CIRCIA Rulemaking Tracker 2026: 9 Critical Delays and Key Updates
CIRCIA Rulemaking Tracker 2026 remains one of the most closely watched cybersecurity compliance topics for U.S. critical infrastructure organizations. The reason CIRCIA Rulemaking Tracker 2026 continues to matter is straightforward: the proposed rule is already public, but the final rule is still pending, leaving security, legal, and compliance teams to prepare for a framework that is visible in outline but not yet fully settled.
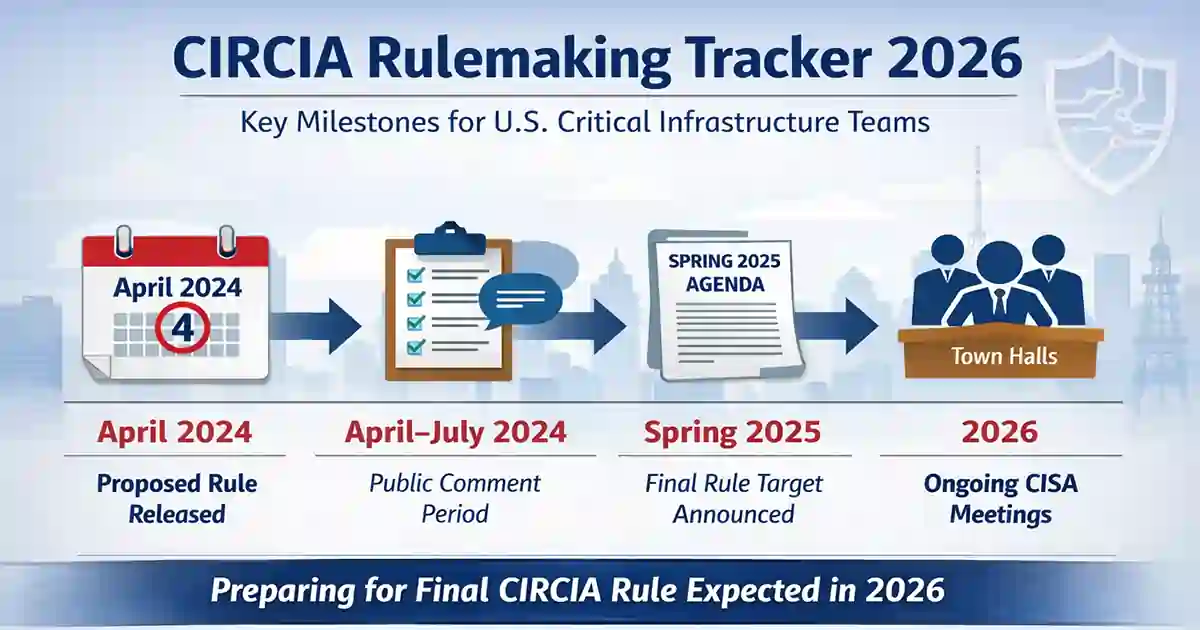
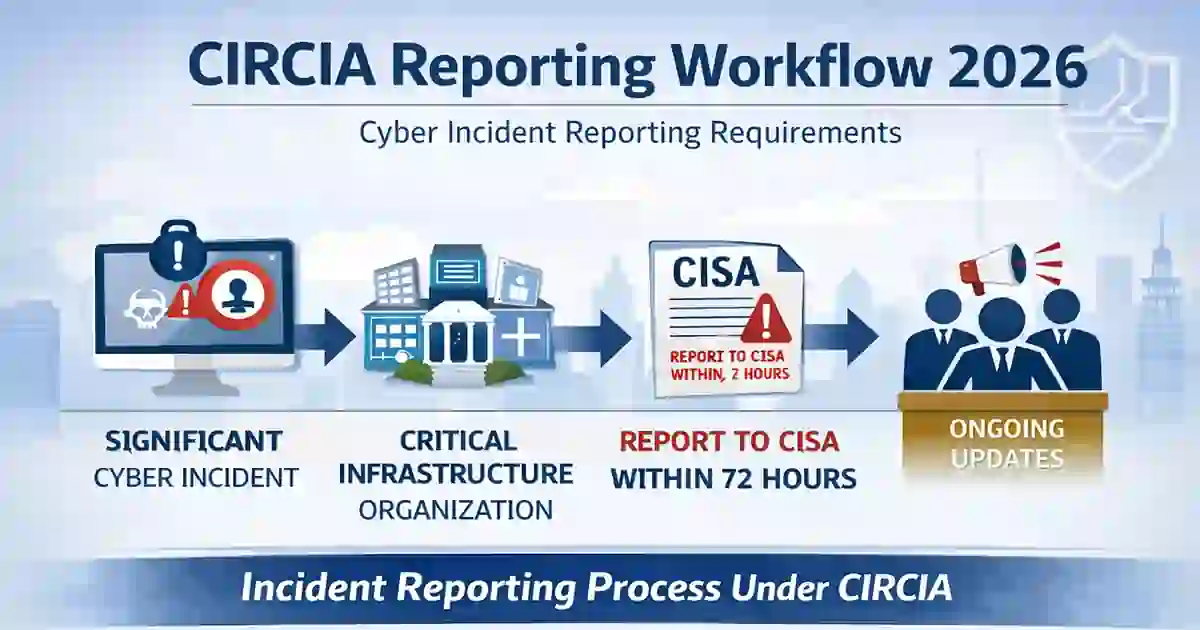
CISA published the proposed rule for the Cyber Incident Reporting for Critical Infrastructure Act on April 4, 2024. That proposal described a reporting model under which covered cyber incidents would be reported within 72 hours and ransom payments within 24 hours once the final rule becomes effective. In practice, CIRCIA Rulemaking Tracker 2026 is not just about dates on a calendar. It is about how regulated organizations should interpret the delay, monitor the final stage of the process, and prepare internal reporting workflows before the rule becomes enforceable. (federalregister.gov)
Table of Contents
What CIRCIA Rulemaking Tracker 2026 Covers
At its core, CIRCIA Rulemaking Tracker 2026 is a status guide to CISA’s rulemaking process for implementing cyber incident and ransom payment reporting obligations under the Cyber Incident Reporting for Critical Infrastructure Act. The law established the reporting framework, but Congress left the operational details to CISA through formal rulemaking. That is why the proposed rule matters so much. It is the document that turns broad statutory language into a real compliance model. (federalregister.gov)
Under the proposed rule, covered entities would report covered cyber incidents within 72 hours after reasonably believing that such an incident occurred, while ransom payments would be reportable within 24 hours after payment is made. The proposal also contemplates supplemental reports as additional information becomes available. Those are short reporting windows, which is why CIRCIA Rulemaking Tracker 2026 matters to operations teams as much as to lawyers and policy staff. (federalregister.gov)
A good internal link in this section is CIRCIA 72-Hour Reporting Rule because it gives readers a practical breakdown of the proposed reporting timelines and their effect on incident response. (cybersecuritytime.com)
Why CIRCIA Rulemaking Tracker 2026 Still Matters
The importance of CIRCIA Rulemaking Tracker 2026 comes from the fact that the rulemaking process did not end with publication of the proposed rule. In February 2026, CISA announced additional town hall meetings and described them as an opportunity for stakeholders to provide feedback on clarifying the proposal and reducing implementation burden. That indicates the rule was still being actively refined rather than simply waiting in line for publication. (federalregister.gov)
For organizations that may fall within scope, CIRCIA Rulemaking Tracker 2026 is useful because it highlights the parts of the rule most likely to affect planning: covered-entity scope, incident thresholds, reporting timelines, supplemental reports, and burden-reduction measures. A delayed final rule does not make the issue less important. It only extends the period during which companies must prepare without having every implementation detail settled. (federalregister.gov)
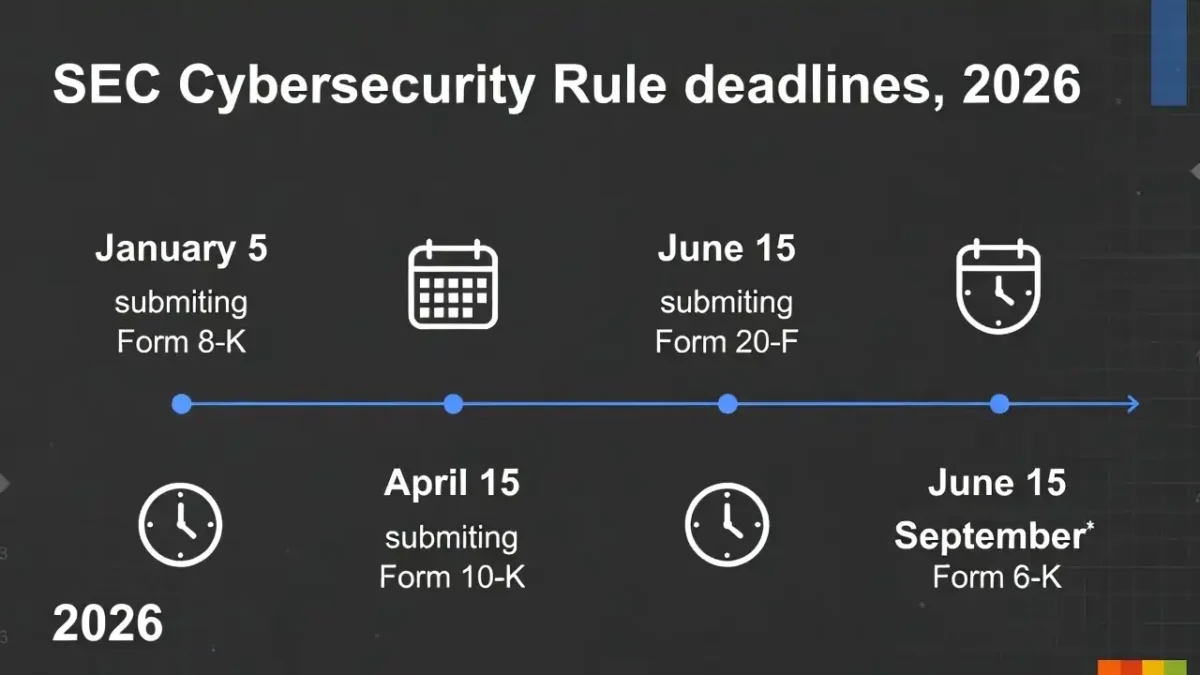
This is also a natural place to link to SEC Cyber Rule Timeline 2026 and SEC Cyber Incident Disclosure Checklist, since readers tracking CIRCIA are often comparing it with other disclosure and reporting obligations. (cybersecuritytime.com)
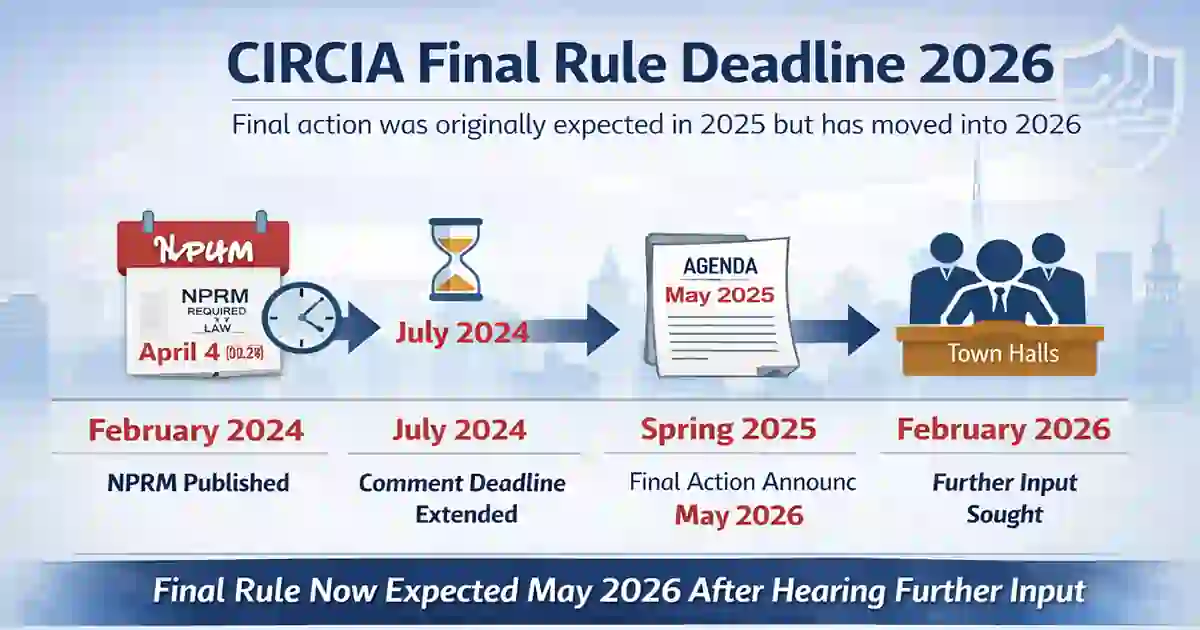
Timeline and Delay in Finalization
The public timeline is relatively clear. CISA published the NPRM on April 4, 2024. The agency later extended the public comment period to July 3, 2024. In the Spring 2025 Unified Agenda, the rule’s regulatory entry listed May 2026 as the target date for final action. Then, in February 2026, CISA announced another round of town halls to gather more stakeholder input. Taken together, those steps show why CIRCIA Rulemaking Tracker 2026 remains relevant: the process advanced substantially, but finalization moved beyond the timetable many observers originally expected. (federalregister.gov)
The delay is significant because the proposed rule itself noted that CIRCIA required an NPRM by March 15, 2024 and a final rule within 18 months of NPRM publication. Because the NPRM appeared in April 2024, many compliance teams assumed the final rule would arrive by late 2025. That did not happen. In practical terms, CIRCIA Rulemaking Tracker 2026 now functions as a planning tool for organizations that need to stay ready during a longer transition period. (federalregister.gov)
For a simple background explainer on the federal process, you can add one external link to Wikipedia’s article on notice of proposed rulemaking.
Nine Developments to Watch
A practical CIRCIA Rulemaking Tracker 2026 should focus on developments that can change real-world preparation.
The first is the publication date of the final rule. The best public signal remains the Spring 2025 agenda entry pointing to May 2026, but that is still a target, not a final published rule. (reginfo.gov)
The second is covered-entity scope. Final wording will determine how broadly the rule reaches across owners, operators, vendors, and service providers that support critical infrastructure.
The third is the threshold for a covered cyber incident. This is where legal text meets the reality of incident response, especially when facts are still developing.
Why CIRCIA Rulemaking Tracker 2026 Is Also an Operations Issue
This part often gets overlooked. CIRCIA Rulemaking Tracker 2026 is not only a policy issue or a legal issue. It is also an operations issue. Short reporting deadlines are much easier to meet when an organization detects incidents early, classifies them quickly, and preserves the right evidence before internal confusion slows the process down.
That is why internal links to Mean Time to Detect, Mean Time to Contain (MTTC), Average Ransomware Containment Time 2026, and Board-Level Cybersecurity Metrics Guide feel natural here rather than inserted only for SEO. (cybersecuritytime.com)
The fourth issue is ransom payment reporting. The proposed 24-hour deadline is demanding because ransom decisions often involve executives, outside counsel, insurers, and incident-response vendors. (federalregister.gov)
The fifth is supplemental reporting. Initial reporting is only one part of the burden. As facts develop, organizations may need to provide additional updates, which makes documentation quality important from the beginning of the incident. (federalregister.gov)
The sixth is burden reduction. CISA’s 2026 town hall notice explicitly invited feedback on reducing implementation burden while preserving useful visibility into major cyber threats. (federalregister.gov)
The seventh is overlap with other reporting regimes. Many organizations will evaluate CIRCIA alongside SEC disclosure duties, customer notice terms, cyber insurance requirements, and sector-specific obligations. That is why internal links to Incident Response Deadlines US UK and SEC Cyber Rule Timeline 2026 fit naturally in the article. (cybersecuritytime.com)
What Organizations Should Do Now
Organizations that expect they may fall within the final rule’s scope should use CIRCIA Rulemaking Tracker 2026 as a planning guide, not just as a status update. They can identify which business units touch critical infrastructure functions, decide who has authority to determine whether an incident may be reportable, and make sure evidence preservation starts early enough to support any later reporting. Those are low-regret steps because they follow directly from the short deadlines described in the proposal. (federalregister.gov)
This is the best place to add your more operational internal links, including Ransomware Detection Timeline, Third-Party Risk Assessment Checklist 2026, and Vendor Security Questionnaire Template. These links support the article’s practical point that reporting readiness begins before disclosure, in detection, vendor visibility, escalation, and incident classification. (cybersecuritytime.com)
How CIRCIA Fits With Other Reporting Rules
CIRCIA Rulemaking Tracker 2026 should not be viewed in isolation. A serious cyber incident may create parallel questions under securities disclosure rules, vendor contracts, cyber insurance policies, privacy obligations, or sector-specific regimes. CISA’s continuing attention to burden and implementation reflects the practical reality that organizations are not navigating a single clean reporting lane. (federalregister.gov)
That broader context is why the article works best when it stays measured. The public record already shows a significant federal rulemaking process, a delayed finalization path, and continuing agency efforts to refine the final product. That is enough to justify close attention and early preparation.
Final Takeaway
The clearest reading of CIRCIA Rulemaking Tracker 2026 is that the reporting framework is advanced, but not yet final. The proposed rule has been public since April 2024. The original expected path to finalization slipped beyond late 2025. CISA continued the process in 2026 through town halls focused on scope and burden, while the public regulatory agenda pointed to May 2026 for final action. Those are the facts that matter most. (federalregister.gov)
For critical infrastructure teams, the practical lesson is simple: preparation should continue even while the last procedural step is pending. That is exactly why CIRCIA Rulemaking Tracker 2026 remains useful.
FAQ
What is CIRCIA Rulemaking Tracker 2026?
CIRCIA Rulemaking Tracker 2026 is a current-status overview of CISA’s rulemaking process to implement cyber incident and ransom payment reporting under the Cyber Incident Reporting for Critical Infrastructure Act. (federalregister.gov)
Has the final CIRCIA rule been published?
Based on the 2026 town hall notice and the public regulatory agenda entry pointing to May 2026, the final rule had not yet been published in the sources reviewed here. (federalregister.gov)
Why are the 2026 town halls important?
They show that CISA was still seeking stakeholder input on how to clarify the proposal and reduce implementation burden, which indicates that final implementation details were still under active consideration in 2026. (federalregister.gov)
What should organizations do before the rule is final?
A practical approach is to prepare internal decision paths, evidence-retention practices, escalation rules, and incident classification workflows in advance. That recommendation follows from the short reporting timelines described in the proposed rule. (federalregister.gov)