CIRCIA Final Rule 2026: 7 Urgent Steps for US Infrastructure
The most useful way to read CIRCIA Final Rule 2026 is not as a live reporting regime, but as a narrowing preparation window. CISA says CIRCIA’s regulatory reporting requirements are not yet effective and will not take effect until the final rule does. At the same time, the statute and the 2024 proposed rule are already clear enough to show the shape of what is coming: covered cyber incident reporting, ransom payment reporting, and short reporting clocks that will force security, legal, and executive teams to work faster than many organizations do today.
That is why this topic matters now. In February 2026, CISA announced another round of sector-specific and general town hall meetings to refine the scope and burden of the proposed rule. Those sessions covered March 9 through April 2, 2026, and the agency said it wanted practical input on applicability, examples of substantial cyber incidents, report content, RFIs, subpoenas, and harmonization with other reporting obligations. In other words, the broad direction is visible, while some operational details are still being sharpened.

Table of Contents
What CIRCIA Final Rule 2026 means right now
CIRCIA sits inside a broader national critical-infrastructure framework. CISA identifies 16 critical infrastructure sectors, and the proposed CIRCIA rule is aimed at “covered entities” within that ecosystem rather than at every business in the country. That is why the first question is scope, not style: if your organization operates in or supports one of those sectors, you should assume this rule deserves serious attention even before the final text is published.
For internal linking, the most natural early references on CybersecurityTime are CIRCIA Rulemaking Tracker 2026 and CIRCIA 72-Hour Reporting Rule. They fit here because one covers the rulemaking timeline and the other explains the proposed reporting clocks in practical terms.
1. Decide whether you are likely to be covered
One of the easiest mistakes is assuming that the final rule will probably apply only to someone else. CISA’s February 2026 town hall notice makes clear that the agency was still seeking input on size-based criteria, sector-based criteria, and whether other lists or categories of entities should be included as covered entities. That means exact boundaries may still move, but it does not mean organizations should wait for perfect certainty before reviewing whether they are likely to fall into scope.
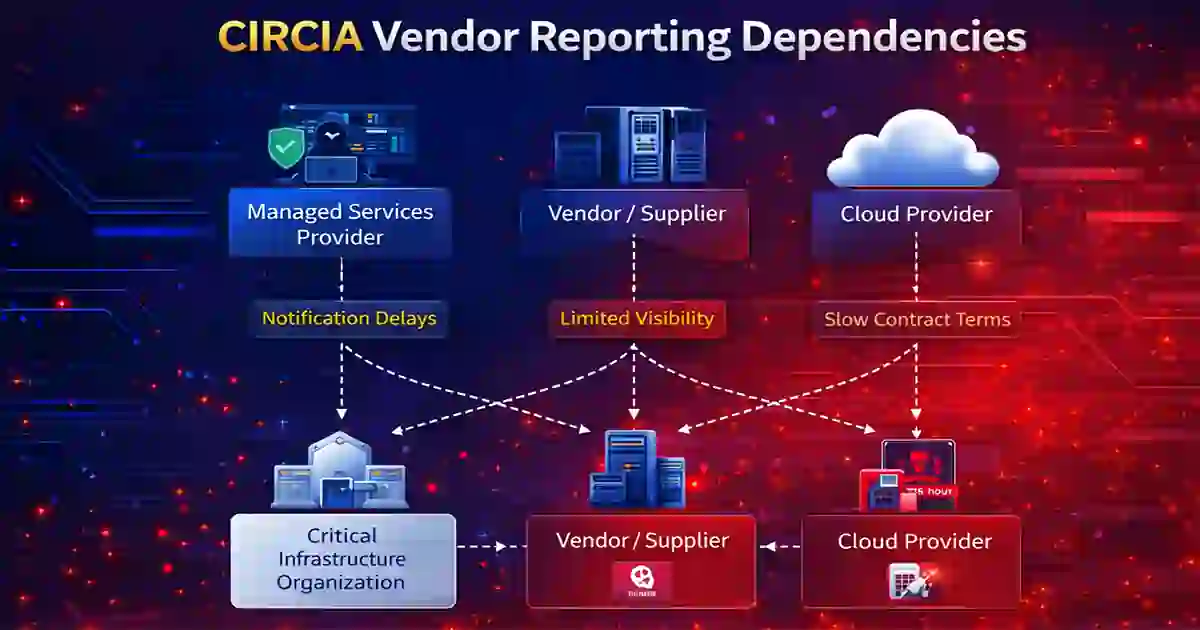
A sensible coverage review should include subsidiaries, major business lines, cloud dependencies, managed service relationships, and other suppliers whose delayed visibility could affect your own reporting timeline. This is where Vendor Security Questionnaire Template and Supplier Cybersecurity Contract Template fit naturally as internal links, because vendor reporting speed and contract language can become compliance issues very quickly once a short federal clock starts running.
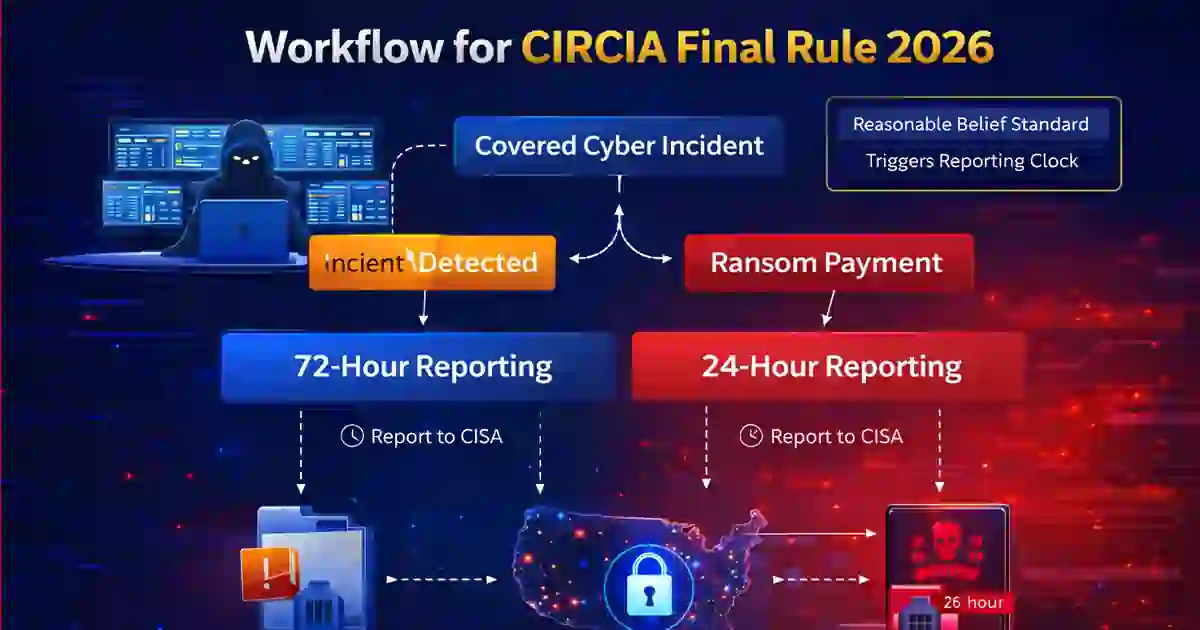
2. Rebuild escalation around the 72-hour and 24-hour clocks
The core reporting model is already visible in official materials. The statute and CISA’s public CIRCIA materials are built around reporting a covered cyber incident within 72 hours after the entity reasonably believes the incident occurred, and reporting a ransom payment within 24 hours after payment. Those windows are short enough that organizations with slow detection, slow classification, or slow legal escalation will lose time before they even begin drafting a report.
This is why CIRCIA Final Rule 2026 is not just a legal topic. It is also a detection and response topic. If your security team needs too long to decide whether an event is serious, or if legal only enters the process after technical teams believe they have “enough facts,” the reporting clock becomes much harder to manage. That makes Reduce Detection Time Regulatory Deadlines Risk and Mean Time to Detect: 5 Proven Ways to Reduce Cyber Risk strong internal links in this section.
3. Build a report-ready evidence package
The proposed rule is not designed for vague, one-line notifications. CISA’s NPRM materials describe reporting requirements, deadlines, report content, exceptions, and third-party reporting procedures. That tells you something important: by the time a report is filed, the organization needs more than a headline. It needs a working record of what happened, what was affected, what is still unknown, and who is responsible for the next update.
A practical evidence package should include a timeline, affected systems or services, operational impact, third-party involvement, known attacker behavior, ransom facts if relevant, and a record of who made the key decisions. That recommendation is operational judgment, but it follows directly from the structure of the NPRM. On your site, Cybersecurity Incident Response Timeline and Data Breach Timeline Template are the cleanest internal links here because they extend the story from regulatory readiness into documented response.
4. Clarify who decides when an incident becomes reportable
Short deadlines are manageable only when decision ownership is clear. Under the proposed model, the 72-hour incident clock is tied to when the entity reasonably believes a covered cyber incident has occurred. That means many organizations will need a tighter handoff between security operations, legal, compliance, communications, and executive leadership than they use today. Waiting for complete certainty may feel cautious, but it can also waste the very time the rule is designed to preserve.
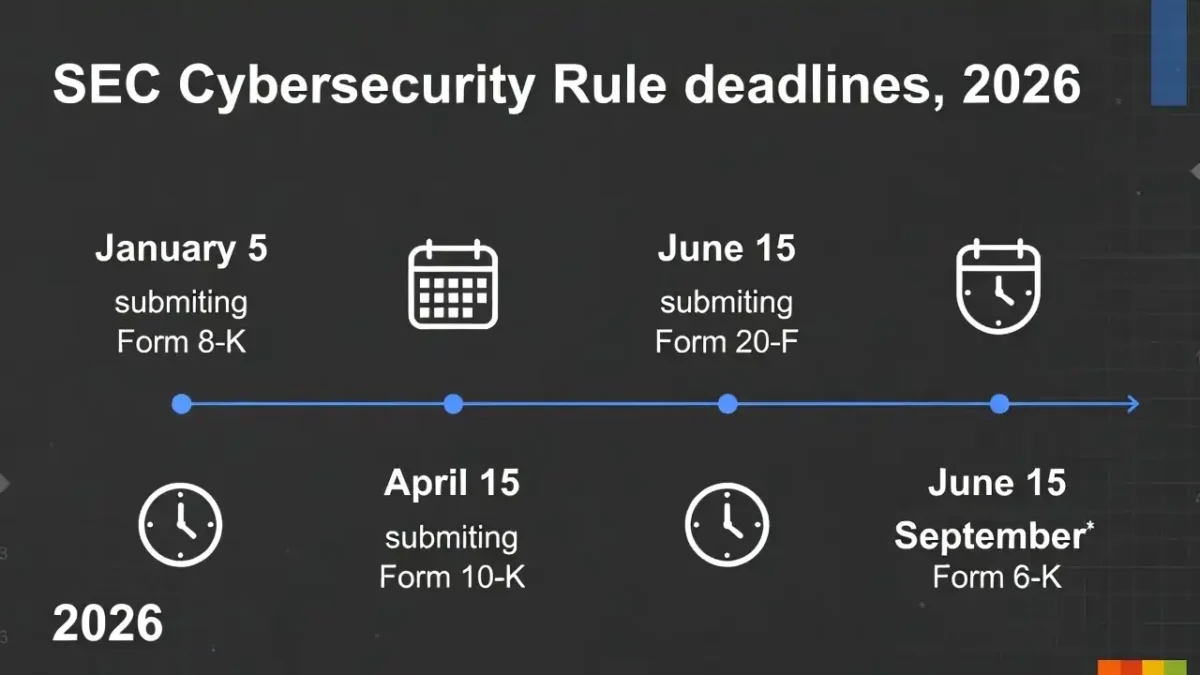
This is also where your internal SEC Cyber Incident Disclosure Checklist and SEC Cyber Rule Timeline 2026 become useful. They are not CIRCIA articles, but they help readers think in the right way about material facts, early escalation, and the cost of waiting too long for perfect clarity.
5. Plan for overlap with other reporting obligations
CIRCIA will not operate in a vacuum. In its 2026 town hall notice, CISA explicitly asked for input on harmonizing CIRCIA with other federal, state, local, tribal, and territorial reporting requirements and on reducing duplication or conflict. That is a strong sign that the agency expects overlapping obligations to remain part of the real-world compliance picture.
For public companies, that may mean alignment with SEC incident-disclosure workflows. For other organizations, it may mean sector-specific obligations, contract-driven reporting, or other regulatory timelines. The best practical answer is not to assume one rule will cancel the others. It is to create one internal decision process that can support several outward reporting lanes. This is where Incident Response Deadlines US UK is also a useful supporting link on your site.
6. Tighten vendor and third-party notification paths
Some of the most important parts of the 2026 town hall agenda were not about headline deadlines at all. CISA specifically asked for feedback on managed service providers, cloud service providers, open-source software, and other applicability questions that affect how incidents are discovered and reported across interconnected environments. That matters because a company cannot report quickly if the relevant facts are trapped inside a supplier relationship or buried in a service contract that never set reporting expectations clearly enough.
That is why internal links such as Vendor Security Questionnaire Template and Supplier Cybersecurity Contract Template belong in this article. They make the point concrete: regulatory readiness is partly a third-party governance problem, not only an internal SOC problem.
7. Run a reporting tabletop before the rule takes effect
The best remaining use of time is rehearsal. CISA’s public guidance says the rule is not yet effective, while the town hall notice shows the agency is still refining implementation details. That combination gives organizations a rare chance to fix ownership, workflow, and evidence gaps before the first mandatory filing is due.
A good tabletop for CIRCIA Final Rule 2026 does not need to be elaborate. It should test who identifies a potentially covered incident, who starts the internal clock, how legal is engaged, how executives are briefed, what evidence is assembled in the first few hours, and how external dependencies are handled. If a team cannot answer those questions clearly in an exercise, it probably will not answer them cleanly during a real incident. SOC Efficiency Metrics 2026 is also a natural internal link here because the reporting challenge is inseparable from operational speed.
Final take
The right tone for CIRCIA Final Rule 2026 is neither panic nor delay. CISA says the reporting requirement is not yet effective, but the statute, the proposed rule, and the 2026 town halls already show enough for organizations to start preparing seriously. The broad obligations are visible, the deadlines are short, and the remaining uncertainty is exactly the reason to fix process problems now rather than later.
For most teams, the next steps are practical: determine likely coverage, shorten detection-to-escalation time, build a report-ready evidence package, clarify decision ownership, map overlapping obligations, tighten vendor notification terms, and rehearse the workflow before the rule becomes effective. The strongest internal follow-ons on CybersecurityTime are CIRCIA Rulemaking Tracker 2026, CIRCIA 72-Hour Reporting Rule, Reduce Detection Time Regulatory Deadlines Risk, Vendor Security Questionnaire Template, SEC Cyber Incident Disclosure Checklist, Cybersecurity Incident Response Timeline, and Data Breach Timeline Template.