UK Incident Reporting Rules Explained: NIS, ICO, and the New Bill
UK incident reporting rules sit at the point where cybersecurity, privacy law, and operational resilience meet. In the United Kingdom, there is no single rulebook that covers every cyber incident. Different duties can arise under the Network and Information Systems Regulations 2018, the Information Commissioner’s Office breach reporting regime, sector-specific communications rules, and the proposed Cyber Security and Resilience Bill. As of 26 March 2026, that bill remained active in Parliament rather than being fully in force.
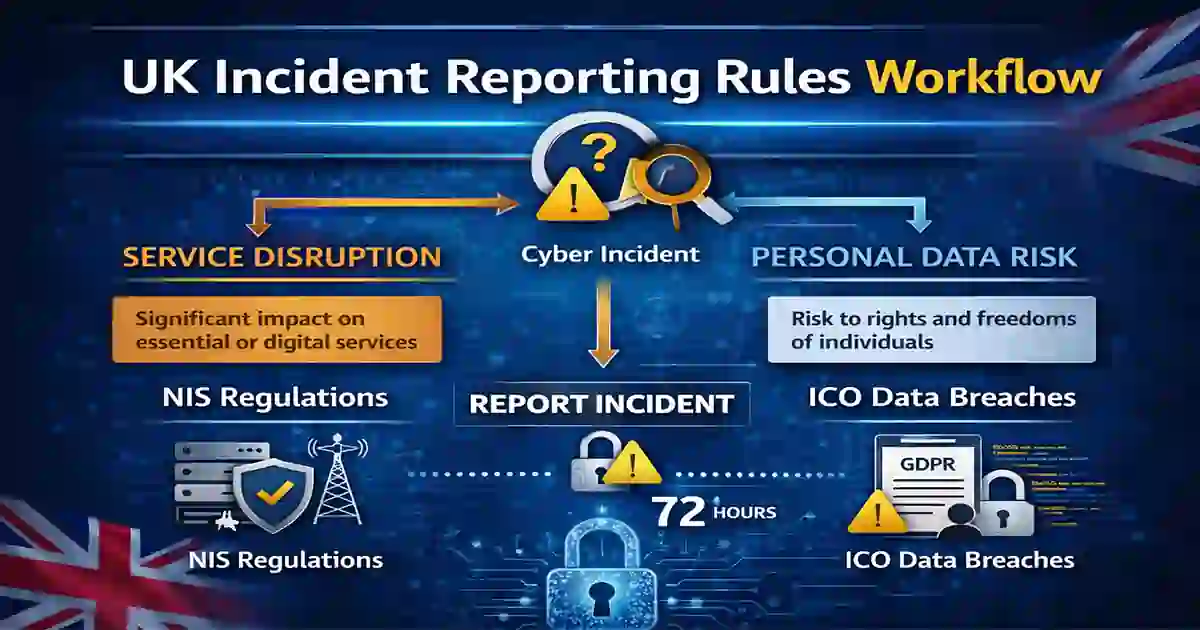
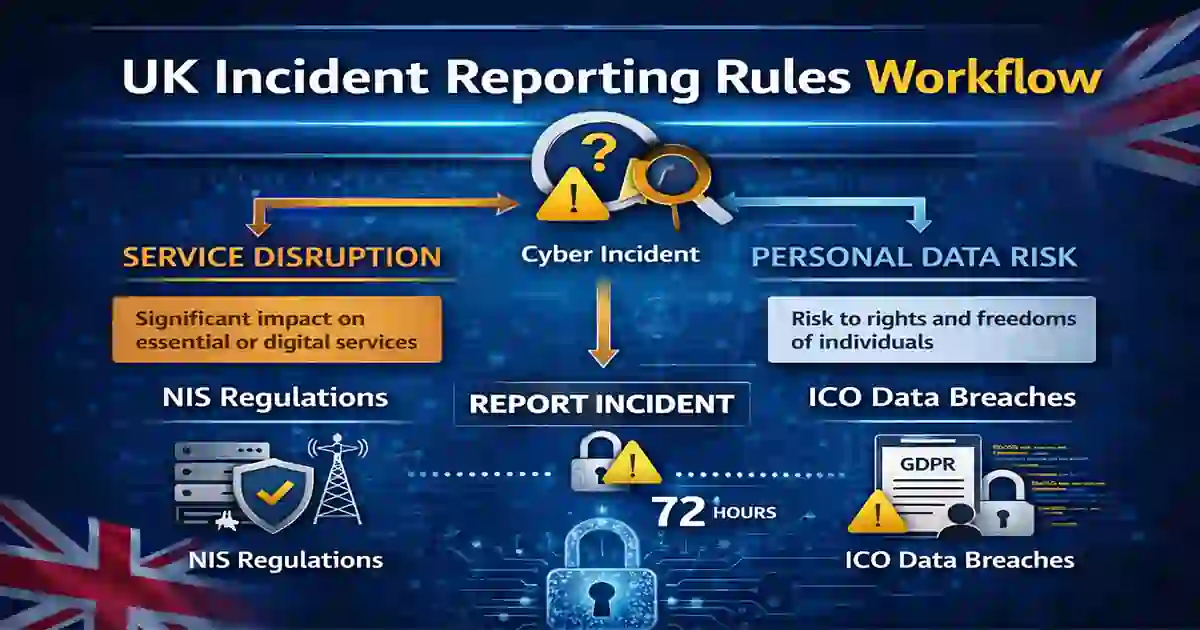
For many organisations, the difficult part is not recognising that something has gone wrong. The difficult part is working out what kind of incident it is, which regulator needs to be told, and how quickly that needs to happen. A ransomware attack may disrupt services, lock staff out of systems, expose personal data, and create supplier risk at the same time. One event can therefore trigger more than one reporting question.
That is why incident reporting is no longer just a legal formality handled at the end of an investigation. It has become part of the early response itself. Security teams need to contain the event, but they also need to preserve evidence, understand whether personal data is affected, and decide whether legal deadlines have started to run.
Table of Contents
What UK Incident Reporting Rules Cover
When people refer to UK incident reporting rules, they are usually describing several overlapping duties rather than one unified law. The most important current layers are the NIS Regulations 2018, ICO breach reporting under UK GDPR, and PECR duties for certain communications providers. The proposed Cyber Security and Resilience Bill is designed to update and expand the NIS framework rather than replace the rest of the system.
This distinction matters because the different regimes are concerned with different types of harm. The ICO is mainly focused on the effect a breach may have on individuals and their personal data. NIS is concerned with the resilience and continuity of essential and certain digital services. PECR adds another layer for parts of the communications sector. In practice, that means a single incident may have to be assessed in more than one way before an organisation knows whether it needs to notify anyone.
A useful way to think about the system is this: not every serious cyber incident is automatically a reportable personal data breach, and not every reportable event is about privacy. Some incidents are about service disruption first. Others are about personal data risk first. Some are both.

Third-party suppliers and common ransomware entry points often shape how incidents are detected, escalated, and classified during the first hours of response.
UK Incident Reporting Rules for NIS and ICO
The NIS Regulations were introduced to improve the security and resilience of network and information systems that support essential services and certain digital services in the UK. In broad terms, they require organisations in scope to take appropriate and proportionate technical and organisational measures and to report incidents that significantly affect the continuity of the service concerned. The regulations came into force on 10 May 2018.
That makes NIS fundamentally about resilience. The question is not only whether a cyberattack took place, but whether the incident significantly affected the delivery of a service that the law treats as essential or covered. A major outage at a cloud provider, a disruption affecting a transport system, or a cyber incident impacting healthcare delivery can all raise NIS issues even where personal data is not the main concern.
The ICO regime works differently. Under current ICO guidance, an organisation must report a notifiable personal data breach without undue delay and no later than 72 hours after becoming aware of it, where the breach is likely to result in a risk to people’s rights and freedoms. If the risk is high, affected individuals may also need to be informed without undue delay. The ICO also makes clear that organisations do not always need to wait for every fact to be known before reporting; details can be provided in stages as the investigation develops.
This is where many teams get caught out. A serious cyberattack may be highly disruptive but not necessarily reportable to the ICO if no personal data is involved. At the same time, a less dramatic technical event may still become reportable if employee, customer, or patient data has been exposed, altered, deleted, or made unavailable in a way that creates real risk.
That difference is one of the main reasons UK incident reporting rules need to be built into incident response planning rather than handled as an afterthought.
Why UK Incident Reporting Rules Matter
In real incidents, reporting questions often arise while the technical picture is still incomplete. A security team may know that systems have been encrypted or that suspicious access took place, but it may not yet know the full scale of data exposure or service impact. Legal and regulatory assessment therefore has to run alongside containment, recovery, and evidence preservation.
This is also why preparation matters. Organisations that already have clear escalation routes tend to cope far better than those trying to decide responsibilities in the middle of a crisis. A privacy lead should know when they are called in. Legal counsel should know when to assess notification thresholds. Senior management should know when the event has moved beyond a technical issue and into a reportable compliance matter.
Preparation is not only about legal awareness. It also depends on identity security, exposure management for internet-facing systems, and secure design choices made before an incident occurs.
UK GDPR remains central to breach notification analysis because it focuses on risk to individuals, not only technical disruption.
Where PECR Fits In
PECR is often left out of general summaries, but it remains relevant for public electronic communications service providers. ICO guidance explains that these providers must notify the ICO of relevant personal data breaches and keep a record of them. The ICO also notes that changes introduced by the Data (Use and Access) Act 2025 moved the reporting period to without undue delay and, where feasible, not later than 72 hours after awareness.
For many organisations outside the communications sector, PECR will not be the main reporting issue they face. For telecoms and similar providers, however, it is a distinct and important part of the overall framework. The practical lesson is simple: reporting obligations in the UK do not sit in one tidy box. They depend on what kind of organisation you are, what kind of incident has taken place, and what kind of harm may result.
PECR is especially relevant for providers in the communications sector, where breach reporting duties may sit alongside broader cybersecurity and privacy obligations..
What the New Bill Changes
The proposed Cyber Security and Resilience (Network and Information Systems) Bill is the main reform likely to shape the next phase of UK incident reporting. According to the government’s own factsheets, the bill would strengthen the existing NIS regime, widen the scope of regulation, improve oversight, and update reporting obligations. The official Parliament page records the bill as a government bill introduced in the Commons in the 2024–26 session, with updates continuing through March 2026.
One of the most significant proposed changes is speed. Government material says the bill would introduce a light-touch initial notification within 24 hours for significant incidents, followed by a fuller report within 72 hours. It also says the National Cyber Security Centre would be informed alongside regulators.
Another important shift is scope. The proposed model is designed to catch more harmful cyber incidents, not just events that have already caused obvious interruption. That means the direction of travel is toward earlier reporting and a wider definition of incidents worth notifying. For organisations already dealing with complex digital supply chains and hosted services, that would be a meaningful change.
The proposed reform also reflects a broader shift toward shorter initial notification windows and staged follow-up reporting. CIRCIA 72-Hour Reporting Rule,
The proposed reforms reflect a broader international trend toward faster initial notification and more structured follow-up reporting after significant cyber incidents.
For readers, the key point is that the bill would move UK reporting expectations toward earlier warning, broader scope, and closer regulatory coordination. Wikipedia’s article on computer security
UK Incident Reporting Rules Checklist
The most practical way to deal with UK incident reporting rules is to treat them as one coordinated internal workflow. When an incident occurs, the organisation should first establish what kind of event has taken place. Is it primarily a service disruption, a personal data breach, a communications breach, or some combination of all three?
The next step is to check whether the organisation falls within the NIS framework or any sector-specific regime. At the same time, it should assess whether personal data is involved and whether the breach is likely to create a risk to individuals’ rights and freedoms. If so, the ICO reporting threshold may already be in play. The organisation should also preserve evidence, document the decision-making timeline, and keep a record of why it decided to notify or not notify. ICO guidance emphasises the importance of keeping those records even where a breach is ultimately judged non-reportable.
In practice, the organisations that handle this best are the ones that prepare before anything goes wrong. They assign ownership in advance, build legal decision points into their incident playbooks, and run exercises that test both technical and reporting responses. By the time a real event occurs, they are not inventing the process from scratch.
UK Incident Reporting Rules Checklist for Teams
For operational teams, the lesson is straightforward. Reporting should not begin after the technical investigation is over. It needs to begin while the investigation is still unfolding. Security teams, privacy teams, legal counsel, communications staff, and leadership all need to know how they fit into the same response model.
Teams respond more effectively when incident timelines, escalation routes, and technical investigation steps are already documented before a real event occurs.
Common Mistakes to Avoid
One common mistake is assuming that every serious cyber incident must automatically be reported to the ICO. That is not the legal test. The real issue is whether a personal data breach has occurred and whether it is likely to result in a risk to individuals’ rights and freedoms.
Another mistake is assuming that one notification solves everything. In reality, a single event may need to be assessed separately under resilience rules, privacy rules, and sector-specific duties. A further error is waiting too long for complete certainty before taking advice or preparing a report. The ICO’s own guidance recognises that full detail may not be available within the 72-hour window and allows organisations to provide information in phases.
These mistakes are rarely caused by bad intentions. More often, they happen because the organisation has not already connected technical response and legal reporting into one process.
Final Takeaway
UK incident reporting rules are best understood as a layered reporting environment rather than a single law. NIS focuses on the resilience of essential and certain digital services. The ICO focuses on personal data risk. PECR adds duties for parts of the communications sector. The proposed Cyber Security and Resilience Bill points toward faster and broader reporting in the near future.
For most organisations, the most effective response is not to memorise each regime in isolation, but to build one internal process that maps them together. That makes it easier to classify incidents quickly, preserve evidence properly, notify the right authority, and avoid missing an important deadline when a serious cyber event occurs.