KEV vs CVSS Patch Priority: 7 Critical Facts
If you are comparing KEV vs CVSS patch priority, you are asking one of the most important questions in vulnerability management. The difference is simple but critical: the CISA Known Exploited Vulnerabilities Catalog tracks vulnerabilities known to be exploited in the wild, while CVSS is a framework for describing vulnerability severity and characteristics. CISA explicitly says organizations should use KEV as an input to vulnerability prioritization, while NVD says CVSS is commonly used as a factor in remediation prioritization.
This KEV vs CVSS patch priority guide helps security teams focus on the vulnerabilities that deserve action first. For most teams, the real challenge is not understanding what KEV and CVSS are in theory. The challenge is deciding what to patch first when the backlog is full, the staff is limited, and the scanner dashboard is overflowing with high scores. CISA’s guidance strongly points teams toward prioritizing known exploited vulnerabilities because those issues are already causing immediate harm.
The best answer to KEV vs CVSS patch priority is usually not “pick one and ignore the other.” The better answer is that known exploitation should usually outrank raw severity when immediate patch order is the goal, while CVSS helps sort the rest of the queue using technical severity and context. That approach lines up with how CISA treats KEV and how NVD and FIRST describe CVSS.
For internal site structure, this article fits naturally with your live pages on Cybersecurity Metrics, Metrics Comparison, Board-Level Cybersecurity Metrics Guide, and MTTD vs MTTR vs MTTC vs Dwell Time.
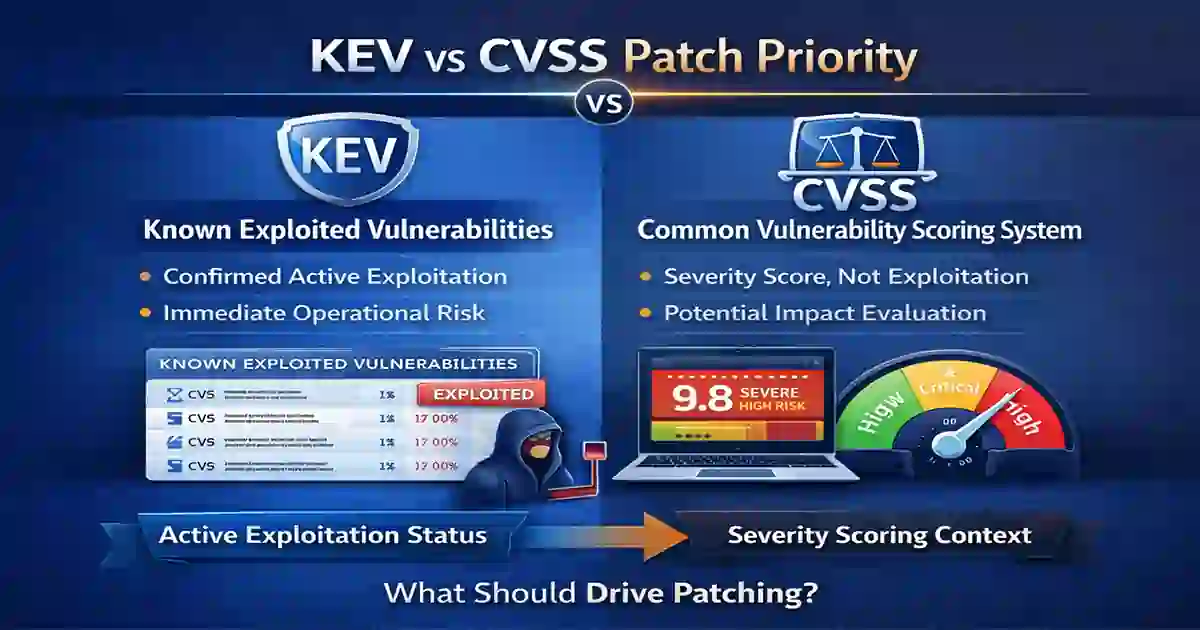
Table of Contents
What is KEV?
KEV stands for Known Exploited Vulnerabilities. The CISA KEV Catalog is a curated list of vulnerabilities that CISA says are known to be exploited in the wild and pose significant risk. CISA also says the catalog is the authoritative source for vulnerabilities exploited in the wild and should be used as an input to vulnerability management prioritization.
KEV matters operationally because of Binding Operational Directive 22-01, which requires Federal Civilian Executive Branch agencies to remediate KEV-listed vulnerabilities by due dates set by CISA. Even beyond federal agencies, CISA strongly urges all organizations to prioritize timely remediation of KEV vulnerabilities.
In simple terms, KEV is not about what could happen in a worst-case scenario. It is about whether attackers are already using the vulnerability successfully in real environments. That is why KEV usually deserves urgent attention in any KEV vs CVSS patch priority discussion. This section also pairs well with your internal Compliance & Reporting and Cybersecurity Incident Response Timeline.
What is CVSS?
CVSS stands for Common Vulnerability Scoring System. FIRST says CVSS is an open framework for communicating the characteristics and severity of software vulnerabilities. In CVSS v4.0, the framework uses four metric groups: Base, Threat, Environmental, and Supplemental.
The National Vulnerability Database says CVSS is commonly used to assess vulnerability severity and as a factor in remediation prioritization. NVD also says the CVSS specifications are owned and managed by FIRST, and its official support note says CVSS v4.0 was released on November 1, 2023 with increased granularity and a new Supplemental metric group.
The key limitation is that CVSS is a severity framework, not a direct source of confirmed exploitation status. A vulnerability can have a very high CVSS score and still not be actively targeted today. That is why teams that rely only on score often make weaker prioritization decisions. This section also connects well with your internal Cybersecurity Metrics and Metrics Comparison.
KEV vs CVSS Patch Priority: Main Difference
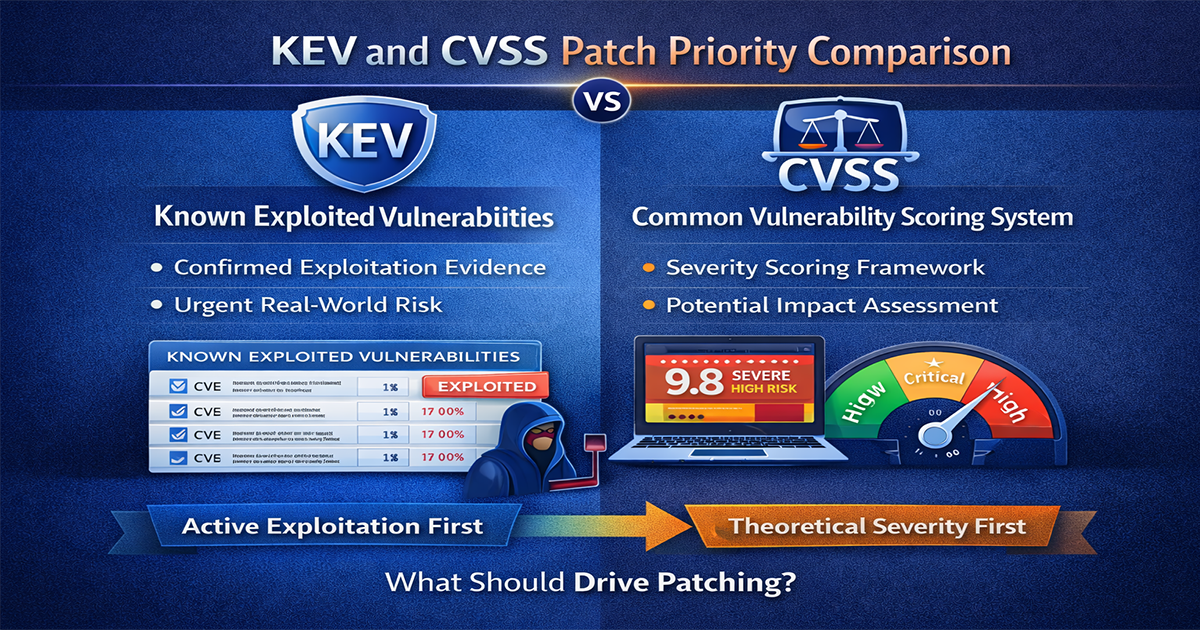
The core difference in KEV vs CVSS patch priority is clear: CVSS measures severity, while KEV reflects known real-world exploitation. Those are different signals, and security teams often weaken patch prioritization when they treat them as interchangeable. FIRST defines CVSS as a severity framework, while CISA frames KEV as a direct input for prioritization because those vulnerabilities are already being exploited.
A very high CVSS score does not always mean “patch this first.” If there is no sign of exploitation and the affected asset has limited exposure, it may not be the most urgent item today. By contrast, a KEV-listed issue may deserve immediate action even if its score is not the highest on the dashboard, because the attacker relevance is already proven. The KEV vs CVSS patch priority decision becomes clearer when teams separate real-world exploitation from theoretical severity.
That is why KEV vs CVSS patch priority is really a comparison between threat-driven patching and score-driven patching. Mature programs use both, but they do not let score alone decide what gets fixed first. This section also fits naturally with your internal Board-Level Cybersecurity Metrics Guide and Dwell Time vs MTTD.
7 Critical Facts About KEV vs CVSS Patch Priority
1. KEV is about exploitation, not just severity
The CISA KEV Catalog says it is the authoritative source for vulnerabilities known to be exploited in the wild. That makes KEV a stronger signal of immediate attacker relevance than severity alone.
2. CVSS is essential, but not enough by itself
FIRST says CVSS communicates vulnerability characteristics and severity, and NVD says it is commonly used as a factor in remediation prioritization. The important phrase is a factor, not the only factor.
3. KEV usually deserves faster remediation SLAs
BOD 22-01 requires federal agencies to remediate KEV vulnerabilities by due dates set by CISA. That shows how seriously known exploitation is treated in practice.
4. A high CVSS score does not automatically mean first priority
A vulnerability can carry a high CVSS score and still be less urgent than a KEV issue if there is no evidence of active exploitation and the affected asset has limited exposure. That is an inference from the different purposes of CVSS and KEV.
5. CVSS v4.0 improves context, but does not replace KEV
FIRST says CVSS v4.0 includes Base, Threat, Environmental, and Supplemental groups, and NVD’s support note says it provides increased granularity. But richer scoring still does not equal confirmed exploitation evidence.
6. KEV should be an input, not your whole program
CISA explicitly says organizations should use KEV as an input to their prioritization framework. That means asset criticality, exposure, business importance, and compensating controls still matter.
7. Patch priority should be threat-informed, not scanner-led
If your patch process is driven only by the biggest red score in a dashboard, you are likely over-focusing on theoretical severity and under-focusing on attacker behavior. That conclusion follows from how CISA frames KEV and how NVD frames CVSS.
This section also supports internal links to SOC Efficiency Metrics 2026, How to Reduce Cybersecurity Detection Time, and How to Reduce Cyber Breach Detection Time.
What Should Actually Drive Patch Priority?
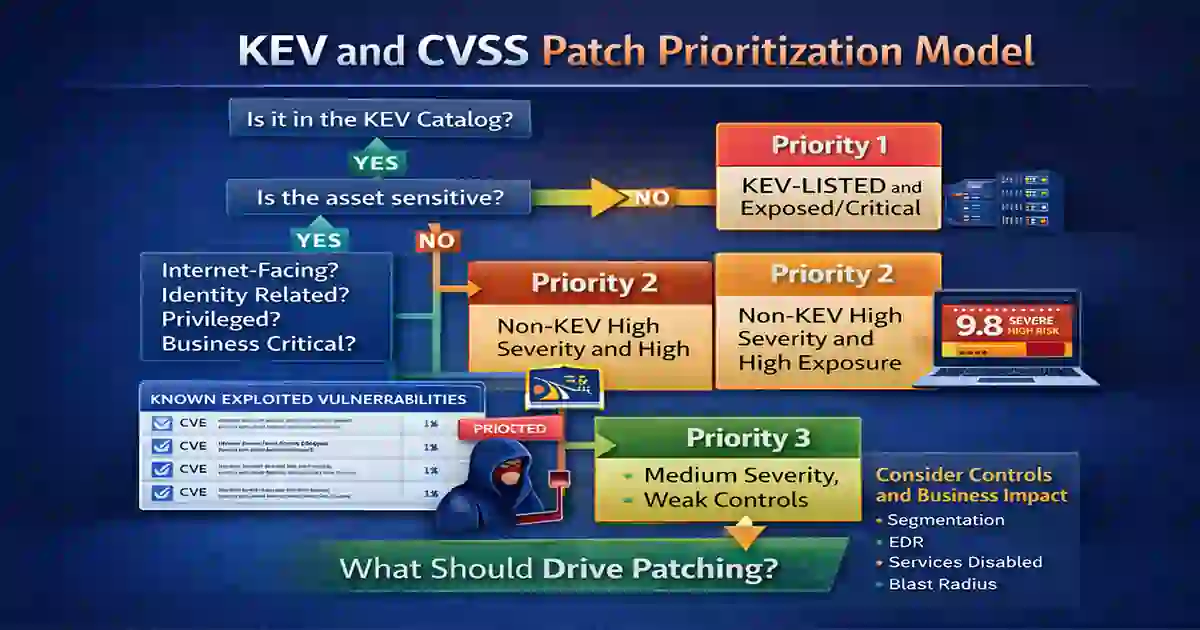
The best answer to KEV vs CVSS patch priority is not “KEV only” or “CVSS only.” A stronger answer is that patch priority should be driven first by known exploitation, then by exposure, asset criticality, and business context, with CVSS shaping the severity layer. CISA says KEV should feed prioritization, and NVD says CVSS is a factor in remediation prioritization.
A practical workflow is simple. First, ask whether the issue is in KEV. Second, ask whether the asset is internet-facing, identity-related, privileged, or business-critical. Third, use CVSS to refine urgency and exploit conditions rather than to override exploitation evidence. Fourth, consider compensating controls like segmentation, EDR, WAF, or disabled services. Fifth, evaluate the operational blast radius of delay. A strong KEV vs CVSS patch priority model should combine exploitation evidence, asset exposure, and business impact.
That model is stronger than relying on raw score alone because it aligns patching with actual attacker behavior. It also fits naturally with your internal MTTD vs MTTR vs MTTC vs Dwell Time, Average Time to Detect Cyber Attack, and Cybersecurity Metrics.
A Smarter Patch Prioritization Model
A smart patch model can be summarized like this: Priority 1 for KEV-listed vulnerabilities on exposed or critical systems, Priority 2 for non-KEV vulnerabilities with high severity and high exposure, Priority 3 for medium-severity issues on important systems with weak controls, and Priority 4 for lower-risk issues with limited exposure and strong compensating controls. This is not a single official standard, but it is a practical synthesis of how CISA, NVD, and FIRST frame prioritization.
This kind of model also improves executive reporting because leaders care more about reduced exposure and real risk reduction than about raw vulnerability counts. A KEV-informed patching story is easier to explain to leadership because it ties remediation to known attacker activity. Before setting remediation SLAs, review this KEV vs CVSS patch priority comparison against your actual environment and threat exposure. This section also pairs well with your internal Board-Level Cybersecurity Metrics Guide and Industry Benchmarks 2026: Critical Response Insights.
Final Verdict
When comparing KEV vs CVSS patch priority, KEV should usually drive first-priority patching when present because known exploitation is a more urgent and actionable signal than theoretical severity alone. CVSS still matters, especially for sorting the rest of the queue and understanding technical severity, but it should not be the only driver of patch order.
The most effective patch programs are not scanner-led. They are threat-informed, asset-aware, and business-aware. That means using KEV to identify urgent attacker-relevant issues, using CVSS to understand severity, and then applying environmental context to decide what actually moves first. KEV vs CVSS patch priority is one of the most important comparisons in modern vulnerability management because it forces teams to separate theoretical risk from active threat. This conclusion also supports internal links to Cybersecurity Time, Compliance & Reporting, and SOC Efficiency Metrics 2026.
FAQ
Is KEV more important than CVSS?
For immediate patch priority, often yes. KEV indicates known exploitation in the wild, while CVSS measures severity. CISA explicitly says KEV should be used as an input to prioritization.
Should we ignore high CVSS vulnerabilities that are not in KEV?
No. CVSS still helps teams understand severity and refine remediation order. NVD explicitly says it is commonly used as a factor in prioritization.
Does KEV apply only to U.S. federal agencies?
BOD 22-01 formally applies to Federal Civilian Executive Branch agencies, but CISA also strongly urges all organizations to prioritize KEV remediation as part of sound vulnerability management.
Is CVSS v4.0 enough to replace KEV?
No. CVSS v4.0 adds richer context, but it remains a severity framework, not a feed of known exploitation status.


