DORA Incident Reporting Checklist: 11 Urgent Steps
A DORA Incident Reporting Checklist is a working guide for deciding whether an ICT-related incident has become a reportable regulatory event and what a financial entity must do next. Under the Digital Operational Resilience Act (DORA), financial entities are expected not only to manage operational disruption, but also to report major ICT-related incidents through a common supervisory framework. DORA entered into application on 17 January 2025 and applies across banks, insurance companies, investment firms, and other financial entities.
For banks, insurers, and fintechs, a DORA Incident Reporting Checklist is mainly about speed and structure. A firm has to assess the incident against formal thresholds, preserve the right timestamps, and follow a staged reporting sequence that includes an initial notification, an intermediate report, and a final report. The detailed reporting deadlines are set out in Commission Delegated Regulation (EU) 2025/301, while the standard forms and procedures are set out in Commission Implementing Regulation (EU) 2025/302.
For payment firms in particular, the change also replaced older PSD2-era practice. The European Banking Authority said it repealed its PSD2 major incident reporting guidelines from 17 January 2025 because DORA introduced a harmonised reporting framework across the financial sector. That point matters because many internal playbooks still use older language even when the legal reporting logic has changed.
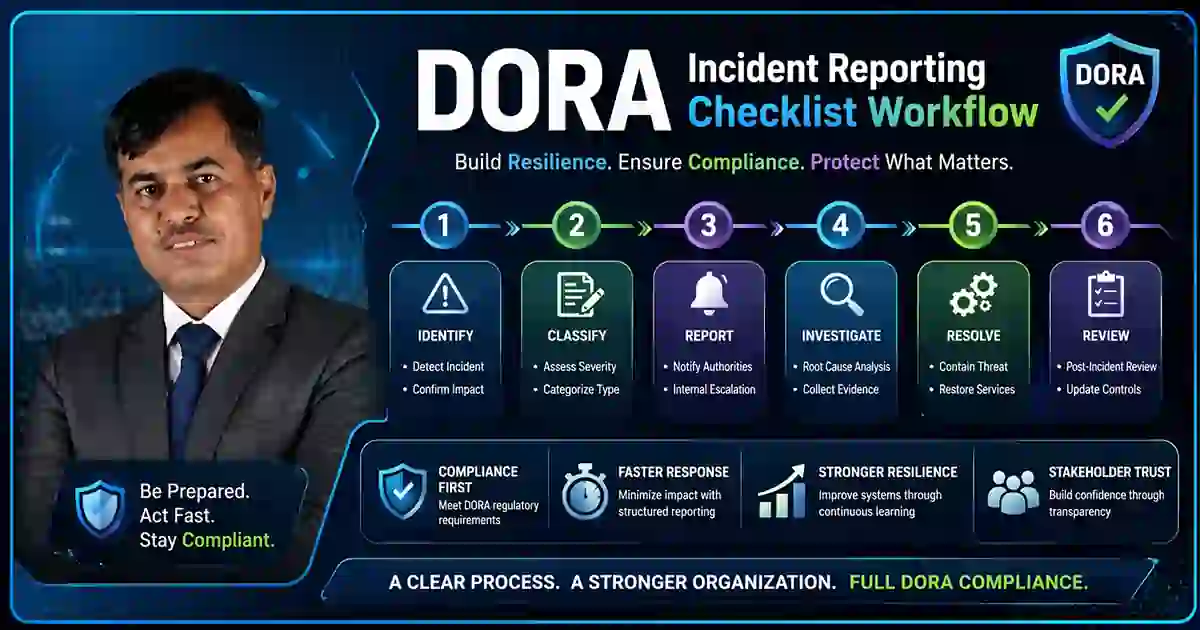
Table of Contents
Why a DORA Incident Reporting Checklist matters
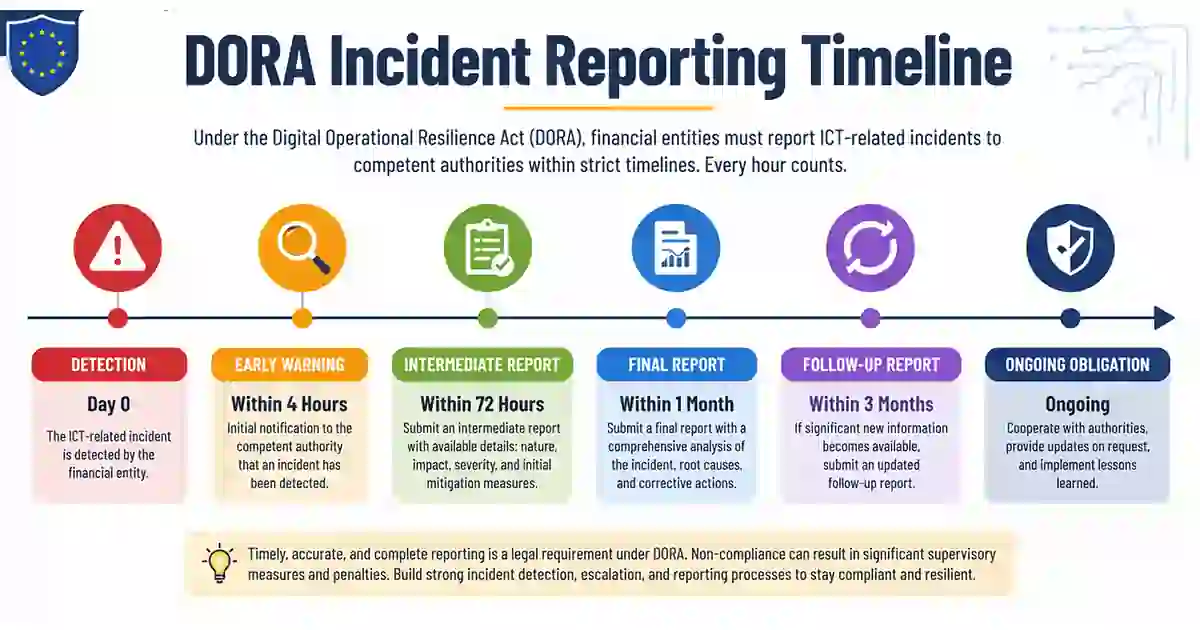
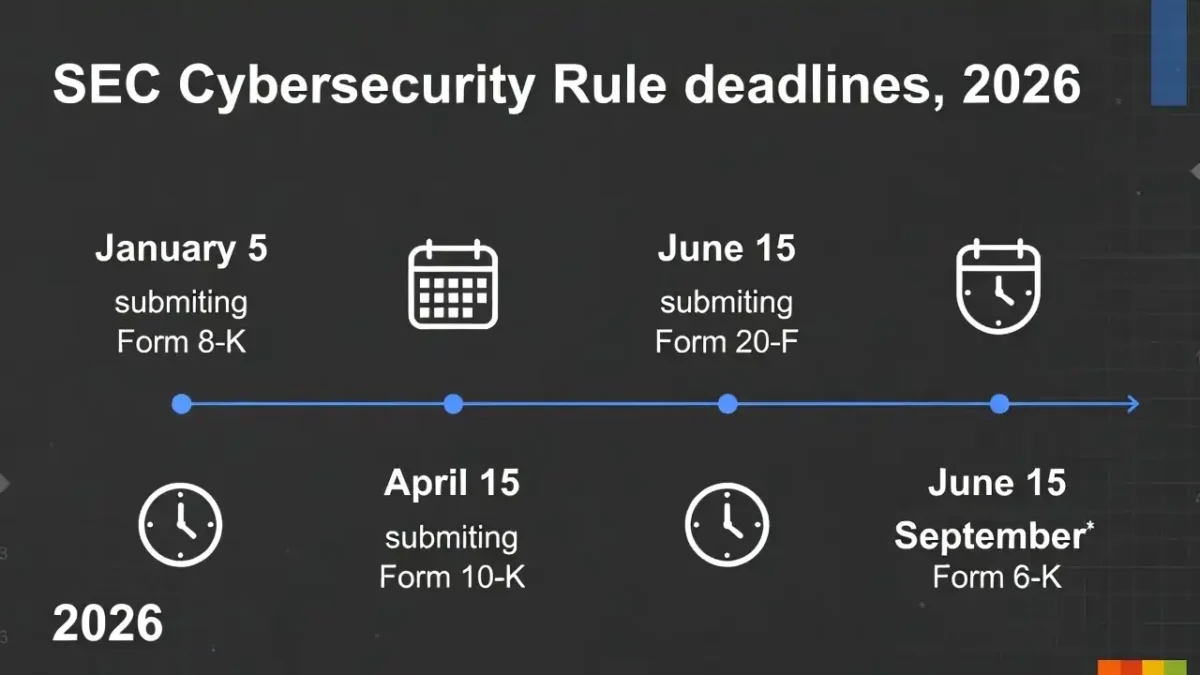
A DORA Incident Reporting Checklist matters because DORA is built around early assessment rather than late certainty. Under Commission Delegated Regulation (EU) 2025/301, the initial notification must be submitted as early as possible, within 4 hours after classifying the incident as major, and no later than 24 hours after the financial entity becomes aware of the incident. The intermediate report is due within 72 hours after the initial notification, and the final report is due no later than one month after the intermediate report, or after the latest updated intermediate report where relevant. A DORA Incident Reporting Checklist is therefore not only a legal reference. It is a timing tool.
That timetable creates a practical governance problem. A firm has to know which services are critical, who can classify an incident as major, which competent authority receives the report, and how evidence will be preserved from the opening hours of the event. That is why a DORA Incident Reporting Checklist fits naturally with related operational reading such as Finance Sector Cybersecurity Checklist 2026: 17 Urgent Fixes, Third-Party Risk Assessment Checklist 2026: 12 Proven Steps, 7 Important Patch Management SLA Template Rules, Data Breach Timeline Template: 9 Critical Response Steps, Cybersecurity Incident Response Timeline: 6 Proven Steps, and Supplier Cybersecurity Contract Template: 7 Best Tips.
DORA Incident Reporting Checklist at a glance
At a practical level, a DORA Incident Reporting Checklist should answer a small set of questions immediately. Is the entity in scope? Did the incident affect a critical or important function or a financial service that requires authorisation? Has the event crossed a threshold that may make it major? When was it detected, when did the firm become aware of it, and when was it formally classified as major? Which authority receives the report, and through which channel? A useful DORA Incident Reporting Checklist reduces delay by turning those questions into a repeatable decision path.
A good DORA Incident Reporting Checklist also separates classification from reporting mechanics. One part of the process decides whether the event is major. Another part decides who files, with which template, through which secure channel, and on what internal approval basis. Keeping those layers distinct usually makes the process faster and easier to defend later.
DORA Incident Reporting Checklist: 11 urgent steps
1. Confirm that the entity is in scope
The first step in a DORA Incident Reporting Checklist is to confirm that the reporting entity falls within DORA’s scope. DORA applies broadly across the EU financial sector and is not limited to the largest banks. A firm should not begin by assuming that DORA is a niche regime and only later check whether it applies. The safer approach is to confirm scope first and record that decision clearly.
2. Define internally what counts as an ICT-related incident
A DORA Incident Reporting Checklist only works if security, operations, legal, compliance, and business leadership use a common internal definition. Outages, security events, degraded services, supplier failures, and data compromise may all be relevant to the same regulatory decision. If teams use different labels for the same event, classification becomes slower and reporting becomes harder. This is one reason Finance Sector Cybersecurity Checklist 2026: 17 Urgent Fixes is a natural companion piece.
3. Map the major-incident thresholds before anything goes wrong
The most useful DORA Incident Reporting Checklist is prepared before the incident. Under Commission Delegated Regulation (EU) 2024/1772, the materiality thresholds include more than 10% of clients using the affected service or more than 100,000 affected clients, more than 30% of financial counterparts related to the affected service, more than 10% of the daily average number or value of related transactions, incident duration longer than 24 hours, service downtime longer than 2 hours for ICT services supporting critical or important functions, impact in two or more Member States, and economic impact exceeding or likely to exceed €100,000. The rules also give weight to data loss conditions and successful malicious unauthorised access. A DORA Incident Reporting Checklist should turn those criteria into something the incident team can actually use.
This is also where Third-Party Risk Assessment Checklist 2026: 12 Proven Steps and Supplier Cybersecurity Contract Template: 7 Best Tips fit naturally. A supplier issue can quickly turn an apparently local problem into a reportable one.
4. Record detection, awareness, and classification as separate timestamps
A DORA Incident Reporting Checklist should require separate timestamps for detection, awareness, and classification. These are not interchangeable. The issue may be detected early, understood later, and classified as major later still. If the firm collapses all three into one vague incident time, it becomes harder to show when the reporting clock started and whether the deadlines were met. The reporting acts are structured around those timing distinctions.
5. Trigger the initial notification early
The initial notification is where a DORA Incident Reporting Checklist becomes real. Under the official reporting rules, it must be sent as early as possible, within 4 hours from classification as major, and no later than 24 hours from awareness. If the incident is only classified as major after that first 24-hour period, the firm still has 4 hours from classification to notify. A DORA Incident Reporting Checklist should therefore identify in advance who can declare the incident major, who approves filing, and who transmits the report.
6. Use the intermediate report to improve the factual picture
A DORA Incident Reporting Checklist should treat the intermediate report as a real reporting stage, not a copy of the initial notice. By the time the intermediate report is due, the firm should be able to explain more about scope, business effect, response measures, and whether regular activities have been restored. This is where Data Breach Timeline Template: 9 Critical Response Steps and Cybersecurity Incident Response Timeline: 6 Proven Steps add practical value. A clean chronology makes every stage of a DORA Incident Reporting Checklist easier.
7. Build the final report around root cause and resolution
A useful DORA Incident Reporting Checklist should make it clear that the final report is not merely a closure note. It is where the firm explains root cause, recovery, dates and times of resolution, and the direct and indirect costs and losses associated with the incident. If the organisation only starts gathering evidence at the end, the final report is likely to be weaker than it should be.
8. Track losses and costs from the start
Another important part of a DORA Incident Reporting Checklist is financial evidence. Costs and losses may include external advisory fees, forensic support, overtime, replacement costs, compensation, and lost revenue. These are easier to document as the incident unfolds than weeks later. This is one reason 7 Important Patch Management SLA Template Rules belongs naturally in the reader journey. Delayed remediation often becomes visible later as avoidable cost.
9. Confirm the filing route and template in advance
A DORA Incident Reporting Checklist should always identify which competent authority receives the report, which secure route is used, what the backup route is if the normal channel is unavailable, and who owns that communication internally. Under Commission Implementing Regulation (EU) 2025/302, financial entities are expected to use the standard forms, templates, and procedures laid down for reporting major ICT-related incidents and notifying significant cyber threats. Firms should not be discovering their reporting path while the clock is already running.
10. Check for outsourced reporting and third-party dependencies
A realistic DORA Incident Reporting Checklist should make outsourced reporting visible in advance. The implementing rules note that competent authorities should know the identity of a third party reporting on behalf of the financial entity before the first notification or report is submitted. If incident facts, supplier evidence, or reporting mechanics depend on an external provider, that dependency should already be documented.
11. Check for parallel obligations immediately
A complete DORA Incident Reporting Checklist should always include a parallel-obligations check. A single incident may also raise privacy, contractual, customer, outsourcing, or law-enforcement issues. Reporting once does not necessarily finish the work. The DORA classification framework preserves separate obligations where the same facts trigger other legal duties. A DORA Incident Reporting Checklist should force the team to ask what other obligations may be running at the same time.
Common mistakes in a DORA Incident Reporting Checklist
The most common mistake in a DORA Incident Reporting Checklist is waiting for certainty before acting. Teams sometimes believe they need a complete forensic picture before they can classify or notify. DORA assumes the opposite: an early initial notification, a fuller intermediate report, and a more complete final report as facts become clearer. Another common mistake in a DORA Incident Reporting Checklist is treating classification as a legal question only, when in practice it depends on technical facts, business criticality, supplier dependency, and timing.
A subtler mistake is underestimating third-party incidents. Many firms first notice a payments issue, degraded service, unavailable platform, or customer-facing outage, not a formally labelled cyber incident. By the time the issue is understood properly, the reporting clock may already be running. That is why supplier visibility, incident chronology, and remediation governance belong close to the core DORA Incident Reporting Checklist rather than in separate documents.
Final takeaway
A DORA Incident Reporting Checklist is most useful when it works as a live operational tool rather than a document written only for audit purposes. For banks, insurers, and fintechs, the essentials are straightforward: confirm scope, define ICT-related incidents clearly, map the major thresholds in advance, separate awareness from classification, assign reporting ownership, preserve chronology, track losses early, and check for parallel obligations. In the end, a strong DORA Incident Reporting Checklist does more than help a firm file on time. It helps the organisation recognise faster, classify better, document more clearly, and explain the incident with less confusion when it matters most.