portals, admin panels, and management interfaces. Exposure reduction is often more effective than simply adding more monitoring to a weak access path.
3. Patch public-facing assets first
External systems should be patched before less exposed internal systems. That priority is consistent with Microsoft’s reported breach patterns involving unpatched web assets and exposed services.
4. Improve early detection
Look for brute-force attempts, suspicious successful logins, unusual admin actions, privilege escalation attempts, and new attacker tooling before the encryption stage begins.
5. Measure detection and containment speed
Detection and containment time affect how far attackers can progress after initial access. Detection and containment speed determine how far an attacker can move after initial access and before business impact becomes severe.

Resources
Final Thoughts
The biggest lesson from ransomware initial access 2026 is that defenders need to stop access abuse before ransomware deployment begins. Brute force against exposed services, stolen credentials used as valid access, and exploit-driven compromise remain the most practical ways attackers get in. That is consistent with Microsoft’s reported emphasis on phishing or social engineering, unpatched web assets, and exposed remote services as common starting points in incident-response cases.
The defensive answer is straightforward. Reduce exposure, harden identity, patch faster, and detect access abuse earlier. Your existing Cybersecurity Time content already supports that argument well, especially the posts on ransomware timelines, phishing-resistant authentication, public-facing application security, and incident response timing.