CISA KEV Update: 7 Critical Flaws to Patch
A CISA KEV update is one of the clearest short-term signals available to vulnerability management teams. CISA’s Known Exploited Vulnerabilities catalog is not a general list of serious software flaws. It is a catalog of vulnerabilities that CISA says are known to be exploited in the wild, and CISA explicitly recommends that organizations use it as an input to vulnerability prioritization.
That is what gives the catalog practical value. Most security teams already have more findings than they can remediate at once. A weekly KEV review does not replace asset context, change control, or normal patch governance, but it does help answer a simpler operational question: which vulnerabilities have moved from theoretical risk into confirmed attacker activity. This is also why the topic fits naturally with internal reading such as KEV vs CVSS Patch Priority: 7 Critical Facts, Patch Management SLA Template: Critical, High, Medium, Low, and Edge VPN Vulnerabilities to Patch First in 2026.
Table of Contents
What a CISA KEV update means
A CISA KEV update is a current view of the newest additions and changes in the Known Exploited Vulnerabilities catalog. The catalog became especially prominent through Binding Operational Directive 22-01, which requires U.S. federal civilian agencies to remediate listed vulnerabilities by assigned due dates, but the catalog is also useful to private organizations because it reflects confirmed exploitation rather than severity alone.
In practical terms, this makes the KEV catalog more actionable than a long stream of scanner findings. A vulnerability can score highly in CVSS and still have little immediate relevance to a particular environment. A KEV-listed item, by contrast, is a stronger indicator that defenders should at least ask whether the product is present, exposed, and business-critical. That is the same prioritization question explored in KEV vs CVSS Patch Priority: 7 Critical Facts.
What changed in this week’s CISA KEV update
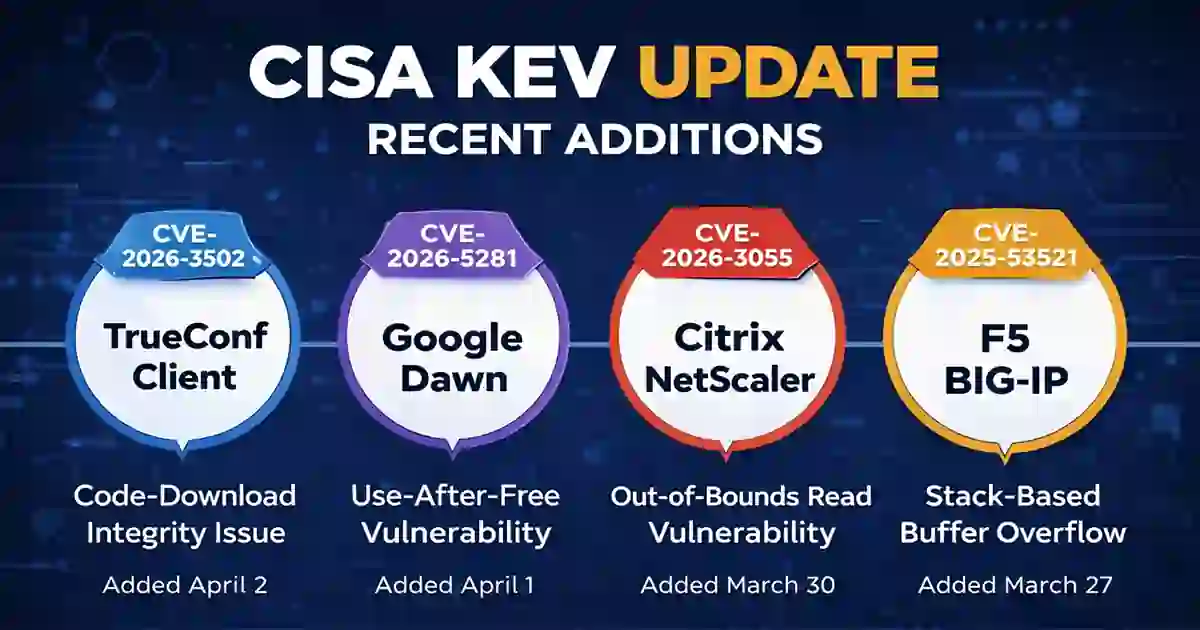
As of April 3, 2026, one of the newest catalog additions is CVE-2026-3502, affecting TrueConf Client. CISA issued an alert on April 2, 2026 saying it had added one new vulnerability to the KEV catalog based on evidence of active exploitation. The KEV catalog lists the flaw as a Download of Code Without Integrity Check vulnerability, and NVD says the client downloads update code and applies it without verification, creating a path for arbitrary code execution if an attacker can influence the update delivery path.
Another recent item is CVE-2026-5281, affecting Google Dawn in Chrome. CISA issued a separate alert on April 1, 2026 for that entry. The KEV catalog identifies it as a Use-After-Free vulnerability, and the catalog notes that it could allow a remote attacker who had already compromised the renderer process to execute arbitrary code through a crafted HTML page.
The catalog also picked up CVE-2026-3055 for Citrix NetScaler ADC and NetScaler Gateway on March 30, 2026. NVD describes the flaw as an out-of-bounds read caused by insufficient input validation when the product is configured as a SAML identity provider, and the NVD record shows CISA’s KEV update with a due date of April 2, 2026.
Recent KEV activity has also included CVE-2025-53521 for F5 BIG-IP. CISA issued an alert on March 27, 2026 saying it had added one new vulnerability to the catalog based on evidence of active exploitation. Together, these entries show a pattern rather than a single isolated issue: collaboration software, browser components, application delivery infrastructure, and perimeter products all entered KEV within a short period.
Why a CISA KEV update matters
A CISA KEV update matters because vulnerability management is usually a prioritization problem, not an awareness problem. Most organizations already know they have patching work to do. The harder task is deciding what should move first when the backlog includes internet-facing systems, user-facing software, vendor advisories, and internal exceptions. KEV helps narrow that decision by focusing on vulnerabilities tied to active exploitation. CISA’s own catalog language supports that use.
The value becomes clearer when asset context is added. A KEV entry affecting a low-value internal system is still important, but a KEV entry affecting a browser engine, gateway, VPN, application delivery product, or identity-related service usually deserves faster attention. That is why it makes sense to connect this article to internal pages such as Ransomware Initial Access in 2026, Microsoft 365 and Entra hardening checklist for 2026, and Data Breach Timeline Template: 9 Critical Response Steps.
In that sense, the KEV catalog is best understood as a triage layer. It does not replace the rest of a patching program, but it improves the order in which work is handled. For teams that need a weekly signal grounded in attacker behavior, that is precisely what makes it useful.
CISA KEV update: 7 patching priorities
1. Review the newest KEV additions first
A practical KEV process usually starts with the newest entries. Recent additions often represent the clearest signal of current attacker interest, and this week’s sequence from TrueConf Client to Google Dawn to Citrix NetScaler is a good example of that pattern.
2. Match the CISA KEV update to the actual asset inventory
A KEV entry becomes urgent only when it intersects with the environment. The most useful first questions are straightforward: do we run the product, where is it deployed, is it exposed, and who owns it. That is where a CISA KEV update becomes operational rather than informational.
3. Prioritize edge and identity-related systems ahead of routine backlog
When a KEV entry affects a public-facing system, remote access technology, browser component, application delivery product, or identity workflow, it often belongs in the first remediation wave. The recent NetScaler and F5 examples show why perimeter and access infrastructure deserve that faster path. Internal support links here include Edge VPN Vulnerabilities to Patch First in 2026 and Passkeys vs MFA vs SMS 2FA.
4. Use KEV with CVSS and exposure, not instead of them
KEV is a strong urgency signal, but it is not the only one that matters. Exposure, business criticality, dependency risk, and remediation feasibility still belong in the decision process. The most balanced approach is to use the CISA KEV update alongside severity scoring and asset context rather than treating it as a standalone answer. KEV vs CVSS Patch Priority: 7 Critical Facts is the most natural internal link for this section.
5. Tie the KEV review to a written patch SLA
A weekly review is only useful if it leads to deadlines and ownership. A written remediation timeline clarifies who patches what, how quickly exceptions are escalated, and when compensating controls are required. That is where Patch Management SLA Template: Critical, High, Medium, Low fits naturally.
6. Treat unresolved KEV items on exposed assets as incident risk
Once a KEV-listed flaw remains unresolved on an exposed system, the issue begins to resemble incident risk rather than ordinary backlog. At that point, monitoring, exposure reduction, and documented exceptions become more important. If exploitation is suspected or the response process needs structure, Data Breach Timeline Template: 9 Critical Response Steps is the strongest internal follow-up.
7. Make the CISA KEV update a standing review
Organizations usually get the most value from KEV when they make it routine. A short recurring review between security, infrastructure, and system owners is often enough. The goal is not to create a separate bureaucracy but to make sure new KEV entries are visible early enough to influence patch order and escalation decisions.

How to use a CISA KEV update in practice
The most effective use of a CISA KEV update is to build it into work that already exists. A straightforward process looks like this: review recent additions, compare them with the asset inventory, identify exposed or high-value systems, apply the vendor fix or mitigation, and track closure against a written SLA. That workflow is why the site’s existing patching and response content makes good supporting reading. In addition to the pages already mentioned, related internal articles include Incident Response Deadlines US UK: 7 Critical Compliance Rules, SEC Cyber Incident Disclosure Checklist, and Cybersecurity News Today | Global Threat Updates & Analysis.
For external references, the strongest practice is to link to primary material rather than commentary. The most useful sources for this post are the CISA Known Exploited Vulnerabilities Catalog, Binding Operational Directive 22-01, NVD detail for CVE-2026-3502, and NVD detail for CVE-2026-3055. That keeps the article close to source material and helps it read like a reference-style explainer rather than a promotional post.
Conclusion
A CISA KEV update is useful because it helps security teams focus on vulnerabilities that have already crossed into active exploitation. This week’s recent catalog activity around TrueConf Client, Google Dawn in Chrome, Citrix NetScaler, and F5 BIG-IP shows why that distinction matters. Vulnerability management improves when remediation order is shaped by evidence of exploitation instead of severity alone.
That is the best way to use the KEV catalog. It is not a full patch strategy by itself, and it cannot replace asset knowledge. It is a prioritization layer. Used that way, it becomes one of the clearest weekly indicators available to defenders.
FAQ
What is a CISA KEV update?
A CISA KEV update is a current view of the newest additions and changes in CISA’s Known Exploited Vulnerabilities catalog, which CISA says organizations should use as an input to vulnerability prioritization.
Why is a CISA KEV update more useful than a long CVE list?
Because it highlights vulnerabilities with evidence of exploitation in the wild, making it more directly useful for short-term patch prioritization.
Which entries are the most relevant this week?
Recent entries include CVE-2026-3502 for TrueConf Client, CVE-2026-5281 for Google Dawn in Chrome, and CVE-2026-3055 for Citrix NetScaler ADC and NetScaler Gateway.
Does KEV only matter for U.S. federal agencies?
BOD 22-01 directly applies to federal civilian agencies, but CISA also says organizations more broadly should use the catalog to inform vulnerability prioritization.
Which internal links fit this topic best?
The strongest fits are KEV vs CVSS Patch Priority, Patch Management SLA Template, Edge VPN Vulnerabilities to Patch First in 2026, Ransomware Initial Access in 2026, and Data Breach Timeline Template.