EU Cyber Resilience Act 2026: 7 Urgent Rules from Sept 11
The EU Cyber Resilience Act 2026 reaches its first real operational milestone on September 11, 2026. From that date, manufacturers must begin reporting actively exploited vulnerabilities and severe incidents affecting the security of covered products with digital elements sold in the European Union. This is not the full start of the whole regime, but it is the first point at which many businesses will feel the law in day-to-day security operations.
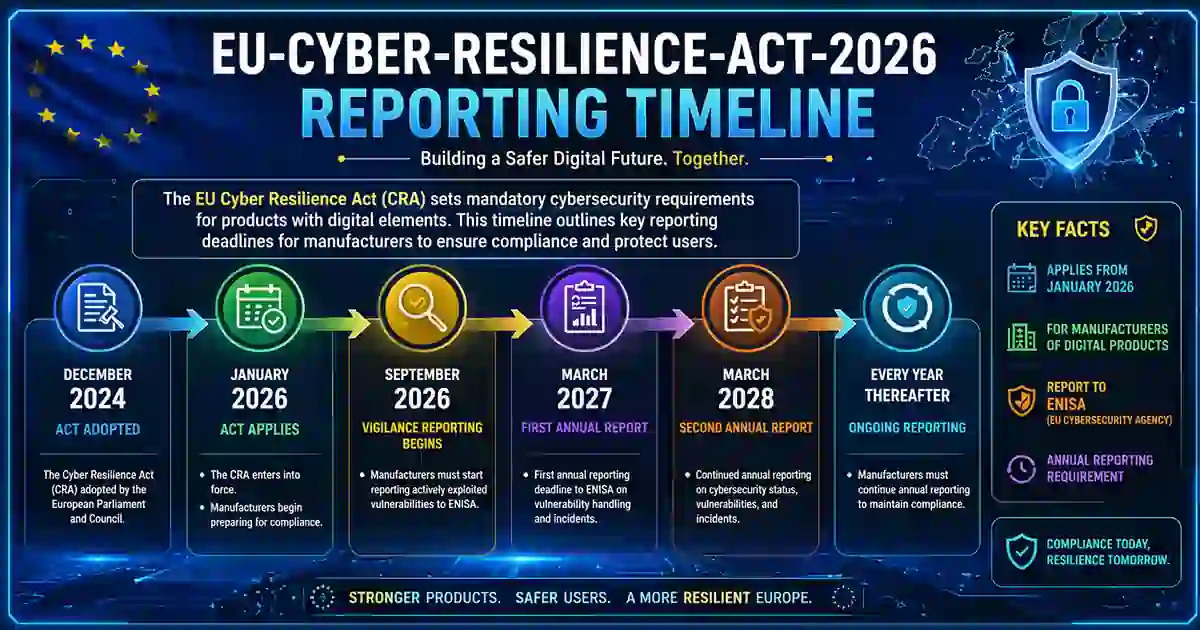
A lot of quick summaries flatten the timeline and make the regulation sound as if everything begins at once. The official position is more precise. The Act entered into force on December 10, 2024. Its main obligations apply from December 11, 2027, while the reporting obligations apply earlier, from September 11, 2026. The Commission’s implementation page also highlights June 11, 2026 as the point when provisions on conformity assessment bodies start to apply, which shows that 2026 is an active rollout year rather than a waiting period.
For readers, the practical meaning of EU Cyber Resilience Act 2026 is simple. This is where the law stops being only a compliance topic and starts becoming an escalation, evidence, and reporting topic. A company may still be building toward the broader 2027 framework, yet by September 2026 it may already need to identify a reportable event, confirm what is known, and notify through the EU process on time.
Table of Contents
Why EU Cyber Resilience Act 2026 matters now
The earliest operational deadline is often more important than the final legal deadline. That is exactly what is happening here. As of September 11, 2026, manufacturers are required to report actively exploited vulnerabilities and severe incidents impacting the security of products with digital elements. That requirement creates real time pressure. It forces product teams, security teams, legal teams, and executives to move from general awareness into a working decision process.
This also helps explain why the CRA sits naturally beside other European cyber rules. The Commission says the Act complements broader EU cybersecurity legislation, which is one reason readers comparing legal regimes may also want to see your related post on NIS2 by Country: 7 Urgent Differences in Europe. For UK comparison, UK Cyber Security and Resilience Bill 2026: 7 Key Changes is a useful companion because it shows how reporting and supplier oversight are evolving on a parallel but different track.
What the law covers
The Cyber Resilience Act is the EU’s product cybersecurity law for products with digital elements. The European Commission describes it as introducing mandatory cybersecurity requirements for hardware and software products placed on the EU market, with obligations that run across the product lifecycle rather than stopping at launch. Products that comply will carry CE marking, while national market surveillance authorities are responsible for enforcement.
That broad lifecycle model is why EU Cyber Resilience Act 2026 matters to more than lawyers. It touches secure development, support periods, vulnerability handling, technical documentation, updates, and post-market responsibilities. The Commission’s implementation materials also make clear that the law is not limited to a narrow consumer-device category. It reaches hardware, software, and related remote data processing solutions, which means the scope can matter to software vendors, embedded-device makers, enterprise technology providers, and industrial suppliers alike.
What starts on September 11 under the EU Cyber Resilience Act 2026
What begins on September 11, 2026 is the mandatory reporting regime under the EU Cyber Resilience Act 2026. The Commission’s reporting page says manufacturers must notify:
- actively exploited vulnerabilities
- severe incidents impacting the security of products with digital elements.
Manufacturers are not expected to file through scattered national routes one by one. They report through the Single Reporting Platform, and ENISA describes that platform as the technical mechanism for CRA reporting in the EU Digital Single Market. ENISA also says the platform is being prepared through 2025 and 2026 to support reporting from September 11, 2026 onward.
That detail matters because it turns the deadline into a process question. A company that has not decided who owns technical triage, who confirms active exploitation, and who approves regulator-facing notification is not just late on administration. It is late on governance. That is the operational implication of the reporting model the Commission and ENISA have described.
The reporting timeline in plain English
The deadlines are short enough to expose weak internal coordination very quickly.
The Commission says manufacturers must submit an early warning within 24 hours of becoming aware of an actively exploited vulnerability or severe incident. A fuller notification is due within 72 hours. A final report must then be filed within 14 days after a corrective measure is available for actively exploited vulnerabilities, and within one month for severe incidents.
On paper, that looks clear. In practice, the difficult part is rarely the form itself. The harder part is deciding what is known, what is still unverified, which product versions are affected, whether a supplier component is involved, and whether the issue meets the reporting threshold. That is why EU Cyber Resilience Act 2026 belongs as much to product security and incident response as it does to legal compliance.
This is also the most natural place to add internal links that help the reader continue the same story. If the problem is supplier visibility, readers can move to Third-Party Risk Assessment Checklist 2026: 12 Proven Steps. If the issue is contractual control, Supplier Cybersecurity Contract Template: 7 Best Tips fits well. If the weakness is remediation speed, 7 Important Patch Management SLA Template Rules extends the discussion into ownership, timelines, and evidence. If the reader is thinking about response sequence more broadly, Data Breach Timeline Template: 9 Critical Response Steps is also a relevant next read.
Which products are likely to be affected
The safest reading is broad. The Commission’s public materials describe the law as applying to products with digital elements, including hardware and software products and related remote data processing solutions. That means businesses should look carefully at anything they place on the EU market that relies on software, network connectivity, embedded computing, or digital service functionality tied to the product.
Another detail that many thin summaries miss is timing. The Commission’s summary says reporting obligations under Article 14 apply from September 11, 2026, while the broader main provisions apply from December 11, 2027. In practical terms, that means organizations with products already present in the market should not assume that all meaningful work can wait until the later date.
Why this matters before December 2027
It is tempting to treat December 11, 2027 as the only date that matters. The official rollout suggests otherwise. The Commission’s implementation page lists the June 2026 conformity-body milestone, Q3 2026 standardisation deliverables, the September 11, 2026 entry into application of reporting obligations, and the December 2027 full application date as distinct steps. That timeline shows a staged build-out rather than a single cliff-edge moment.
The Commission also published draft guidance in March 2026 to help companies apply the Act, especially around scope, remote data processing solutions, support periods, and overlap with other EU legislation. That is another sign that EU Cyber Resilience Act 2026 is already in the implementation phase, not the distant-future phase.
For readers, this is where a more neutral, encyclopedia-style linking pattern helps. When you mention the official framework, link directly to the European Commission’s CRA overview, the CRA reporting obligations page, the implementation timeline, and ENISA’s Single Reporting Platform page. In WordPress, leave these as normal outbound links so they remain standard dofollow links rather than nofollow.
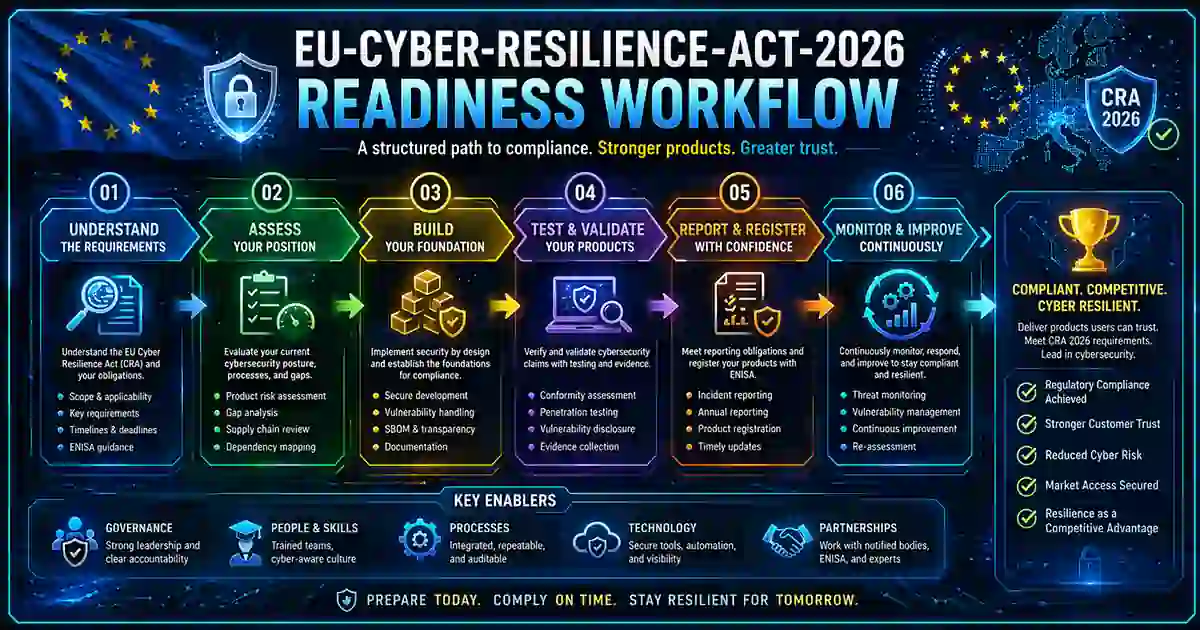
What companies should do now
A strong response to EU Cyber Resilience Act 2026 starts with product visibility. Teams should know which products with digital elements they sell into the EU, which versions are live, which components come from third parties, and which remote services are part of normal operation. Without that, even basic scope and reporting decisions become slower and less reliable.
The second requirement is ownership. Someone needs to lead technical triage. Someone needs to review legal thresholds. Someone needs the authority to approve notification. Under EU Cyber Resilience Act 2026, the reporting clock is short enough that uncertainty over internal ownership can become a material compliance problem in its own right. That point is not stated as a slogan in the law, but it follows directly from the 24-hour and 72-hour deadlines.
The third requirement is evidence flow. In the first one to three days of a serious issue, teams may need fast answers on exploitation status, affected versions, product impact, corrective measures, and supplier involvement. That is why the best internal links in this article are the ones that extend the same reader journey instead of changing the subject. Third-Party Risk Assessment Checklist 2026: 12 Proven Steps, Supplier Cybersecurity Contract Template: 7 Best Tips, 7 Important Patch Management SLA Template Rules, and Data Breach Timeline Template: 9 Critical Response Steps all support that same progression from discovery to evidence to reporting.
Final takeaway
The clearest way to explain EU Cyber Resilience Act 2026 is this: September 11, 2026 is the start of mandatory reporting, while December 11, 2027 is the broader full-application date. That split is consistent across the European Commission’s CRA overview, reporting page, summary page, and implementation timeline, and ENISA’s platform planning is aligned to the same September 2026 milestone.
For readers, that means September is the first date that turns the law into a live operational issue. For companies, it means the real challenge is not only reading the regulation. It is building a process that can identify a reportable event, collect the facts quickly, and move without confusion when the clock starts. That is where practical readiness begins under EU Cyber Resilience Act 2026.