CISA KEV This Month: 3 Dangerous CVEs to Patch Now
When a vulnerability appears in CISA’s Known Exploited Vulnerabilities Catalog, the discussion changes immediately. At that point, defenders are no longer looking at a bug that might matter someday. They are looking at a vulnerability that has already crossed into real-world exploitation. Under Binding Operational Directive 22-01, KEV entries are not just informational for federal civilian agencies; they are tied to remediation expectations. For private-sector teams, the catalog has become one of the clearest public signals for patch prioritization.
As of April 2026, the most notable additions in CISA KEV This Month are CVE-2026-5281 in Google Chrome, CVE-2026-3502 in TrueConf Client, and CVE-2026-35616 in Fortinet FortiClient EMS. CISA added those KEV entries on April 1, April 2, and April 6 respectively, which makes this month’s list short but still operationally important. Each one represents a different kind of risk: browser compromise, management-plane exposure, and software-update trust failure.

Table of Contents
Why CISA KEV This Month matters
The value of CISA KEV This Month is that it helps defenders separate urgency from volume. A high CVSS score can show that a flaw is severe, but it does not show whether attackers are already exploiting it. KEV answers that second question directly. That is why KEV vs CVSS Patch Priority is useful related reading here: severity and active exploitation are connected, but they are not the same thing, and mature patch programs handle them differently.
In practice, CISA KEV This Month is most useful when it is tied to a real workflow. A KEV entry should trigger asset identification, exposure validation, remediation ownership, and fixed-version verification. Readers looking to extend that process into day-to-day operations may also find Patch Management SLA Template and How to Reduce Cybersecurity Detection Time helpful. Together, they carry the discussion from prioritization into execution.
CVE-2026-5281: Chrome browser risk with broad exposure
The most broadly exposed entry in CISA KEV This Month is CVE-2026-5281. Google’s Stable Channel Update for Desktop on March 31, 2026 updated Chrome to 146.0.7680.177/178 for Windows and Mac, and the related NVD entry for CVE-2026-5281 says the flaw is a use-after-free in Dawn in Google Chrome prior to 146.0.7680.178 that could allow arbitrary code execution after renderer compromise via a crafted HTML page. CISA added it to KEV on April 1.
This entry ranks high because browser exploitation scales quickly. Browsers process untrusted content all day, across large endpoint fleets, and a confirmed browser vulnerability can create defensive urgency far beyond the original technical details of the bug. Readers looking at browser exposure in a broader security context may also find Public-Facing Application Security Checklist and Okta Security Checklist useful, especially where web exposure and identity controls intersect.
The response here is straightforward: update Chrome to the fixed build, make sure users actually restart the browser, and verify version compliance across managed endpoints. A confirmed exploited browser flaw is not the kind of issue that belongs in a routine monthly queue. It is exactly the sort of vulnerability that CISA KEV This Month is designed to bring forward.

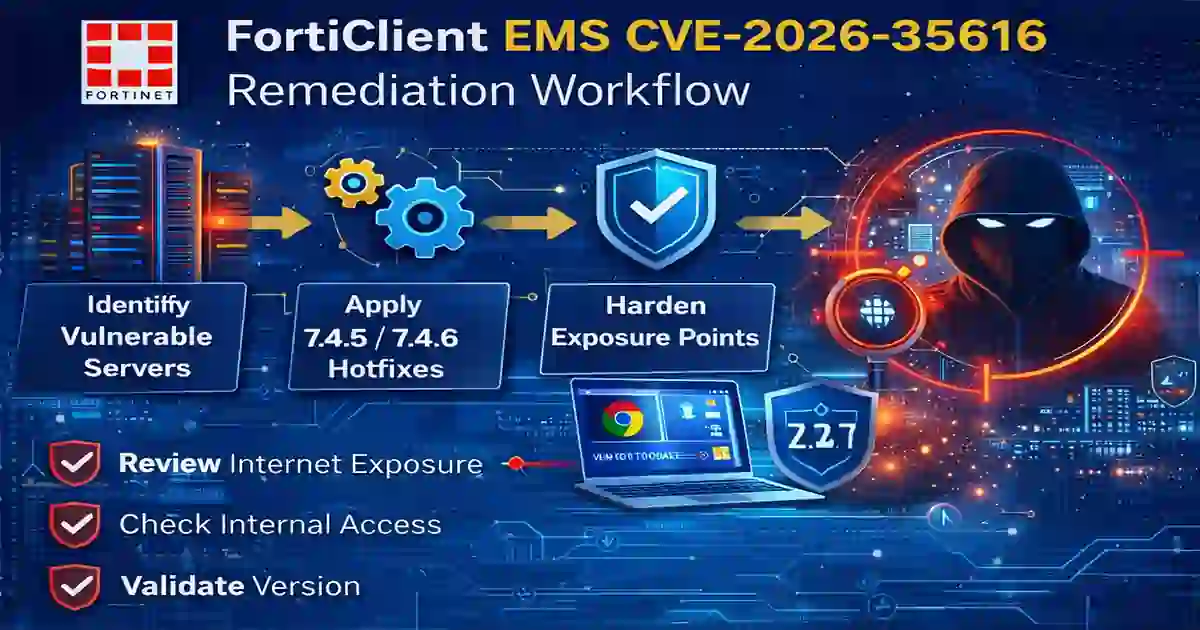
CVE-2026-35616: Fortinet FortiClient EMS and management-plane risk
The most operationally dangerous management-platform entry in CISA KEV This Month is CVE-2026-35616 in Fortinet FortiClient EMS. Fortinet’s PSIRT advisory FG-IR-26-099 says the flaw is an improper access control issue in the API component, affects FortiClient EMS 7.4.5 through 7.4.6, may allow an unauthenticated attacker to execute unauthorized code or commands via crafted requests, and carries a CVSS v3 score of 9.1. Fortinet also says it has observed exploitation in the wild and urges customers to apply the hotfixes, with 7.4.7 also including the fix. CISA added it to KEV on April 6.
This is the sort of vulnerability that deserves immediate attention because endpoint-management infrastructure creates outsized downstream risk. A browser vulnerability may offer attackers scale. A management-plane vulnerability may offer them control. For organizations measuring the business impact of this kind of exposure, Board-Level Cybersecurity Metrics Guide and How to Reduce Cybersecurity Detection Time provide useful follow-on reading.
If your organization runs FortiClient EMS, this belongs at the front of the change queue, especially if the server is internet-facing or reachable from lower-trust segments. This is one of the clearest examples of why CISA KEV This Month is useful: it turns a vendor advisory into an immediate prioritization signal for defenders who need to act before the next routine patch window.
CVE-2026-3502: TrueConf Client and update-integrity risk
The third major entry in CISA KEV This Month is CVE-2026-3502 in TrueConf Client. The NVD entry for CVE-2026-3502 says the client downloads application update code and applies it without performing verification. An attacker who can influence the update-delivery path could substitute a tampered payload, which may lead to arbitrary code execution in the context of the updating process or user. CISA added the issue to KEV on April 2.
This one ranks below the Chrome and Fortinet entries mainly because the exploitation path appears narrower, not because it is harmless. Update-integrity failures matter because they attack one of the assumptions defenders rely on most: that software updates are trustworthy by default. This also connects well with Secure by Design Checklist Vendors and Vendor Security Questionnaire Template, particularly for teams reviewing software trust, supplier assurance, and update security.
If your environment uses TrueConf Client, update it quickly and review how updates are delivered internally. Proxies, TLS inspection, cached packages, and software-distribution controls can all affect the trust path. In that sense, CISA KEV This Month is useful not only because it identifies a product to patch, but because it highlights a risk pattern many teams underestimate until it becomes urgent.
How to patch CISA KEV This Month in the right order
For most organizations, the best operational sequence is simple. Patch FortiClient EMS first if it is present, because it is a management-plane issue with active exploitation and potentially outsized impact. Patch Chrome immediately across endpoints because browser exposure is broad and attacker relevance is already established. Then patch TrueConf Client and review the integrity of the update path around it. That is not an official CISA-issued ranking, but it is a practical order based on exposure and likely business risk.
A mature workflow does not stop at “patch available.” It checks where the vulnerable software exists, whether it is externally reachable, whether compensating controls reduce the exposure, and whether the corrected version is actually running in production. Readers who want to go beyond prioritization can continue with CISA KEV Update, Patch Management SLA Template, and [Data Breach Timeline Template] for more detail on remediation tracking and incident response.
Final take
CISA KEV This Month is still a short list, but it already captures three distinct risk patterns: a browser flaw with broad endpoint reach, a management-system flaw with outsized enterprise consequences, and an update-integrity weakness that undermines trust in software delivery. That mix is exactly why the KEV catalog matters. It helps security teams spend scarce patching time where real attackers are already active instead of spreading the same effort evenly across a much larger backlog.
For readers who want to explore the next steps, helpful related reading includes KEV vs CVSS Patch Priority, Patch Management SLA Template, How to Reduce Cybersecurity Detection Time, Secure by Design Checklist Vendors, and Data Breach Timeline Template.. Together, these topics extend the discussion from vulnerability prioritization into patch execution, vendor assurance, and incident handling.